Updated: December 15, 2008; December 31, 2008
Is the Internet safe? What do I have to do to be safe from viruses? How can I tell a real website from a fake? All these are critical questions that less savvy Windows users ask themselves every day. And when they address these questions to their more knowledgeable counterparts, they get the following answer - use common sense.
By all means, this is a great answer. The only problem is, common sense is meaningful only when the decision maker has enough prior knowledge and experience to rely upon. Otherwise, it is a wild guess. Thus, while it may seem rather astonishing that so many Windows users would repeat their mistakes and fall for the same tricks all over again, it is in fact perfectly normal. Unless explicitly taught and explained what should and should not be done, their attempt at "common sense" will always be flawed.
Luckily, mastering the basic principles of common sense in regard to the Internet can be a rather simple and even pleasant task. You can reach a sufficient level of proper Web behavior in just a few elegant steps.
This article is an attempt to provide the basic understanding of potential risks and the sensible solutions to avoiding them - and if exposed, to mitigating them. All of the solutions presented here require minimal knowledge and effort. So let's begin.
Table of Contents
- The choice of the browser
- Security updates (patches)
- Preventing active infections
- Preventing passive infections
- Downloads
- Security through Obscurity
- Conclusions
The choice of the browser
Most of the interaction we have with the Web is through the browser. Therefore, the choice of the Web browser should be your utmost priority. To this end, I recommend Mozilla Firefox. Firefox is one of the most successful and definitely the fastest growing Web browser available to Internet users. It is fast, stable and secure.
Firefox is being actively developed and constantly improved. Security vulnerabilities found in the browser are patched quickly. The developer even offers money rewards as an incentive to users and researchers for any vulnerability discovered in the browser. Firefox is open-source and cross-platform.
Some of the many features Firefox has are: tabbed browsing, incremental search, live bookmarks, a spell checker, an integrated search system, a download manager, It also has a built-in updater, allowing you to update your browser without any complicated procedures. Furthermore, its basic functionality can be significantly enhanced through a variety of Mozilla-approved add-ons, which can be used to enhance the security, privacy, visual performance, or productivity. There is also a portable version that can be run from a USB stick.
Why not Internet Explorer?
Internet Explorer can be a safe browser. Power users will claim that it does not really matter what you use. And this is true - for power users. For most people, this is not true. Out of the box, in its default configuration, Internet Explorer is less safe than its counterparts - Firefox or Opera, for example. Internet Explorer also has a very poor record of complying with international Web standards.
Why is Internet Explorer less safe?
Internet Explorer is less safe for two primary reasons:
ActiveX controls are applications designed to be downloaded and executed from the Web browser. While this functionality can greatly simplify the distribution of Web-rich content, it opens a huge gap in the security of the browser and the underlying operating system. Badly and maliciously coded ActiveX controls can be used to take over the system. Major Internet Explorer rivals, like Firefox and Opera browsers, do not support ActiveX controls.This brings about the second major reason. Internet Explorer runs as a part of the Windows shell and is not separate from it. This means that whatever system does, Internet Explorer does - and vice versa. In other words, Internet Explorer is an unrestricted application with system-wide access. Running malicious ActiveX controls through the browser can result in system-wide infections. To date, this has been one of the primary reasons for infections among the Windows users browsing with Internet Explorer.
Various alternatives, like Firefox (or Opera, K-Meleon and several other browsers) do not use ActiveX controls, eliminating a major vector of attack. Additionally, these browsers employ the Sandbox principle: the browser is an isolated application restricted to its installation folder; it does not have access to the system core - indeed, one of the reasons why Firefox (or Opera) can be installed to a portable drive is the fact it is not tied to the system. Thus, any potentially malicious action will be inherently restricted.
