Updated: April 27, 2019
Several months ago, I wrote my prophetic piece Windows 10 updates - One step forward, one step back, which lamented the massive over-complication in the update facility in the latest version of this operating system, the amount of time needed to get things done, as well as some planned improvements designed to address these issues. Then, there was also the matter of quality.
I highlighted this in my recent Creators reviews - for the first time ever, I had big errors in the 1804 build, something that has never happened to me before, as Windows Updates used to be legendary rock-solid. And then, Build 1809 introduced still more issues. Not for me, but everyone. Microsoft actually paused this update, restored it, and then axed it completely. And then, they revamped the update functionality.

So what's happening?
Well, Microsoft has changed how Windows 10 handles updates. First, there's a separation between regular monthly patches and feature upgrades (the twice-yearly upgrades a-la old service packs). Second, Windows Home users will have the option to defer updates for up to 35 days, so they won't be instantly pressured into installing packages and possibly hitting bugs, the way it's been happening more and more lately. There are still other changes, all of which are meant to reign in the chaos.
In a nutshell, more like ... the old updates.
Now, we need to be fair and give praise when praise is due. How many (big) companies are capable of admitting mistakes and backtracking on their decisions? This is something that's not done in the industry, and you usually end up with long, almost religious spiels of buzzwords justifying one bad decision after another. But Microsoft did change and react, quite a few times in the past several years. There was the Start Screen fiasco, and now the updates are becoming more reasonable.
This is a VERY good thing - and I will write a complete article when I test this properly, come the 19H1 update. In general, my expectations are fairly simple: speed and stability. Windows 7 and 8.1 allow me to complete updates within about 20 minutes, one reboot, done. Now, there used to be a slowness problem for a long time, but that one got resolved. On Windows 10, I'd like to see the same kind of speed, because having to wait for an hour or two for the system to upgrade is simply too much. It's time that people need for their productivity, and it's not something that one can easily afford to lose.
Active hours & automatic updates are another big issue. As a personal example, my Windows machines stay up without reboots for many weeks, and overnight they run all sorts of scheduled tasks, including backups. The work setup remains, and having the system trigger a reboot is highly disruptive. The transactional nature of the automatic updates works fine for phones, where people have little to no 'history' to their immediate work, but that just isn't feasible on the desktop.
Then, there's the reliability element. While I NEVER update a machine without performing a full system image first, even the notion of having to restore the operating system state because of a bad patch is annoying. Another waste of time. And this wasn't a problem. Ever. Only now, the overall quality of patches is going down, and the problems are also propagating into the older versions of Windows. I know this is related to anti-virus software, and while you don't need one, most people do use one, and who knows what other complications may arise. The whole drama around speculative execution issues with Meltdown and Spectre doesn't help, because things took another turn downhill in January last year. Also, back then, there were similar issues with the patching and anti-virus compatibility, only the problem is now isolated to non-Windows 10 systems.
So it's not a big ask: reliability.
Sounds familiar? Yes. Much like the old updates!
And so we have years and years of work going toward making development seem faster, but in the end, it just doesn't work. There's a reason why old, tested methods are the way they are. There's a reason why you cannot just arbitrarily change systems due to random fashion fads, whatever the technology jargon of the week may be. Microsoft's decision to slow down is a right step in the right direction. Well done.
That said, I will now diverge and show you the amount of hassle a Windows Home user - a savvy and determined user - needs to go to in order to prevent their system from automatically updating itself, with all the associated perils in the process.
Medic to your medic
When Windows 10 first came out, if a Windows Home user wanted to prevent their box from updating automatically whenever there was a patch, they had two options. They could mark their network connection as metered, or they could stop the Windows Update service.
At some point, Microsoft disabled access to the Windows Update service - made it run with higher privileges than your admin, so you needed a tool like ExecTI to run services.msc as TrustedInstaller, in order to be able to stop and disable the service. Come one of the Creators updates, there was a new service - Windows Update Medic, designed to start the service whenever it detected it was down. This one also needed extra privileges.
Going through the system, I've discovered still more tools - additional services and scheduled tasks, all designed to keep the update service running at all costs. Now, I do understand the imperative - unpatched machines can be risky and all that - but we're now in a situation where there's half a dozen processes whose only purpose is to keep the update service alive. And they work against the user. Ordinary people don't have the skills to manipulate services, but if someone had stopped one, there's a reason for that. The system should not pretend to know better.
You may say, but Dedo, malware can do this. Yes, malware also prevents you from stopping it. The symptoms are similar, and they create a dangerous precedent: 1) users become insensitive to anomalies and ignore real problems when they do occur 2) users developer distrust toward their operating system and thus end up not doing any patching whatsoever.
By adopting a self-healing mechanism that works against the user, Windows Update accidentally co-equates itself with the kind of software you don't want on your systems. If you hit the software forums discussing Windows updates, you will notice a prevalent tone among the techies who simply end up refusing to do any updates on Windows 10 whatsoever, for the fear of their box being changed, or not being able to have control over the operating system. And this is worse than the original state that Microsoft tried to fix.
Now, you may ask, well, how do you distinguish between a tech savvy person making the Windows Update change themselves versus bad software altering your system state? Well, the first thing one should discuss is not what happens AFTER you contract malware, it's what happens BEFORE you do that. Because once it's on your system, not having updates is the least of your problems. There are many practical ways to make the system secure, like using EMET or Exploit Mitigation and running a standard (limited) account. Inbound firewall is very useful for home systems, and totally applicable unlike the industry where botnet attacks are most likely to happen, plus most home users have some sort of router, which often features a firewall of its own.
Second, if you really want to do this, there are two ways. One, the old method that allowed Windows 7/8.1 users to make whatever choice they like (still available to Pro users), or perhaps a CAPTCHA mechanism on service state change. Ask the user to authenticate or provide some sort of code, and you know that it's a deliberate change that a techie is doing, and then, there's no reason to "heal" their service.
Going back to the topic of services and scheduled tasks, this is what I came up with. First, services, we have Windows Update and the Medic service. But there's also one called Update Orchestrator Service, which downloads updates, manages them, and checks their integrity. Sounds important. Yet.

