Updated: September 20, 2013
By now, you know that Microsoft Enhanced Mitigation Experience Toolkit is the best security software for the Windows operating system. The reasons are many. Chiefly, it is simple and transparent to setup, and there are no silly questions. It's free. And it's effective in what it does. Not stopping you from being a fool, but stopping software from misbehaving. And that's what makes it awesome, and this is why it gets so little spotlight in the pay-for-security world out there.
Now, the first really public version is out there, numbered 4.0. True, the previous versions were also usable, but they were sort of beta slash interim editions, mainly intended for geeks. This one can be used by normal people, too. Let me try to give you an overview as well as a somewhat detailed tutorial that should help you use and implement EMET in your security setup with jolly good ease. After me.
Installation
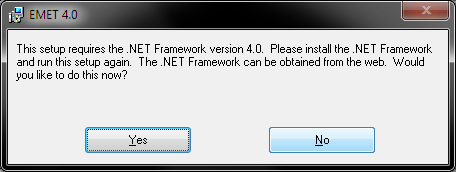
The installation is rather trivial, but there's one thing you need to take into account. EMET v4 needs Microsoft .NET Framework v4. How poetic. Indeed, you will first have to install this one to be able to use the latest edition.
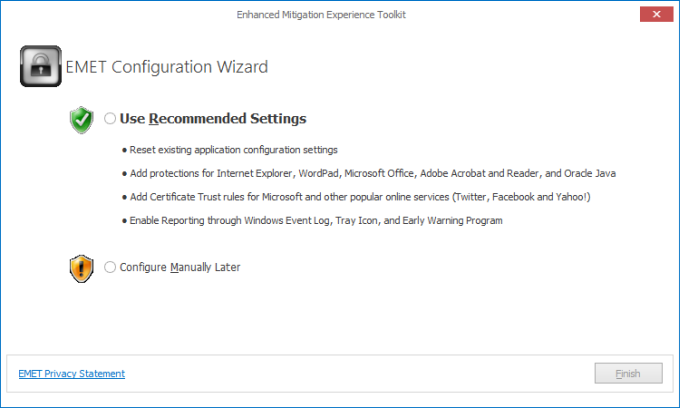
Next, Just click through the wizard as fast as you can, without reading any details. Seriously, it's easy. The one step that you should pay attention to is the first post-install wizard.
The configuration wizard allows you to configure EMET before it launches the first time, and this is really a recommended step for most users. As its states clearly, it will reset application settings from previous installations, add protections for a number of commonly used and commonly targeted programs, including Internet Explorer, Adobe Reader and Oracle Java, add trust rules for popular online services so they do not trigger mitigations in your browser, and finally enable detailed reporting through the system log facilities. My suggestion is to do this, because it won't hurt, and most people will manually configure these same settings anyway. Plus, you can always rerun the wizard.
First steps & basic configurations
One the wizard is complete, EMET will launch. Let's evaluate the user interface and its various functions. We will go left to right, top to bottom. If you have already used EMET in the past, the settings will be familiar, only visually arranged in a different manner.

Import/Export & Configuration
Import and Export buttons allow you to save and retrieve existing EMET configurations. These will be XML files that store your settings and applications rules. It is advisable to save your configuration before making drastic changes or re-running the wizard, as you could reset your entire setup. We have discussed the import/export rules in the previous review of EMET, the 3.5 TP edition. For all practical purposes, this is just save/open equivalent to normal software.
The Apps button will open a window where you can configure your programs. More about that later. The Trust button will open a window where you can configure certificates for online services. Soon.
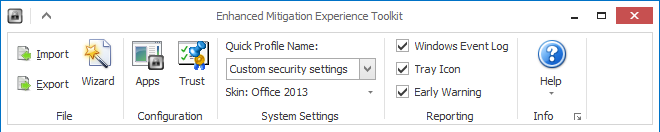
Profiles & Reporting
For those of you wondering, profiles are just a collection of settings, stored in the XML format, and they will include certain rules for your machine. However, they will affect the behavior of the entire system when applied. You can switch between your existing setup, which will be labeled Custom, and the other two, labeled Recommended and Maximum.