Security updates (patches)
We have mentioned earlier that running malicious code through the browser can possibly damage the operating system. Likewise, we have seen that the less tied the browser is to the system, the less likely and less severe the damage is. Nevertheless, it is important to understand how browsers can be used to infect the system. Basically, there are two types of infections - passive and active:
Active infections
Active infections are those initiated by the user. If a user downloads a file and executes it on his/her machine, this can hardly be considered a browser fault. This principle also applies to ActiveX controls for Internet Explorer users. Certain websites may offer different ActiveX controls for installation under the false premises of providing enhanced content to the user, in which case he/she may be convinced to download and install the control. This is synonymous to installing any other application. We will discuss how to interpret browser prompts and actions soon.
Passive infections
Passive infections are more problematic. As their name implies, the user is passive. In other words, the infection process takes place without direct user interaction. This means that malicious activity can take place by merely visiting a web page. Therefore, passive infections are more difficult to spot and counter if executed. On the other hand, they also require a much greater margin of error on behalf of the user and his/her system to succeed.
Passive infections are closed tied with so-called drive-by-downloads and remote execution of code. A user visits a web page that triggers a download without his/her consent. This download is then executed by the browser, resulting in an infection. Usually, the process takes places in the background, without any visible symptoms. It is also usually quite fast. Hence the term "drive-by download" - in other words, the user is challenged by hit and run tactics.
Since this method does not involve active user participation, it must rely on an existing, unpatched vulnerability in the browser and the operating system to work. If the browser / operating system contain potentially critical holes, in the right (or rather, wrong) circumstances, they can be used against the user to take control over his machine.
Therefore, making sure the system and the browser are fully up to date is the most effective measure of combating drive-by downloads. Updating your software goes a long way toward mitigating potential risks.
Again, the importance of separation between the browser and the system comes into play here. The more separate the browser is from the system, the less likely and less severe the damage. Another critical parameter is the updating policy of the browser vendor. Now, let us review more deeply the mechanism behind the passive infections:
The first step of the possible infection is to visit a malicious web page. There are many ways the user might end up opening such a page in his/her browser. This can be a mistake on behalf of the user (mystyped URL), casual browsing that leads the user to a malicious web page, a link someone sent you, or even a carefully crafted trick aimed at convincing the user that he/she should visit the page.
The goal of the malicious page is to initiate a download of a certain file. The download can be activated without user interaction only if the browser security settings are inadequate or if there is an unpatched vulnerability in its security mechanism. Otherwise, the attempt will most likely fail.
The third step of the infection is to run the downloaded file. Again, this procedure requires a hole in the browser to be successful. This brings us to several important conclusions:
- One - We can see that a connection to a server containing the malicious payload must be established for the infection attempt to work. Therefore, if the users can be taught how to avoid exposure to websites of potentially harmful nature, they can reduce the chance of infection, even if they run a vulnerable browser.
- Two - Even if the user connects to a so-called rogue server, it is quite possible that nothing bad will happen. This depends on many factors, which we will discuss soon. However, applying the latest patches is a very efficient method of combating passive infections.
- Three - Lastly, after the malicious file is downloaded, it is executed. Being able to control the execution will allow the user to prevent the infection, even if the first two security mechanisms failed. We will shortly discuss this, as well.
Preventing active infections
Active infections are all those that results from user decisions. While the simplest to prevent, they are also the most difficult. This is because it is impossible to predict the user behavior. There will always be a margin for error.
Being "safe" on the Internet requires discipline, a rather strict regime that may not suit your mood and needs. Still, there are some things can do that will not significantly impair your usability - but will go a long way toward ensuring you do not harm yourself.
To infect yourself, you need to go to a webpage that contains harmful content. If someone wants you to go there, then it is in their "best" interest to make sure you are goaded, enticed, lured, duped, tricked, or simply led to the webpages where you will be convinced to download and then install potentially malicious content. On the other hand, you can stumble across malicious content by merely browsing.
These two cases require a somewhat different approach, but the basic idea is the same: if you did not ask for it, you do not need it. This is the fundamental principle that should guide you whenever you are faced with a choice: to click or not to click. But let us elaborate.
