Updated: August 27, 2012
Welcome, readers. As promised, here's my review of Advanced Penetration Testing for Highly-Secured Environments: The Ultimate Security Guide, by Lee Allen, a 414-page book that teaches you how to breach networks and systems in a good and civilized manner. As a security skeptic, I sure love to take a look at this kind of works, and see whether my cynical sensory array will sounds its klaxon. Or whether we're dealing with some honest, no-nonsense hardcore hacking tips for the enterpreneuring system administrator.
On a more serious note, after having reviewed a very similar topic last year, this book comes handy, as it offers both a rather relevant comparison to another work, as well as gives me opportunity to potentially learn something new in the world of security. Anyhow, let us begin.
Overview
Quoting from the official page, the books will help you: 1) learn how to perform an efficient, organized, and effective penetration test from start to finish 2) gain hands-on penetration testing experience by building and testing a virtual lab environment that includes commonly found security measures such as IDS and firewalls 3) take the challenge and perform a virtual penetration test against a fictional corporation from start to finish and then verify your results by walking through step-by-step solutions.
This is an ambitious and risky topic. It is designed for skilled system administrators and security engineers, as well as people well familiar with the network stack and multiple operating systems. The Advanced Penetration Testing book focuses on corporate environments, so some of the stuff may not be immediately applicable at home, but the overall ideas and principles should serve you well in your quest for security, on both sides of the fence.
Chapters
Chapter 1: Planning and Scoping for a Successful Penetration Test introduces the topic, defines the limits and scope and implications of a lawful penetration testing. It elaborates on the skills, and then delves into the potential obstacles for one testing, including things and technologies like patched environments, hardening policies, DMZs, network and host-based detection and prevention systems, and more.
Next, the chapter goes into the rules of engagement, making it sort of fair. You are also introduced to measures you will be using and fighting against as a pentester. After that, there's a sizable section dedicated to installing and configuring BackTrack Linux in VirtualBox.
I found this step to be unneeded, as it's rather generic. Why not perform a physical installation, for example. A Windows host is used for this task, too. Then, you are into exploring the distribution, with some rudimentary commands that are meant to help you familiarize with Linux. But they focus strictly on how BackTrack does things, and you surely won't be an expert in Linux once you're done reading.
Finally, we start getting ready for the actual work, but again, there's another distraction looming ahead of you. The author uses an OpenOffice spreadsheet to review IP ranges we will be testing. What! What's wrong with a simple text file? And how is OpenOffice being an alternative to Microsoft Office relevant to the topic, the truth of it notwithstanding? Is this is the reason why we're installing an office suite into a security distro?
Anyhow, after that, you're taught about the MagicTree java applet for collecting and reporting, which allows imports for nmap, nessus, and other tools, etc. Using this program, we add nodes using a GUI menu and finally we run nmap. Then, you are introduced to Dradis, which I found to be completely unnecessary, including its ability to import data and create HTML reports. Perhaps these tools are the author's programs of preference, but there are many other methods you can parse data and text streams.
After this rather lengthy exposition on Chapter 1, we're into Chapter 2: Advanced Reconnaissance Techniques. This one teaches you how to scope out potential targets and grasp the layout of the environment being tested. There's some emphasis on passive recon, which means getting as much data without leaving indicators, sort of old-school intelligence gathering. There's a fancy term, and it's called Open Source Intelligence (OSINT), and the focus is on harvesting information from public databases, search engines, blogs, and similar.
The next step turns your work from passive to active. You perform footprinting, examine IP addresses and hostnames, check operating system versions, and probe for IDS/IPS technologies and network devices. The author dissects the collected intel into three phases, which pretty much are true for anything else: gather, correlate, use.
After that, you learn how to use nslookup and dig to check DNS records and automate these commands into scripts. I found the DNS introduction to be unessential to the book. If you're a hacker and need help finding out the canonical names and A records, you're in a bit of a trouble.
The chapter then goes into DNS brute forcing with fierce, using whois, banner search with Shodan, exploiting Google databases. Excuse me? Is this part of a legal penetration testing? So why it's here? And finally, how you can use smart filters and automated crawls across the Web. This chapter also gives you very long outputs of these sample tools and commands, inflating the book size. Some of the logs could have been sliced to one or two lines of text, no need for pages after pages of console text. A simple screenshot of a sample output is sufficient.
Chapter 3: Enumeration begins with an addition of a Ubuntu virtual machine to our lab. Again, there's too much focus on the machine administration, like manually setting up the IP address and then making this configuration permanent. This is irrelevant to our hacking tasks.
We warm up with a decent introduction to the nmap bundle, although some of the explanations could have been skipped, as you can easily use nmap -h or man nmap to get the same info. The author performs a handful of basic scans and plays with options like retries, timeout, SYN scan, Null scan, and others.
