Updated: December 11, 2008; December 20, 2008
Note: I have edited the tutorial, following great advice by tlu and Kays (the SuRun author). The changes mainly concern the password-protection policy and the use of program lists for trusted/untrusted users. tlu, Kays, thank you for your feedback!
Most people run Windows (XP) with full administrator accounts. This means they can do things very easily in Windows - double-click and Bob's your uncle - both good and bad things. The problem is when bad things happen. The system is wide open, with nothing to limit the damage.
If the bad things were limited to user mistakes, the situation might be almost tolerable. The problem is that our computers are connected to the Internet. And every day, we work, play and fiddle with hundred of documents and programs, some of which could be and are malicious in nature. This nature of today's computing brings the average user in close contact with high levels of risk. The risk can be mitigated by careful practice of common sense and a few basic principles. But this method requires knowledge and discipline. There is an easier way, though.
The answer is: Limited User Account (LUA)
It is possible to run Windows in the non-default, non-administrative mode. This automatically reduces the user's privileges and access to non-core files and folders, significantly reducing the chance of potential damage.

The ONLY problem is that the default Windows LUA mechanism is somewhat rusty and will not work well with most programs. The Windows has been designed to work under the administrator account and things will break or work improperly under LUA. Firewalls, anti-virii, P2P programs, games, most won't cooperate well with LUA, even when you try to temporarily elevate privileges.
Quite a few people (and programs) have tried to solve the problem. A few names that spring to mind include Run As, MakeMeAdmin, SuDown ... So far, there has been no adequate solution. And by adequate, I mean a program that is stable, rock solid, simple to use, bug-free, secure, and offers seamless functionality. The biggest problem was the last issue. Until now.
Enter SuRun
SuRun is the latest incarnation of programs that mimic the default UNIX system configuration: the user account is regular and limited; system access requires temporary elevation of privileges to the administrator (root) account, by the means of password authentication. This principle is known as SUDO - Super User Do. The user sudoes access to the system and relinquishes it when done.
On UNIX/Linux, this has always worked perfectly. But on Windows, it has not. SuRun changes this. It is the first application that truly encompasses the principle of sudo on Windows.
How does SuRun work?
After you install SuRun, you need to configure users to become members of the SuRun group. These users will lose their former account privileges and become limited users. But when needed, they will be able to elevate their privileges, using a password.
The best part is - SuRun will elevate the privileges for the CURRENT user account! It will not try to run programs as another, administrator account. This means all registry entries and file system paths will be correct, just as the user expects them!
Additionally, SuRun does not violate privacy, security and access rights by trying to run things from another account. Everything is restricted to the specific, current user account. Furthermore, SuRun has many other advantages over alternatives. You should read the following forum thread for more information.
SuRun: Easily running Windows XP as a limited user
Good. Now, let's install it.
Install and configure SuRun
Getting hold of SuRun is very simple. Head to the official site and download the package. The website is in German, but it offers an automatic translation to English. The program itself is in English and works well. Before we execute the installer, there are some things we need to do.
Create an account that you want to SuRun
First, let's create a new account. We will make it an administrator account. Then, we will log out of our current account and log in to our new account. As you can see, our new account is called SuRunner. Password protect this account!
Why is the password important?
Well, if you are sharing your machine with other people, then you will definitely want to restrict the access they have to your account. But more importantly, the password will keep them from gaining administrative rights when trying to elevate the privileges. We'll discuss this a little more later.

In the new account, we will execute the SuRun installer. Please note that I usually use the classic theme in Windows XP. To differentiate SuRunner from other accounts, I'll stick with the default theme.
Before you execute the installer, I recommend you disable any HIPS software, as they can interfere with SuRun - just for the duration of the installation. For example, I set the System Safety Monitor (SSM) HIPS into the Learning Mode.
Now, once you execute the installer, you will be asked a few questions. The explanations are rather self-explanatory - run SuRun Settings manager after the installation and disable access by limited users to files and registry keys created by SuRun administrators.

SuRun will then do an unusual thing. Your desktop will fade and become inaccessible. Do not worry. You'll get it back in a few moments. For now, concentrate on configuring SuRun Settings properly.
Step 1: Common Settings
You should mark Show SuRun settings for experienced users if you are one of them. If not, tick Set Recommended options for home users.
Still, let us review a few options:
Users must enter their password is a very important step! It's one of the basic foundations of the SUDO mechanism. Let me elaborate:
If you do not use the password, anyone using your computer will be able to execute programs with elevated privileges. Please note that SuRun does NOT require passwords to function and its security mechanism will not be compromised. SuRun uses human-driven input from the keyboard and the mouse to distinguish from automated operations by potentially malicious programs. In other words, the chances of a rogue program executing, being able to hook the keyboard and the mouse while running in the limited account, guessing the exact location of the OK button, and "clicking" on it - are nil. But rogue human users could easily do it. Passwords will keep other users from doing harm and gaining elevated rights they ought not to have.
If you are installing SuRun on a non-clean machine, where you might suspect a keylogger in action - or similar, the use of the password could be tricky - but so is the infection, in the first pace.
Shell Integration options are also useful. I recommend you select at least some of them, since they allow you to sudo-access system settings functions easily. At the very least, check Start/Restart as administrator, SuRun Explorer and Control Panel as administrator.

Step 2: SuRunners group
Here, we will configure our SuRunners users - limited users that will have SuRun (SUDO) access.

Click Add to add a user. Select from the list of existing users on the machine. We'll choose SuRunner, our new administrator account. SuRun will ask us to confirm our choice. It tells us that SuRunner will LOOSE (lose) the administrator status. Good. Exactly what we want.