Prompts
It is possible that while you're browsing a web page that you may be prompted to "interact" with an object on the web page. This could be a flashing alert trying to draw your attention, a popup windows or similar. In either case, if you have not initiated this activity, you should be careful when answering the prompt.
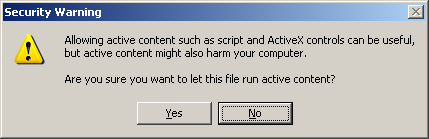
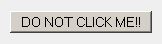
Your best bet is to simply close the "offending" prompts. If the prompts contain buttons, you should not use them to allow or deny the prompt; it is quite possible that the buttons are "fake." Your best option is to close the window by using the Task Manager (the X in the window corner might be disabled). Here's a pair of examples for Internet Explorer:
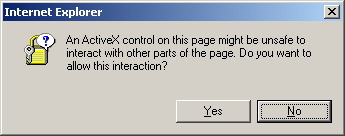
It is also possible, although extremely unlikely, that you might be prompted to install an unasked-for Firefox extension, theme or other add-on. If this happens, if you did not explicitly try to install the extension, close the prompt.
Firefox will go as far as to warn you - before you install an add-on, even if you have initiated it yourself. Here's an example, demonstrated using the completely safe and innocent Sage RSS Feed extension.
Furthermore, your machine will not display any shiny red warning if things stop working, especially not while you are browsing. The chance your machine will throw up a genuine prompt about some serious failure is extremely low. At best, your application will close and you will get an error report. At worst, your machine will crash.
Links
This is one of the most common methods of trying to take users to potentially dangerous websites. You will find links everywhere. Usually, links are accompanied by explanations, briefly telling you of what you may expected on the destination page. You may not want to click on just about any link you find, especially if you're supposed to do something personal or important. Plus, there is always the chance you may be led to a specially crafted page that will try to take advantage of you in some way, whether through an infection or social engineering.
If you are a savvy Internet user, you will probably be able to dismiss the tricks without thinking. Still, quite a few people take alerts, prompts and shiny red warnings too seriously. Here are several guidelines that should help you better understand when not to click:
- One - There is no such thing as a free meal. Well, there is, but not on the Web. No one will give you money if you just install this or that. No Nigerian general's daughter will give you her millions. You did not win a lottery. Simply disregard any "incredible" offer, no matter how well designed it may be. Do not click on links that promise to take you to wonderland.
- Two - You may also be enticed to check your system for errors, viruses or whatever. Again, your browser does not have the ability to perform any such activity and cannot inform you of any system errors. Therefore, any such link inside web pages is an attempt to draw your attention and possibly "force" you to click on a link.
- Three - Links embedded in mails or Instant Messaging (IM) sessions should be treated with care. Do not follow links if you received them from people you do not know. Even if you receive links from people you do not and supposedly trust, you should still avoid clicking on links. If you must see what's behind the sent link, COPY it into the browser address bar.
- Four - Think before clicking. If you receive an email - or any other form of message - telling you should login in to a certain website and approve, check, validate, or confirm your personal data, you should NEVER do this.
This is why:
- Ask yourself if the message is relevant. An email with the Subject: Your website is completely irrelevant for someone who has never had a website. So why click on such a link?
- Almost every single scam message is generic: the subject, the addressee and every other supposedly identifying information will always be in the form of you, your site, your country etc - never personally addressed to you specifically (e.g. Roger Bodger).
- Never trust the sender's name or email; they can be easily forged.
- Websites like Paypal (and probably every bank in the world) will NEVER ever send you emails asking you to confirm your credentials. They have them, they do not need a confirmation.
While most of the above pertains to mail messages, the strategy is valid for any kind of message & link. If you are using webmail, then you are going to interact with mail messages through the browser.
The same principle applies to images, archives, documents, and executables someone might send you. Even if the sender is a close friend whom you trust, you can never be 100% sure that he/she has not accidentally sent you a file containing potentially malicious code.
