Updated: November 25, 2020
I got an interesting request (not from singles in my area). One of my readers asked me, how does one go about connecting two Linux boxes - I presume for sharing purposes. This is a topic I've touched upon frequently, but often indirectly. As Commandant Lasard from Police Academy would say, there are many, many, many, many different ways to do this.
So perhaps it's time for a proper tutorial. I will show you several common, robust ways to have two Linux systems communicate over network. We'll do it on the command line, then move up to file managers, and finally, also perform a remote data backup using a friendly GUI tool. Let's start.
Command line: SSH, SCP
The "easiest" way to connect two Linux systems is using the SSH protocol. It's convenient, secure and available on pretty much any Linux system. Now, in some remote [sic] cases, there could be interoperatibility problems due to incompatible versions of software here and there, but overall, you shouldn't have any issues.
One host acts as a server (opens TCP port 22 by default). The other acts as a client. You can use the SSH command-line utility to establish connection to the server and even run commands there, remote as local, including administrative tasks (provided you have the right permissions). Or you can use SCP, to securely copy files from the client to the server, or even retrieve files from the servers back to your client host.
SSH server setup
I'll demonstrate with a Fedora 32 server and a Kubuntu 18.04 client. First, we need to install and configure the SSH service software. While instructions may slightly vary from distro to distro, largely, what you see here is pretty much all you need. The one notable difference is the package name used to identify the SSH server - in Fedora, it comes as openssh-server. If you search for an existing sshd (ssh daemon = service), you won't get anything really.
No match for argument: sshd
Error: Unable to find a match: sshd
sudo dnf search ssh
...
openssh-ldap.x86_64 : A LDAP support for open source SSH server daemon
openssh-server.x86_64 : An open source SSH server daemon
openssh.x86_64 : An open source implementation of SSH protocol version 2
...
Once openssh-server is installed, you can start the service. Typically, it will run on startup by default, but you can also always manually start or restart it (either via the command or startup service script), however, it will not run if it doesn't have SSH keys (by which the host can be uniquely identified).
sshd
sshd re-exec requires execution with an absolute path
/usr/sbin/sshd
/etc/ssh/sshd_config: Permission denied
sudo /usr/sbin/sshd
sshd: no hostkeys available -- exiting.
We need to generate the hostkeys:
sudo ssh-keygen -A
ssh-keygen: generating new host keys: RSA DSA ECDSA ED25519
And now, openssh-server will run:
sudo /usr/sbin/sshd
ps -ef|grep ssh
roger 1832 1791 0 15:03
? 00:00:00 /usr/bin/ssh-agent /bin/sh -c exec -l /bin/bash -c
"/usr/bin/gnome-session"
root 3640 1675 0 15:17
? 00:00:00 sshd: /usr/sbin/sshd [listener] 0 of 10-100
startups
Network setup
I am going to show you how to connect two boxes on a local network. Terms and conditions apply. You will need the two hosts to be reachable (firewall et al). Opening a network port can have security implications - less so on local network, but more so on public networks, like the Internetz. However, I'm not here to discuss the security of your shi... stuff, merely to show you how to connect two boxes, in your LAN setup. However, for those most curious, you can harden SSH, including non-root access, non-default port usage, login throttling, various other restrictions, and whatnot.
Now, write down the IP address or hostname of your Linux server machine. On "modern" distros, finding the IP address isn't trivial, because netstat and ifconfig ain't cool no more, but it can be done. We will need this for the client part of the connectivity.
Command line: SSH, SCP (continued)
On the client, connect to your server. The syntax be as follows:
ssh username@hostname
So, practically, in my example, this is - notice the first-time connection warning:
ssh roger@192.168.2.107
The authenticity of host '192.168.2.107 (192.168.2.107)' can't be established.
ECDSA key fingerprint is SHA256:8Qk//cbC0v3BLuU1FQ/vjABNN34nw1sWANY+hoycHiE.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '192.168.2.107' (ECDSA) to the list of known hosts.
roger@192.168.2.107's password:
Last login: Thu Sep 17 15:03:38 2020
Now, you're "in" - you can now do things on your server. But we also want to be able to copy data to and fro. Let's use SCP then. The syntax be as follows:
scp source username@hostname:destination
The scp command also takes various useful arguments - you can recurse through folders, preserve permissions, connect to a non-default port and more. Interestingly, perhaps ironically, ssh uses lowercase p to specify the port (e.g.: -p 2222), whereas scp uses uppercase p (e.g.: -P 2223). With scp, the lowercase p is used to preserve original files modes and times. There.
scp -r /home/igor/Wallpapers/ roger@192.168.2.107:/home/roger/Pictures/
roger@192.168.2.107's password:
wallhaven-156819.jpg
100% 166KB 500.8KB/s 00:00
wallhaven-448391.jpg
100% 1606KB 3.0MB/s 00:00
wallhaven-12679.jpg
100% 501KB 5.4MB/s 00:00
...
In the example above, we recursively copy the contents of the Wallpapers directory to the Pictures folder on our server. You can always reverse the direction of the data flow (source, destination).
Unattended SSH, SCP connectivity
As you may have noted above, in my example, I was asked for a password. This is good for interactive work, but it can be cumbersome if you want to run unattended backups, like overnight scheduled jobs. To that end, you will need to configure the SSH public-private key pair. The linked tutorial explains this nicely.
Command line: rsync
The most obvious usecases for connectivity between two hosts is for data backup purposes. For example, you want to copy the home directory on your workstation to an archive server. When it comes to backups, rsync is an excellent tool for the job. Better yet, you already have a guide from your significant author, which explains how to use rsync to configure data backups.
We need to introduce the SSH component into the equation. Rsync supports SSH seamlessly. In other words, everything stays the same, except how you define the destination. The SSH/SCP syntax to the rescue:
rsync source username@hostname:destination
For example:
rsync -avs --delete -i -h
/home/igor/Wallpapers/ roger@192.168.2.107:/home/roger/Pictures
roger@192.168.2.107's password:
sending incremental file list
*deleting Screenshot_20200516-125442.png
*deleting Screenshot_20200516-125302.png
*deleting Screenshot_20200516-125252.png
...
*deleting QEMU Virgil.txt
*deleting Fedora 32.txt
.d..tp..... ./
<f+++++++++ wallhaven-122457.jpg
<f+++++++++ wallhaven-12679.jpg
<f+++++++++ wallhaven-156819.jpg
sent 11.16M bytes received 7.94K bytes 2.03M bytes/sec
total size is 11.15M speedup is 1.00
Once again, we need keys for seamless connectivity.
GUI connectivity: Dolphin file manager
Like I said, there are many different ways to do this. I will demonstrate with Dolphin, the default file manager in the Plasma desktop. It natively supports SSH connectivity, so you can basically do what we did earlier, except you now do it through the GUI rather than on the command line. I will dedicate a separate article to the finer details of Dolphin & SSH usage, so for now, here's an abbreviated version.
Dolphin uses the FISH protocol to establish connection to remote hosts. In Dolphin, hit Ctrl + L or double-click on the location line to expose the address bar, and then write:
fish://username@destination
Dolphin will now prompt for password - which you can save, and that's it. You're connected to the remote host, and you can do any which file operation (within the SSH permissions your user has and the server allows).