An interesting aspect of this chapter is how to shift blame and claim an idle zombied machine did it, by using a host with good TCP Sequence Prediction Rating. Whatever that means, you can glean the information from nmap scans. Finally, avoiding IDS systems by firing decoys is as disappointing as using the -D flag. The nmap section is wrapped with some custom scripts.
Next on the menu is SNMP and how it can be exploited, since most devices use weak community strings. The author refers to SNMP as a goldmine, and it truly is a useful source of device information. The tools at hand include snmpenum, snmpcheck, onesixtyone, and several others, which help automate and brute force your work. Some of the tools need elaborate setups like mySQL databases.
The final part focuses on enumeration avoidance techniques, if you're on the other side of the penetration
testing, using methods like port knocking, port triggers, SNMP lockdown, alerts, and more.
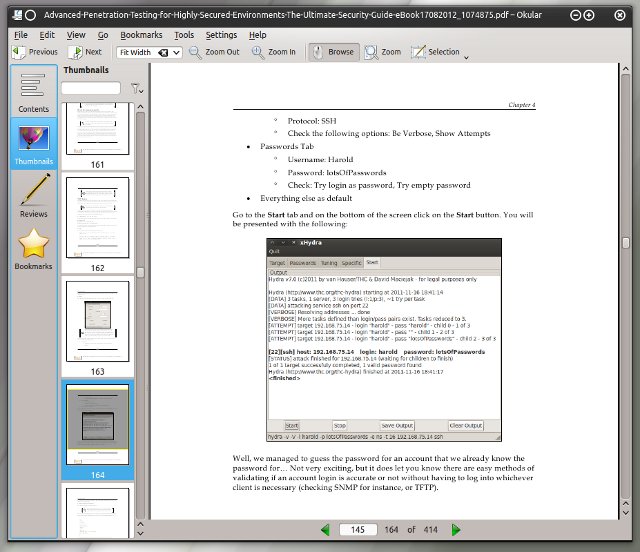
It all gets more interesting and a bit more frustrating in Chapter 4: Remote Exploitation. Again, there's a bit too much focus on adding specially crafted vulnerable hosts to our lab network. The machine has open ports, wow, how convenient. We do some scans with several tools, which feels redundant. We grab some Web banners using netcat and ncat, and I wonder why? Finally, we connect to the Web server on the exposed box and run HTTP commands. We repeat the process with smbclient.
The pentest distro used, BackTrack, comes with its own copy of the Exploit-DB online reference, which lists various vulnerabilities you can try to exploit. We search some for Samba and then compile the code. Once again, the author sidetracks into vim introduction, how to use the search and replace function therein and get rid of special characters in the exploit code. We then run the exploit and gain access and switch to root.
The next step is more confusing, as the author sets up a TFTP server for data transfer. Namely, we want to grab
the passwd and shadow files and then hack them using John The Ripper and Hydra. But why bother with the TFTP
setup? Why not use smbclient or scp to copy files? Lastly, you learn about the Metasploit framework, but the
introduction is too short to expose its flexibility and usefulness. The chapter does feel a bit
oversimplified.
Chapter 5: Web Exploitation does the same things as the previous one, with the focus on Web servers. In highly secure network, this might be your only way of ingress. Most of the chapter is dedicated to creating a vulnerable setup fr your hacking attempt. It feels too rigid and formulaic, I'm afraid.
You go through installing and configuring Mutillidae on the Ubuntu virtual machine, setting up pfSense virtual firewall and router, setting up a DHCP server, and configuring a HAProxy on Ubuntu to simulate load balancers in a potentially typical Web server environment. The setup is long and complex and creates only one very specific scenario that may be completely irrelevant to your work.
Once this is done, the author tries to detect Web App Firewall (WAF) on the target host with wafit and w3af auditing tools. The steps are performed both in console and GUI and feel somewhat redundant. One thing that becomes apparent here is that some of the screenshots should have been edited; for instance, the console is transparent and shows the distro logo beneath the console text, which can be distracting.
The middle of the chapter talks a lot about proxies, and I felt really lost here. Finally, we get to using Mantra and its Hack Firefox plugin exploit the other box. We simply run different commands that are sent to the Web server and grab stuff by using SQL injection tricks. Eventually, we manage to login, realize the users are reusing their passwords, and we gain access elsewhere.
Chapter 6: Exploits and Client Side Attacks is the best chapter of the book and the one you want to focus on. It really is the core of the book, and what makes it worth. This chapter focuses on exploits that require user interaction.