Treat all and any external content with care, especially if you intend to execute it on your machine. Forethought and prevention are much cheapter than lengthy recovery or malware cleaning procedures. For more about how to handle files, see the Downloads section below. We will discuss mail security in a separate article.
Secure sites
If you need to connect to a website that advertises a secure (encrypted) connection and you may be require to provide your personal data, there are two things you should do to ensure the integrity of the connection:
- One - Do NOT use links to reach the desired site. Links can be altered to appear to point to a certain website, while in fact pointing to a bogus site designed to look like your destination. Always access the confidential websites directly. If you are not sure what the website address is, phone the relevant offices.
- Two - Make sure the connection is encrypted and digitally signed by a Certificate Authority. You will know if this is true by visual clues displayed by your browser. The clues include the https:// prefix in the address bar and additional information (including some sort of a secure connection icon).
Here are example for three browsers: Internet Explorer, Firefox and Opera:
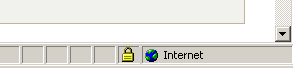
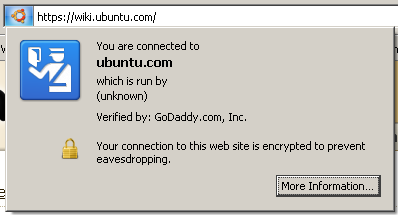
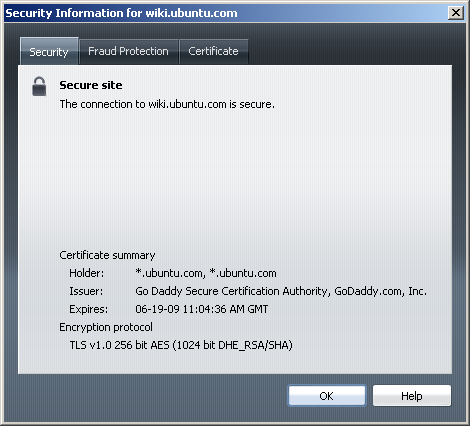
You may also notice that Firefox and Opera display additional information for the secure sites. This is because they have built-in anti-fraud and anti-phishing functions, aimed at preventing abuse of confidential data.
You should never accept secure connections to self-signed web sites for the purpose of any personal data transaction. Likewise, you should be extremely careful about expired certificates or ones with mismatched domain names. Here's an example (from my Apache book chapter) - please note this example is NOT associated with the website ourserver.com, whether it exists or not:
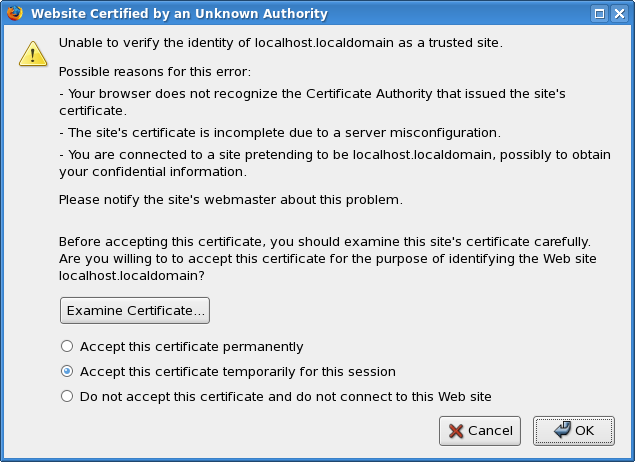
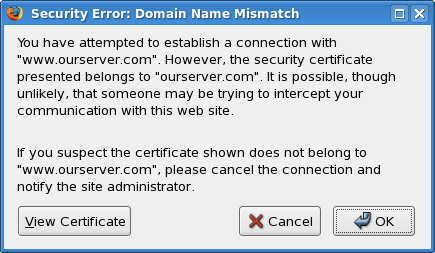
If your bank site throws up an error like this, do not proceed with the login! Contact your bank and inform them of the potential security breach.