Now, we have a new user configured (please ignore the Program list for now...). We have the option to configure what SuRunner can do - whether it can change SuRun settings, whether it will require password to change access SuRun settings, whether the account can only use a predefined list of programs with elevated rights, and more.
If you are configuring an account for yourself, then you should give yourself as much access as needed. If you're configuring, let's say an "untrusted" family account, then you should not let the user have any access to the SuRun settings. You should also hide SuRun from the user.
If you do not select User can only run predefined programs ... then the Program list below becomes less important, because the user will be able to run all programs that he/she requires.

Let's add a program. As you can see, we've chosen the ZoneAlarm firewall executable. Depending on your setup, you will choose between allow, ask and deny for the particular application.
SuRun defaults are the two options toggled and shown in the screenshot below: ask if the program can be started with elevated rights and ask only if the program requires to run with elevated rights. Any application not included in the list or any application specifically included with these options will have complete system access when allowed to run with elevated privileges.
Therefore, if you do NOT use the option Users can only run predefined ..., the list of programs becomes a blacklist of applications you do not wish the certain user to be able to run with elevated rights, provided you toggle the right options.
If you DO use the option Users can only run predefined ..., the list of programs becomes a whitelist of applications you wish the certain user to be able to run with elevated rights.
You will probably use the first option (blacklisting) for yourself and other trusted users and the second option (whitelisting) for untrusted users. The first option will only be valid if you toggle non-default selections (other than ask if ... and ask only if ...). The whitelist will only be useful if you toggle these two options or start programs automagically. In other words, for these untrusted users, you best bet is to toggle don't ask and NEVER ... or start the program automagically ...


if you must limit certain applications for certain users, this is the time to do it. For untrusted users, you should prepare a ist of programs that they should be able to run with elevated privileges. For instance, allow anti-virii to update themselves daily or allow a defragmentation utility to run weekly. Then again, Most Windows users will discover that the problematic programs are security applications, which they do not need if they run as LUA. It's a kind of win-win situation.
Step 3: Execution hooks
This is an advanced setting and won't be enabled unless you specifically ticked the Show SuRun settings for experienced users. The Execution hooks are about controlling programs that require elevated rights. For most users, the default setting is good enough.

Step 4: Advanced
This tab is mainly about configuring the usability of SuRun. For example, you can change the SuRun icon in the System Tray when the active program credentials change.
You can also replace the Windows Run As... with SuRun's Run As..., allow SuRun users to change system time and power options, show Windows update notifications to users and disable auto-restart for scheduled automatic updates (very important!).

Click Save to commit the changes. This will complete the installation. Reboot to commit the changes.

Reboot and use SuRun
After restart, let's login in to SuRunner account. SuRun is now running. There's a smiling green icon in the System Tray. This means everything is fine.

But how can we know we're truly running as a limited account? Well, let's try to change the time.

We can't. This is why the shell option Control panel as administrator is highly useful. You can launch the system options by right-clicking on the desktop.
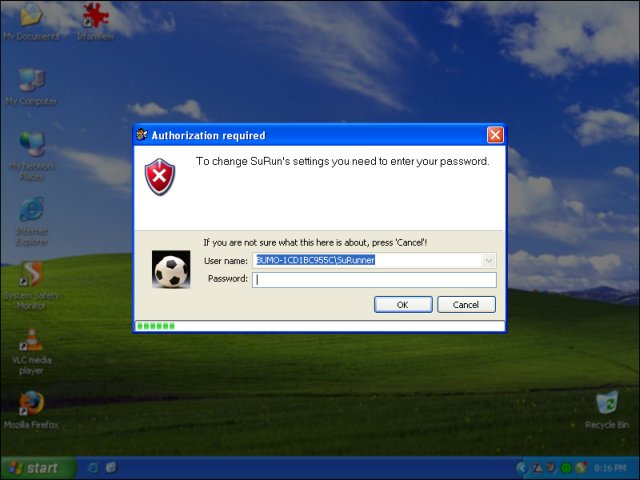
Now, for the exercise sake, let's try to access SuRun settings. Right-click the System Tray icon and try to access the SuRun Settings.
P.S. The two screenshots below were taken at different times, so excuse the difference in time and icon status of the System Safety Monitor (the green yin-yang). Still, on a side note, as you can see, SuRun has no quarrel with a HIPS program.

And we see SuRun in action! We need a password to continue! This is why I stressed the need for the password when we created the account. Without it, the security mechanism is useless.
Similarly, Windows Explorer can be launched with SuRun privileges. For example, this is useful if you need to define shares or work with system files.

Individual programs can also be launched with elevated privileges.


Let's try Windows updates ...
Of course, we will require administrator privileges for that.

And we're happily installing the latest version of the Windows Updates ActiveX thingie. Notice the SuRun icon has turned red. This means that Internet Explorer, or rather, the Windows Updates, are running with elevated privileges.

Everything works! Dandy! P.S. If you need help configuring Windows XP, you may want to refer to my article: Installing Windows XP - Full tutorial.
Conclusion
SuRun is simple and powerful. It truly grabs the beauty of SUDO principle and integrates it into the Windows desktop. For the first time, it is possible to enjoy the security benefits of user account modularity on Windows without losing functionality. SuRun works as promised.
This is a great way of securing user accounts, especially on multi-user machines, where the majority of users are computer-illiterate or trigger-happy. Best of all, you can achieve security without wasting money and resources on tons of security programs. SuRun allows you to pilot Windows XP naked, even in the hands of an inexperienced skipper. That's about it for now. Many thanks to tlu for discovering this program and compiling the detailed thread on Wilders Security Forums.
Cheers.