GUI backup: Grsync
We've talked about this before. Grsync is an excellent rsync frontend utility - my favorite. You can use it to define one or more data replication tasks, including various options and exclusions. In the destination line, you need to put in the username@hostname:destination entry, just as you would do with rsync in a terminal window.

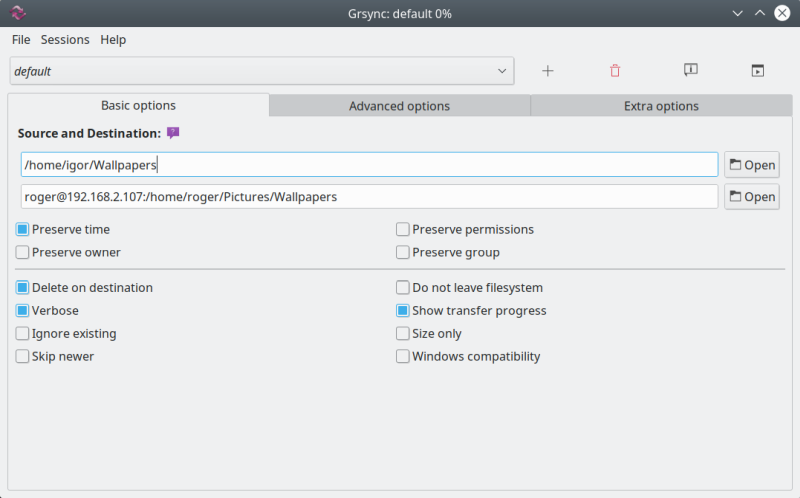
You can then simulate (dry-run) the operation, or connect for real - with the added bonus that you can save the connection credentials, so you can re-run the task without having to manually authenticate again. Perfect for scheduled data backup tasks.



Conclusion
Well, there you go. Now you have four different ways to connect your Linux machines, including command line and GUI methods, password-based and passwordless authentication, data backups, and then some. Behind the scenes, it's all SSH, but that's the beauty of it really.
I hope you find this article useful and practical. If you want to make sure you have your Linux boxen seamlessly talk to each other, you have the tools to be your own boss. For those confident with the command line, ssh, scp and rsync do the job, but if you're more keen on simple mouse point-'n'-click action, Dolphin and Grsync offer the necessary functionality. Now, the list does not end there. You can also use FTP, SFTP - or a program like wormhole, and some other Linux file managers also offer SSH and Rsync functionality, but that's a topic for another article really. And that would be all for today.
Cheers.