Updated: Firefox 3 SSL spoofing
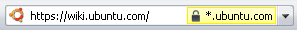
Firefox 3 changes the way validated secure web sites are displayed to the user. The yellow bar is gone, replaced by a color icon left of the address bar. This area is also used by websites to display their favicons.
In theory (and practice), a malicious website might use a solid color favicon similar to Firefox certification validation color codes to try to fool users into thinking they have connected to a safe website.

Please read this highly useful Blog entry for more details, as well as methods how to prevent this seemingly innocent feature from accidentally confusing you. Many thanks to tlu for pointing this out!
If you must use your computer (most likely laptop) in "untrusted" locations, like airports or Internet cafes, I strongly recommend you postpone any confidential activities for later.
Preventing passive infections
By itself, HTML, the language of the World Wide Web, is a static language. It is used to display content. HTML cannot be used to setup dynamic web pages, which allow the user to interact with the content. To this end, different "active" languages are used.
The active content of web pages can be divided into two sections - the server-side and the client-side. The server-side content is executed on the remote server that present the web page to the user. The client-side content is executed on the user's computer, inside the browser. This is where the trouble begins, so to speak.
Different browsers use different methods to handle the active content, but the most prevalent method is the use of the JavaScript language. JavaScript is neither harmful nor good. It is a language, just like any other (C, Python etc). The purpose of the JavaScript code (written into blocks called scripts) is to allow interaction between the user and the content.
The scripts are read and executed (parsed) by the browsers' JavaScript engines. By default, these engines do not allow the scripts to be able to read or write to hard drives on the user's computer. The entire experience is restricted to the browser space.
However, if and when vulnerabilities in the browser engines are found, they can and are used to break outside the browser space and tamper with files on the local system. This phenomena are usually called buffer overflows.
Buffer overflows allow malicious web pages to initiate downloads and execute content without user content and impact the system. Running a fully patched browser means a fully patched scripting engine. The same principle applies to other languages, like Java, Flash etc.
Internet Explorer
Now, Internet Explorer is one step more problematic than other browsers, because it has yet another language that it uses and that is particular to its rendering engine - the ActiveX. But that is not all.
What makes ActiveX so powerful, useful and yet so dangerous is the fact that ActiveX controls can interact with the local system. Unlike JavaScript, Java and other scripts, which are limited by design, ActiveX controls are not. They can touch any and every part of the system.
This is the principal reason why Internet Explorer is the most widely targeted browser in the world. Its inherently weak security principles make it so much easier to write and successfully deploy malicious code. All right, now we understand where the trouble comes from. The question is, how to prevent it?
Damage control
We have mentioned three major reasons for passive infections - URLs, bad security before and after the download. Let us see how we can minimize the risk for each.
Locating the malicious content
I have already written an article called 'The Internet won't hack you unless you provoke it,' which explains that it is often the users who come looking for trouble, rather than the other way around. Visiting a page with malicious content can take a lot - or very little - effort, depending on the user's security practices.
Deliberate pursuit after malware
Quite a few Internet users like to explore the so-called "dark" side of the Web. This dark side is epitomized by the cracks and warez websites. Whether the existence and the purpose of these website is illegal is completely beside the point. They attract huge crowds of visitors from all over the world, making them suitable for hosting malicious code, both in the web pages and the downloadable content.
Legal questions aside, if you must visit this part of the Web, you should be aware that you might encounter potentially malicious content, probably in somewhat higher percentage than if you were to stick with news, forums and gardening sites.
While the goal of this article is not to educate you on the facets of the cracks and warez sites, you should also be aware that there is varying quality of customer satisfaction to be had, so to say. This means, make sure you know where to go and what to do. We will discuss downloads a little later.
It is also possible that the user might accidentally stumble across a malicious page in his/her innocent pursuit of fun on the Web. Legitimate sites are rather frequently compromised, becoming hosts of malicious content and serving it to unknowing users. This means that you should always treat online content with some care. There is no need for fear or paranoia, though. We will talk about this soon.