I don't recall this service being there in the earlier builds of Windows (I might be mistaken), but more importantly, even with this service in the disabled state and only the Windows Update service manually turned on, I ran a full sequence of updates, and the machine was able to download, install and configure the monthly patches without any problems. I am actually bothered by the inconsistency between written text on the net and the actual results.

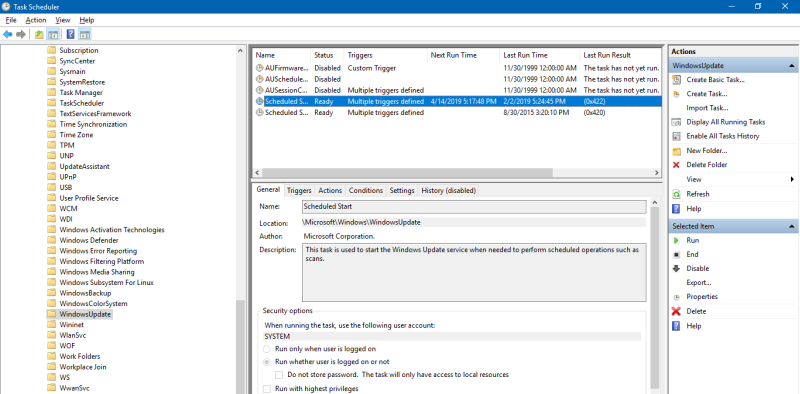
Then, there's a section that covers the Update Orchestrator. A few were disabled, but there were others that would run checks and whatnot. This would be perfectly fine if not for the forced nature of updates that could potentially bring bugs (I need a system image first), disrupt work (reboot that happens in the middle of a nightly backup and kills a work session). So there's more to disable.
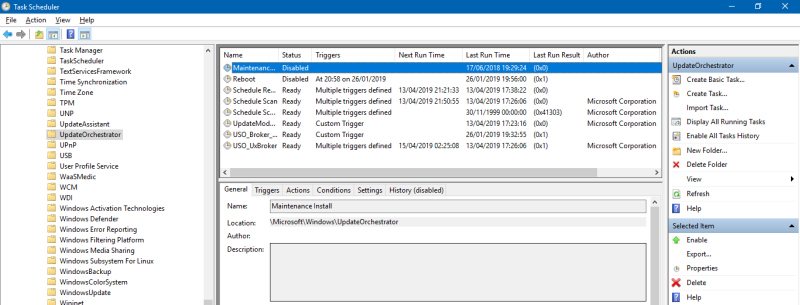
And so, in order not to have their system restart at random times and possibly end up unbootable, which can happen and has happened, instead of using an official toggle, sanctioned by Microsoft - the way it was before Windows 10 - tech-savvy users now need to dabble in half a dozen services and scheduled tasks to achieve the same result.
This actually makes the system less stable, less secure, less everything! But between potentially losing important data due to a reboot and tweaking the system, I think the choice is obvious. Microsoft does seem to realize and understand this, hence the change, which is a first step toward winning the trust of its users back. Took a while, but it happened, and that's the important thing in this story.
Black Viper & deeper look at the services
At some point, I even decided to consult the Black Viper's guide on Windows 10. This dude became famous in the XP era when he wrote a guide on which services you could safely disable to improve performance and minimize the system footprint, memory and security wise. I looked, and then went through the services to see what other entries were showing there and had no applicability in my setup, namely a local account with no use of the online store or any purpose for the touch-optimized universal apps (UWP) or whatnot. And remember, I'm saying this as a happy Lumia 950 user. In the mobile space, Windows Phone is the most elegant operating system ever designed, with the best ergonomics and layout, and the whole paradigm makes total sense. It's a tragedy Windows Phone will be EOL-ed at the end of the year. But on the desktop, there's no value to touch apps, as they are inferior to their desktop counterparts in every way.
Among the first entries, you have AppXSVC. This service deploys Store applications. If you're using a local account, then you can't really install Store apps anyway. So what's the purpose of this in the local setup, for instance? Even with this service stopped, Metro apps launch and run just fine really.