Things really start to be interesting when the author speaks about buffer overflows. Then, you're into using gdb and compiling programs with -fno-stack-protector. You also learn how to use ldd and turn ASLR on/off. We create a special program that segfaults when the input is longer than 21 characters. We then debug step by step through gdb, reading register contents and finally manage to overwrite the contents of the EIP register. I believe the author deliberately avoids the exact steps to running arbitrary commands.
After that, the book explains on fuzzing, which make memory attacks more efficient, using tools like BED, sfuzz and fast-track. Overall, an excellent piece on the core idea of how programs work and the little bugs that you can exploit. Finally, there's some basic mention of the Social Engineering Toolkit (SET), a sort of wizard for packaging click-me booby traps for the Internet-challenged users.
Chapter 7: Post-Exploitation - you are now tired. The last chapter really got the best of you, so now you're
sort of breezing through. This chapter focuses on the often overlooked aspect of pentesting, and that is what
to do after a successful project.
There's a lot of explanations on data gathering, gaining stored credentials, elevation of privilege, and
whether you're allowed to make changes or add persistence. Then, there's a long overview of important Linux
files and commands, which feels somewhat rather simplistic. Again, the thing is, if you don't know Linux, you
really shouldn't be reading this book.
A similar emphasis is given to Windows post-exploitation. Only you do not really expect people to work in
Windows through command line, so you're given a tool called Armitage, which comes with silly lightning bolt
graphics that indicate a box was compromised. I found the Windows section to lack the most important aspects,
like WMIC and PowerShell.
In Chapter 8: Bypassing Firewalls and Avoiding Detection, we work through an additional setups of the pfSense
firewall and WAN/LAN configurations. We use hping to spoof addresses and try to get past firewalled segments.
We also use the nmap firewalk script and learn how to create probes with signatures that will avoid IDS
filters. There's also some mention on a successful cleanup after taking over a box, but it is underemphasized
overall.
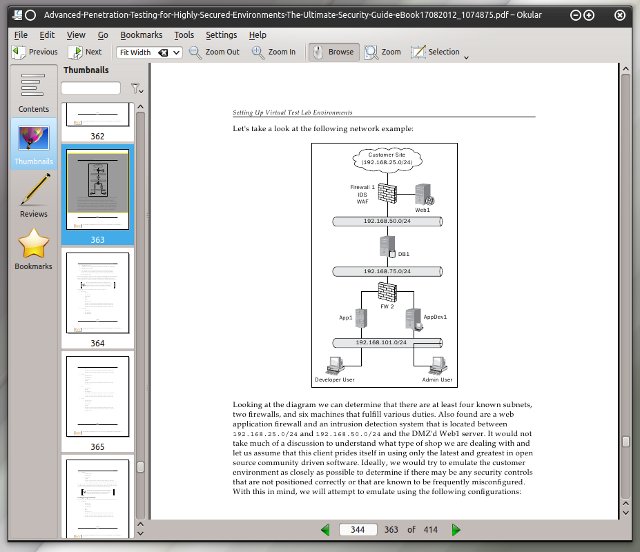
The next two chapters are a quick and somewhat unnecessary read. They feel bureaucratic, because they are, and must have been added in order to flesh out the book to its mandated size. Chapter 9: Data Collection Tools and Reporting is about proper documentation. You get a lengthy prose on the text editor battle and why vim is the one of choice. I felt the author himself was bored here. Chapter 10: Setting Up Virtual Test Lab Environments is all about using VirtualBox, options and such. Completely orthogonal to the subject at hand.
Chapter 11: Take the Challenge - Putting It All Together does come to rescue as it walks you through all you've learned and wraps the book topics. You get a scenario, there's some practice, and then you work through the challenge of probing and taking over the target box. Not bad all in all.
Conclusion
I may have sounded harsh through the article, but this is a harsh topic. Security penetration testing is an abused animal in the sensational world we live in. That said, Advanced Penetration Testing for Highly-Secured Environments: The Ultimate Security Guide, by Lee Allen is a very good book. It does have its lows and the content could have been easily shortened by about 100 pages. But it also has its strong sides.
First, it goes into much greater depth than most other works I've read. In particular, Chapter 6 is a blast, and that's how all hacking lessons should be written. Because, it's not only about security bugs, it's about all bugs. Second, the content is wrapped nicely, and you get a good sense of direction.
Overall, it gets 9/10, which is a lot for this kind of book. I was not bored, most of the time, or frustrated, and Lee Allen elegantly escapes the doomsday tone that security experts love to hear. The book's all about working through the network stack, efficiently and skillfully. True, some less virtualization focus, shorter command outputs, and maybe try to get rid of some of the more obscure options and topics, that would be my suggestion for the second edition. All in all, quite recommended.
Cheers.