If you come across malicious content, your browser, and possibly additional security tools, should keep your safe. It is rather impractical to place the security in the hands of the user. Sometimes, spotting trouble might be easy and obvious; other times, it might not. Then, different levels of skill, knowledge and experience among users also contribute to the potential outcome.
An efficient set of security mechanisms should keep the user safe from passive infections without any interference and possibly even without notifying the user.
Initiation of these downloads depends on the level of security settings in the browser. As said before, by default, Firefox has a higher default security level than Internet Explorer. If you must use the latter, then you should consider raising the default level of security in your browser - or, at the very least, not lower it!
Configuring a custom level of security in Internet Explorer requires lots of knowledge and is not a flexible practice; you do not have the ability to easily configure per-site policies. The Zones are meant to do this, but they still require that you manually input each website to the relevant category.
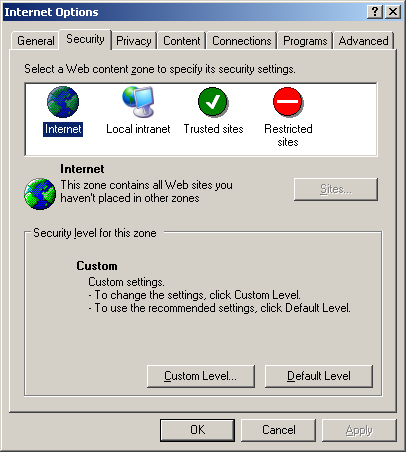
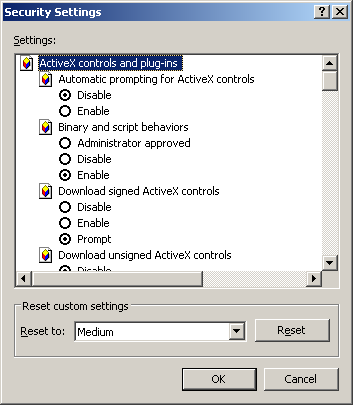
As you can see, you need to be able to understand what each section means to achieve a good mix of control and usability. The most prudent choice is to switch to an alternative browser. Still, if you must visit websites that you know could be "dangerous," then you should at the very least set the security level to High for the duration of your adventure.
If you are using Firefox, you're not likely to experience this phenomenon. However, if you are using Internet Explorer, you might come across drive-by downloads now and then. Should a file be downloaded to your machine and be about to be executed, having the following two tools will significantly enhance your security:
- Anti-virus - while not exactly the mother-of-all solutions to Web dangers, an anti-virus (updated, of course!) can be useful in discovering and neutralizing malicious files on your machine, including freshly downloaded code about to run. The anti-virus might not be able to spot every single infected file or prevent every single execution, but for most people, it is better than nothing.
- Firewall - while running this tool properly does require some knowledge, if properly configured to monitor outbound connections from the local computer to the outside world (remote servers), a firewall can intercept attempts by downloaded malicious program to contact its parent server, whether to download yet other programs or, even worse, send out information collected from your computer. You might be infected, but at the very least, the threat will be somewhat contained.
Of course, the goal is to stay uninfected, in which case you do not need to worry about unsolicited, undesired outbound connections - or worry about your anti-virus flagging files as malicious.
Firefox
How does Firefox fit into this picture? Practically, all of the above advice applies to Internet Explorer. As a Firefox user, you will probably never see or experience a drive-by download. The combination of quick patches, a much more robust design and no ActiveX controls means that your browsing experience should be rather uneventful.
This does not mean that you should throw caution to the wind or bait "hackers" into compromising your system. A good security policy is one maintained regardless of the platform and browser used.
Nevertheless, Firefox security can be boosted by several orders of magnitude through the careful use of some of its security extensions (add-ons). These extensions allow a fine-grained, per-site control of active content, allowing you to display and run active content only on the websites you trust, and even then, only some content and just temporarily, if you like.
