Updated: July 15, 2019
A few days ago, I read a flurry of articles surrounding the July batch of security patches for Windows 7. One of them, the security-only KB4507456 package, available through the Online Catalog (and not WU) seems to contain telemetry code, too - something called Compatibility Appraiser. Hm, naughty.
I decided to check this and see what gives. There are two important findings to this - one, whether Microsoft sneaked in telemetry to Windows 7 in the guise of a security-only fix, and two, the wider implication of this move when it comes to user trust. Let's explore.
Compatibility Appraiser
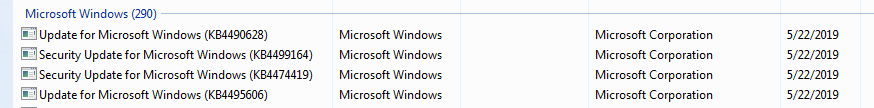
To see whether the July patch truly pushed a naughty bit onto Windows 7 users, I checked the status of one of my Windows 7 machines, which had last been updated on May 22, i.e. it has not been subjected to the July round of patches. Lo and behold, it had the exact same entries under the Task Scheduler as referenced in the latest series of articles.
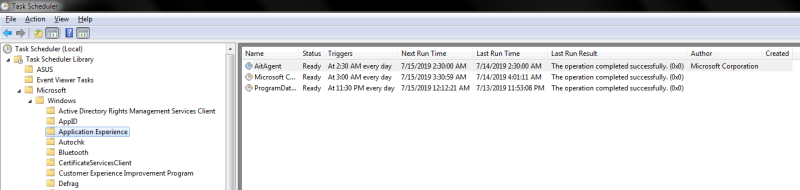
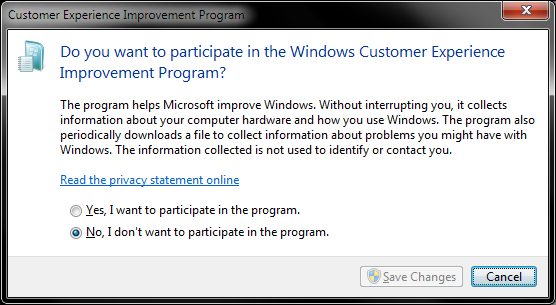
So no, this wasn't added in July - merely updated. For what reason? I do not know. However, these tasks do not do anything unless you're opted-in the Customer Experience Improvement Program (CEIP). Indeed, the text of the scheduled tasks under Application Experience reads:
Aggregates and uploads Application Telemetry information if opted-in to the Microsoft Customer Experience Improvement Program.

And you can check whether you're opted-in the CEIP. By default, Windows 7 is NOT opted-in CEIP.
Now, there was a point where one of the cumulative updates introduces a new service called Diagnostic Tracking Service way back when - but I do not believe it is related to the scheduled tasks above. On this particular host, this service is in the disabled state, and this state has not changed between updates (so far).
But I've talked about this many years ago, with the whole Windows 10 & keylogger conspiracy. This isn't really anything new, and the data telemetry has been around for a long time. From all practical purposes, the presence of this code doesn't alter how Windows 7 behaves. But that's only the first point of this situation.
User trust
The more important element is HOW Microsoft did the update. Security-only means what it means. To include packages that do not serve a security-only purpose is a breach of user trust who expect their updates to do as the text says. Indeed, the move to cumulative updates has removed a degree of freedom among advanced users in how they manage their patching, as the granularity of yore is gone. This means you must accept the whole bundle of updates - or none at all.
Then, let's not forget the GWX campaign. Hardly the record of awesome behavior that you would expect. Indeed, many people got burned by this aggressive push to use Windows 10, and it still lingers. The latest set of updates, REGARDLESS of what they factually, technically do, erodes the trust even further, and in the long run, will only cause more damage. That's classic sales foot-in-the-door nonsense. Works for people with IQ in the double-digit zone, does not work for smart people.
So no, there's nothing new on the telemetry side. Yes, there's something new on the updates side - and that means they're less trustworthy than before. You can add the reduced quality of updates in recent times, and none of this helps build confidence among Windows 7 (and possibly Windows 8) users in moving forward and trying Windows 10. Because freedom and privacy are important, even as philosophical concepts.
Speaking of freedom and privacy, come the day, if you don't want Windows 10 upgrade, then Microsoft has released updates that allow you to block system upgrades once and for all. Indeed, you should check my Windows upgrade & telemetry article. This means you won't be nudged to try the "modern" world and whatever. Specifically, the relevant patches include KB3050265 for Windows 7 and KB3050267 for Windows 8.1. There you go.
What to do then?
Well, my advice on automatic updates from 2008 still stands. You should NEVER blindly apply updates, because you can never be 100% sure that the other party has done all the testing and validation to ensure you get a foolproof product. But there's more. Let's elaborate.
- Never be the first to apply updates. Most of the time, there's nothing cardinal that requires you to apply patches right away. After all, Microsoft provides patches on a monthly cadence, so this means you're getting patches 1-29 days late (think about it). If the whole ecosystem is set up to deliver patches in this way, a few weeks here or there won't matter. On the other hand, this is plenty of helpful, precious time during which bugs and problems can be detected - ergo this issue. Let others find the problems, and then patch once everything is sorted and peachy.
- Never apply system updates without a FULL system image. This way you can roll back if there are issues with patches. In the past twenty years, I've rolled a few systems back due to bad updates. In fact, this is the only reason I ever needed to use the imaging, to undo damage caused by system - and a rare few application - updates.
- The whole security thing is overrated, in general. Yes, being a target of a hack or similar can be painful, which is why backups also play an important role. But you're more likely to be a victim of other companies misusing or misplacing your data than you being a victim of your own folly. You can read about massive data breaches almost daily. Hundreds of millions of records of data being leaked all the time, from names and emails to physical addresses and credit card data. And you have little control over this. So your system can be a few weeks or months behind the latest set of patches, as long as your Internet-facing apps are properly configured, you should be fine.
- You could say - the fact someone else is doing a bad job, that doesn't you should, too. Correct. But having the system fully patched isn't a panacea. Like I said, having Internet-facing apps patched is important. Then, you should consider using a standard rather than admin user. You want something like Noscript for your browser, and you definitely want EMET (and Exploit Mitigation in Windows 10) as your security tools. All of these are vastly more important than the run-of-the-mill fearmongering you get in mainstream IT media, or the system patches. Oh yes, you're not a business that must keep their network ports open. Use a firewall or a router, and then all sorts of vulnerabilities that affect servers don't apply to you.
Last but not the least, keep that resentment boiling. A good controversy is often more effective than technology. Companies fear reputation damage more than anything else.
Conclusion
Sometimes, it is hard to separate fact from emotion when it comes to technology. This does not help the end user, because when people come searching for solutions to genuine concerns like this, they first have to filter through outbursts of pent-up frustration as a result of many years of salesy bullshit.
From the technological point of view, there's nothing new here. However, the fact you now get non-security nonsense with security means you can't really trust updates from Microsoft anymore. So if anything, this will majestically backfire. People don't like being pushed, and I'm amazed with the repeated attempts to do so, again and again.
Well, I never trusted any updates ever, hence my wait-and-see image-first approach. That's the best I can offer you now. As to a brighter future, there probably won't be any. The golden days of computing are behind us. Things will, across the board, just get worse for smart and independent people. The Linux desktop was a great hope, once upon a time, but that's another sad, empty dream. On that happy note, bye bye.
Cheers.