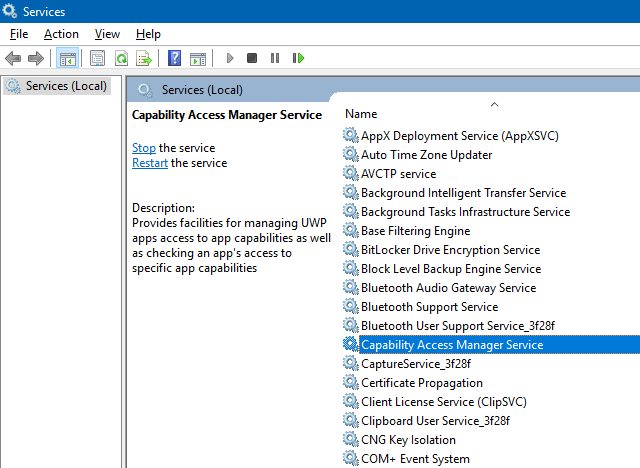
I found another - Capability Access Manager Service. Now, you need this to actually be able to read and set the access permissions for UWP apps, like Mail, Calendar, etc. This affects what you see in the Settings menu, and with this service turned off, the toggles won't display. But then, if one has everything tweaked to Off anyway, and is not using any of these apps, does this service need to be running, why can't it be set to Manual?

Another Store-related service: ClipSVC. This is for apps you bought in the Store. No problem, but we go back to the issue of local versus online (Microsoft) account. If you don't have one, you can't shop. That's fine too, but the service is not required unless one has an online account, has one associated with the Store, or has purchased apps through the Store. I'm not opposed to this at all, I'm just seeing no purpose in having the service up and running if the user cannot take advantage of the functionality.

I would actually love to be able to use a store in Microsoft a-la Synaptic, Software Center, KDE Discover as in Linux, but that just doesn't really exist. The mobile-thingie apps in Windows Store aren't the classic desktop apps you want. You just can't have the full desktop programs. If that existed, that would be really neat. Alas.
Anyway, I came across something called Geolocation. Why would this be useful on a desktop? I know that Gnome offers something similar, and there, the question also remains. This is useful if you're on the go, or travel abroad, and then you might want to get localized results. But in most cases, it just doesn't really make any sense.

Then, I finally stumbled upon an oldie but goldie - SSDP Discovery - unplug 'n' play that dynamically opens ports for you, so you can game and such without having to manually tweak applications. This didn't make sense on XP, and still doesn't on Windows 10, and won't work if you have a router that has UPnP disabled, which you should if you're actually trying to do something practical from the security point of view, for a change.

Sync Host - syncing mail, contacts, and other user data. Sync where and how? If you're not using an online account, this won't work, so there's no purpose to this service. I also discovered I couldn't really stop it, which is another interesting facet. So much potential, so much goodness that made sense on the Phone, but doesn't fly on the desktop.

And there were tons more other services, all of them geared toward a model that simply isn't applicable to the typical desktop user. The thing is ... Windows XP had hardware profiles, where you could actually boot your machine into different configurations, so you could have a gaming profile, a sharing profile, a security profile, etc. This could have been used to provide practical configurations rather than a generic permissive setup that doesn't really give any advantage. For example, a local account doesn't need any online-aware services. Too much stuff running could actually harm the performance. So not having the extras is a win-win situations both from the functionality and philosophy perspective.
But you hate tweaking!
Yes I do. If you read my articles going back to 2006, you will see that I'm opposed to tweaks. There are few systems changes that I believe should ever be made, and yet, I found myself taming Windows 10 quite extensively, the very thing I promised myself not to do. And yet, I had to do it, to ensure I have the right level of control to manage the system if and when I deploy it in my production environment. There will come a day where I will probably end up using Windows 10 (Pro), and I need to make sure I can maintain a sane, stable, robust, quiet, and effective setup.
What Microsoft aims to do in their upcoming release is a first, important step toward restoring some of the awesome quality they used to have in their systems. Kudos, and let's hope this is a beginning of a positive change back to the slow-and-unbreakable philosophy.
Conclusion
You may feel this article is all over the place - but it's not. It's a culmination of about four years of a process that ended up being rather superfluous. Automatic - and forced - updates did not yield better quality, stability or security to Microsoft Windows users, something the vendor has acknowledged and is gradually rolling the clock back from agile to awesome. In this regard, there are almost no documented cases where giant corporations admitted mistakes and managed to steer themselves to a different track. So this is hugely important, no matter what you think or feel about Microsoft.
That said, there's still a lot more to be done to regain the legendary quality of yore - and also restore the user trust. Updates are a first step on that journey. For me, the end will have been achieved when I realize I need not make any changes to the system defaults ever again. And if Microsoft plays their card right, they can win big here. Because mobile systems are all about being closed and locked with little to no user control, so Microsoft has the opportunity to do the opposite. We're not there yet, the hope is strong, the perils high. But for now, as far as Windows Updates are concerned, it's a step in the right direction. One small step for man one giant leap for ... whatever.
Cheers.