The most efficient security extension for Firefox users is the Noscript extension. While it is impossible to explain its so many excellent features in this article, a brief description is in order. Noscript will prevent scripts of any kind from running on any page, by default. This means that no active content can ever run - and all you will see is the static and harmless HTML. On many pages, this will result in some functionality being broken, but the lost extras can be easily restored.
Noscript installs an icon into the status bar of the Firefox browser, allowing you to bring up an options window with a single mouse click. Here, you can decide whether to temporarily or permanently allow scripts to run on the relevant web page. Through the advanced options, you can even configure how individual plugins are controlled.
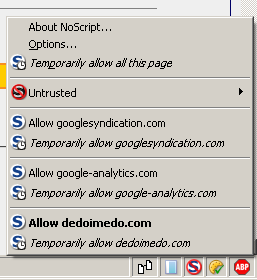
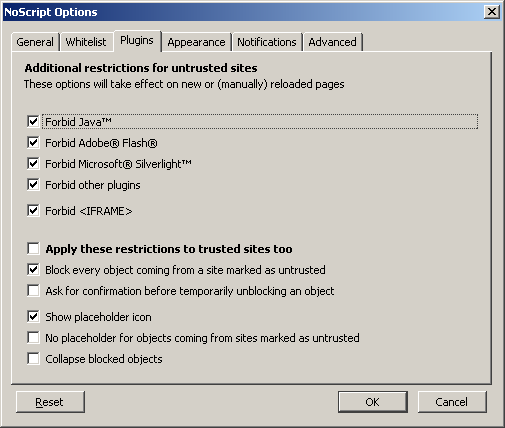
Using Noscript when visiting webpages that are likely to contain potentially malicious content is a very sound security practice.
Isolating the browser further still
Please note that this sub-topic is for advanced users. It is only briefly introduced here and will be reviewed in detail in a separate article. So ... Even though Firefox is secure, it can be made even more so. And so can Internet Explorer. Or any other browser.
Most Windows users run full, unrestricted administrator accounts, allowing any application running on top of this account to perform practically anything. If you take away the admin rights from the user, you reduce the exposure vector significantly. This can be done in two ways:
- Run the administrator account - but restrict Internet applications (like the browser, mail client, IM client etc).
- Run the limited account. For more details about how to setup the limited account on Windows XP, please refer to my article Installing Windows XP - Page 6.
Running a limited account is an efficient method of battling browser vulnerabilities. But this method may not suit everyone. Instead, some users might prevent to restrict only the browser, so that if its default security is somehow defeated, the damage will be localized.
There are many applications that specialize in stripping privileges from Internet-aware programs and forcing them to run in highly restricted modes. I would personally recommend DropMyRights. You can find more details about it in my article: A (sweet) collection of Windows programs. Another useful application is SandboxIE.
Both of these adhere to the sandbox principle. In the case of Firefox, the choice might be slightly redundant, but it is quite useful for Internet Explorer.
And then, you can also combine either method with additional functions, like Group Policies and Data Execution Prevention (DEP). For more details about Group Policies, you may want to read another of my articles - Group Policies - Beginners' Guide. We will talk about DEP separately.
Summary of how to prevent passive infections
Let us see what we can do to avoid passive infections:
- Use a good browser, keep it patched and set to the right security level.
- Set the security level to a higher, custom level if and when exposed to potentially dangerous content.
- Be somewhat choicy regarding the "free" exploration of the Internet.
Still, all of the above does not help us with the files we have deliberately download to our computer and now wish to execute.
Downloads
Being able to tell a good file from a bad one just by looking at it is some sort of a hacker art. Most people cannot do it. Therefore, they must rely on tools written by other people to perform some sort of code analysis and then, based on the result displayed by this tool, decide whether to run the file.
