Updated: March 31, 2013
Recently, I was asked to review a book named Instant Penetration Testing: Setting Up a Test Lab How-to, a relatively short piece spanning 88 pages, by Vyacheslav Fadyushin. As a tutorial, this is a focused, fast guide designed to teach you about a setup of a test lab that can be used for penetration testing scenarios, in a concise and clear manner.
I have previously reviewed several security-related works, including Advanced Penetration Testing and BackTrack 4 books, so in a way, this latest addition to the PacktPub arsenal ought to complement the earlier releases well, especially since it focuses more on the architectural side of the hacking business rather than actual methods and tricks. All right, let's see what gives.
Chapters
There are only five chapters in the book, so it's supposed to be an easy read. Moreover, the book aims at a less knowledgeable audience, so highly skilled users might scorn some of the topics elaborated here. However, the purpose of the book is to educate people only making their baby steps in the world of pentesting, on the methodology, procedure and an actual setup where testing and practice can take place.
I must admit Instant Penetration Testing begins with a very liberal opening, listing the credits of book reviewers and other miscellaneous details, that it feels somewhat academic, and might steal the focus away. Then, you get a list of requirements for your lab, revolving around the somewhat cliche VMware + Windows combo, plus some Linux for good measure.
The first two chapters are named Understanding penetration testing and Planning the lab environment. The second is marked as optional. You get the mandatory and somewhat boring theory on what penetration testing is, how it works, the law implications, and so forth.
Then, we have the lab and its components described, as well a very brief outline on what we are going to do with our servers, our workstations, and Wireless devices in our network. Personally, I found the rather detailed explanation on how to choose and setup the virtualization software for the test lab somewhat redundant. It goes into a sort of comparison between several existing solutions, while it misses several others, plus there are a few subjective inaccuracies into the pros and cons of each technology. This is a brief item, but still very much unneeded.
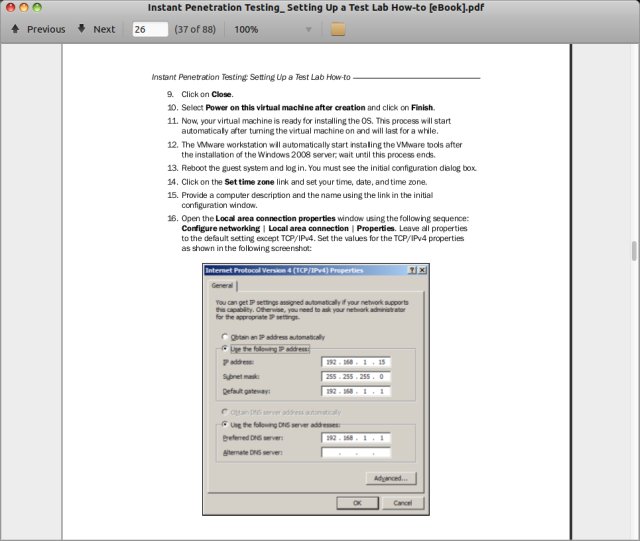
The network setup is another letdown, because the configuration is done using GUI, so this kind of defeats the purpose of building up one's so-called hacking powers. Moreover, at no point is any skill level about networking mentioned, used or explained, while it should be the core focus of the setup, because it constitutes about 90% of any pentesting exercise, and without proper understanding of the network stack, it simply isn't doable.
Much like the virtualization software, we have a setup of different Windows servers, and then the author
creates snapshots as a baseline for his testing. At this stage, you might find some confusing switches between
the first singular and plural persons, as we have both I and we used throughout the guide.
The third chapter teaches us about Web app lab setup, and it is too marked as an optional read. True to its mission, the chapter follows the simple, concise style and does not go into too many details, so if you are impatient, you will like the quick progress. However, if you want to understand what is happening beyond the step-by-step instructions, you might be a little frustrated. Speaking of steps, some of the actions seem rather confusing. For example, the author shows us how to disable Google Chrome auto-update in registry, whereas the same fix can be easily achieved in msconfig and disabling the scheduled task that runs on logon, but then demonstrates how to do the same thing in Firefox using its Options menu. Either you stick with command line & registry or do everything from the GUI, but not mix both randomly.
Moreover, quite a few things are left unexplained, so if you yearn for knowledge, this tutorial is all about the physical setup, less about being able to utilize the lab or modify it later on, because you will not have the sufficient knowledge to make calculated decisions based on the learned topics, unless you have previous experience.
Afterward, there's the XAMPP setup. It's configured very quickly with some basic rules. Then, the author setups the Damn Vulnerable Web App (DVWA), one of the many toolboxes used for pentesting education and practice. He deliberately creates a vulnerable setup with low security and access outside the localhost. Nice, but what's the point.
Last two chapters, named Setting up a Wi-Fi lab (Become an expert) and Reviewing online lab portals (Become an expert) are also somewhat confusing. First, become an expert? Really? That won't happen by following deterministic instructions in a two-hour book. Second, the purpose was to educate new users about basic configurations, most of which we do using GUI and with little focus on the actual core concepts, so the expertise question is rather tricky.
Second, the last two chapters are too short, even for this tutorial. In the Wi-Fi lab, setup, the author demonstrates using Web access to his router device, again with no discussion of network protocols, whatsoever. His screenshot of the GUI also shows two other tabs open, one with some PDF in German, another with a title in Russian. This does not seem like the best, most focused way of demoing things. There's also an extremely brief mention of free radius setup in Ubuntu, but that's just a passing remark, really.
The last section could have easily been marked as an Appendix, as it's just a list of various websites, live CD and other tools focused on penetration testing, and hardly classifies as a chapter of its own.
Conclusion
I firmly believe in the conservation of quality and knowledge. Tutorials, no matter how brief, must also include the core theoretical part explaining why and how things are being done, otherwise whoever follows the instructions will fail on the very first error they encounter. In trying to be concise and to the point, Instant Penetration Testing misses some of the point.
I liked the simple approach, and it's nice to see an attempt in helping less skilled users create a workable environment for their testing, but the book skips some of the needed steps in various setups, focuses too much on others, there's virtually no command line, and most of the stuff is done using GUI, in an inconsistent manner. This creates a problem, because if someone wants to setup their virtual environment using Xen or KVM, or maybe use a different setup, then the instructions lose some of their charm, and the guide becomes irrelevant.
Instant Penetration Testing is an okay work, but it would have benefited from some extra 30-40 pages, explaining in some details the reasoning and mechanisms behind the setup, and the instructions should all have been focused on command line, so that tests can be scripted and repeated easily. VMware as well as other virtualization tools all offer the needed command line, and servers can be installed in an automated manner. I also wish the author explained what we could do with Wi-Fi hacking, because it's an interesting topic, focused some more on network protocols, and finally elaborated on the methods a theoretical attacker might want to use. This would flesh out the existing content and give it purpose, beyond being a simple, fast guide. Priced at slightly less than GBP6.00, it's a decent bargain, but do not expect to earn magical skills after reading it. I guess 6/10. Oh, and there's going to be a giveaway soon, so stay tuned.
Cheers.