First, here's the best advice ever - if you have any, even the slightest doubt that the file might be infected - do not run it. As simple as that. Consider the risks involved. Does the computer you're about to execute the file contains personal, valuable information that you do not wish to be corrupted, damaged, lost, or sent to a third party? What will you gain from the execution? What will you lose? If you absolutely have to run a suspicious file, there are some things you can do to minimize the risks.
Scan the file with anti-virus
If you are running some sort of anti-virus (or any anti-malware) program on your machine, put it to a good use. Still, results from a single application might not be satisfactory - or reliable enough. However, running tens of anti-malware scanners on your machine is simply impractical.
For this purpose, two highly popular websites exist, whose entire purpose is to allow people to upload suspicious files and then scan them with a whole army of anti-virus and anti-malware scanners. Files are then forwarded to the vendors of these products for signature updates.


If you upload a file to both these websites and the results come clean, you are most likely OK. Still, it is entirely up to you to decide what you want to run on your machine. At the very least, you should have backups of your important documents and preferably run a firewall with outbound control.
Search for answers on the Internet
The sentence "Google is your friend" has some truth to it. There will always be someone somewhere who has tried before whatever you are doing now. If you are not sure if the file you're about to run is malicious, open a browser, head to your favorite search engine and then type its name, in conjunction with malware, spyware or similar terms. Then, spend some time reading, trying to find useful information on the relevant topic. You will most likely find the answers very quickly.

Virtualization
This is definitely an advanced topic, but if you want to test a file and are not really sure what its impact on the system might be, you may want to try it on a separate machine - or even a virtual machine. While not the silver bullet, this method can go a long way to ensuring the files you want to run on your machine behave as you expect them. I will not elaborate here. Please read VMware Player - A great friend for more details.
Security through Obscurity
Security through obscurity is a common practice of avoiding trouble by disguising your security setup from potential attackers in an attempt to make their attempts more difficult. The desired result is usually achieved by advertising as little information as possible about your setup - or lots of false and misleading information. While the products at hand are neither made better or worse by this practice, it is possible that the obscurity may slow down or deter potential attacks.
Browsers can achieve some levels of obscurity by answering as little information as possible to the servers they contact. This means blocking cookies and referrers and altering the user agent string in the page requests. For example, it is possible to "masquerade" Internet Explorer as Firefox, in an attempt to prevent automated drive-by downloads hosted on potentially malicious sites from being triggered any time a connection is established with Internet Explorer. This may or may not work. Furthermore, Internet Explorer will remain as safe - or vulnerable - as it currently is.
Lastly, to be able to use these features to their full extent, some advanced knowledge is needed - we will discuss them in a separate article. For now, keep in mind that it is possible to make your Web presence less obvious. This will not increase your actual security and will most likely result in some inconsistencies in the quality of Web experience you may be used to so far, but you might gain some leeway against potential attacks.
Another, less technical aspect of the security through obscurity approach is to use little known (i.e. obscure) products. In our case, this means using less popular browsers. This may help keep you off the radar, but it might also inadvertently make your online experience more difficult. Less known browsers tend to be less supported, sometimes resulting in poor Web performance. However, if you are willing to sacrifice some usability for potential, unguaranteed security, then you might want to consider this idea. Some of the Windows-supported browsers you may wish to consider for this task are: K-Meleon and Safari.
Conclusions
Internet can be enjoyed. That is a fact. And there is no reason to smother your computer with anti-this-or-that software in a frantic attempt to stay ahead of the "bad guys." The security begins and ends with the user. The user is the one in control of the software - not the other way around.
While the Internet is an alien world to most of us, the strange terminology can be learned. And the same principles that guide us in everyday life also apply here, because, after all, we still have to deal with people on the other end of the line.
Think before you click, be choosy about your downloads, use a good browser like Firefox - and you should be okay. Really. It is as simple as that. Of course, you can fine tune this approach further, but for people do not wish to bother with immense security tweaks and ideas, the basic setup is enough. I hope this article has helped you much better understand how to handle the Web safely - and with pleasure.
Cheers.