The Recommended profile will set mitigations in the manner that Microsoft deems is least disruptive while providing good security. The Maximum profile will toggle all options on, and this means that incompatible software may suffer or crash.
In fact, I would advise against using the Maximum profile, because it is too strict. Too many applications have not been coded and compiled in a way that can be considered safe and compliant, and they might experience weird behavior when subjected to mitigations.
For example, Google Chrome might undergo Aw, Snap! errors. VLC Player will not be able to auto-update with all of the mitigations turned on. In the past, before Microsoft's acquisition, Skype would not work well with some of the options turned on. We will soon explain in more detail what kind of settings exist, and what they might do or not do when switched on and off. Lastly, you can change the application skin, but that's silly.
Reporting is the fourth category from the left, and it covers messages that you might see when EMET comes into action. You will be able to see desktop popups when mitigations are activated, and you will find entries in the Event Log. As a reminder, here's a couple of screenshots from our earlier review of EMET, which highlight the functionality:


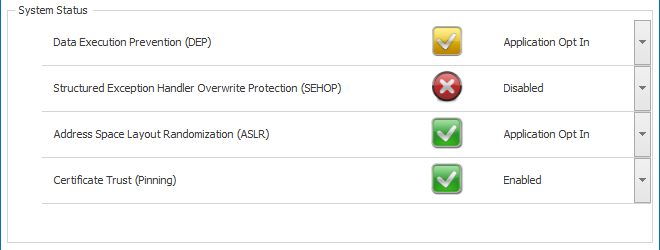
System Status
We will now discuss the System Status field. It lists four types of mitigations for your software. By default, you will see the picture like below, which is quite permissive. It means programs that can use DEP and ASLR will use them, there will be no SEHOP protection activated by default, and the Certificate Trust is enabled.
Now you may be asking what these acronyms stand for? And the answer is, I am not going to tell you. Because they are MEANINGLESS to anyone who is not a programmer or has not studied Computer Science at the university. For that matter, we might discuss the kernel, scheduler, memory management, process space, and everything else.
For normal people out there, what you need to know is the following: these mitigations will ultimately going to affect your software. So the only thing you should care about is the sane and correct functionality of your system. In between the maximum settings and permissive settings, as defined by the various profiles, there are several options you can use.
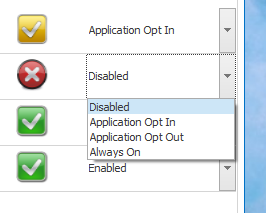
If the mitigation is set to Disabled, it won't be used. Opt In will activate mitigations only for specific system files, binary and functions, and will depend on what features are supported by your operating system, BIOS as well as applications.
Opt Out is more rigorous, and it will try to use all mitigations against all applications, unless you specifically choose to deselect the functionality for certain non-supported or misbehaving programs. Lastly, Always On will activate the mitigation, without any ability to reset it. By the book, it is the most secure, and the most troublesome, because you might end up with too many crashes for your legitimate programs.
Suggestion: Start with the Recommended profile, or if you're skilled enough, your own configuration. Max. settings should be left for until after you figure out how to use EMET properly, and with confidence. Lastly, certificate trust is fairly simple, enabled or disabled.
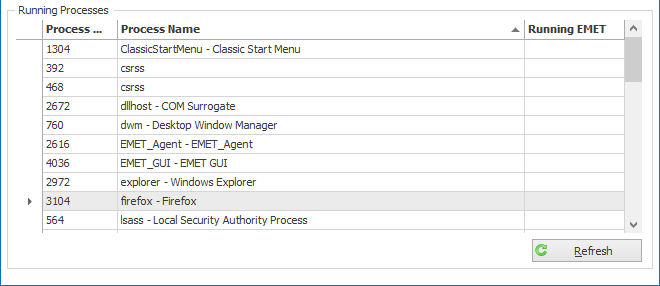
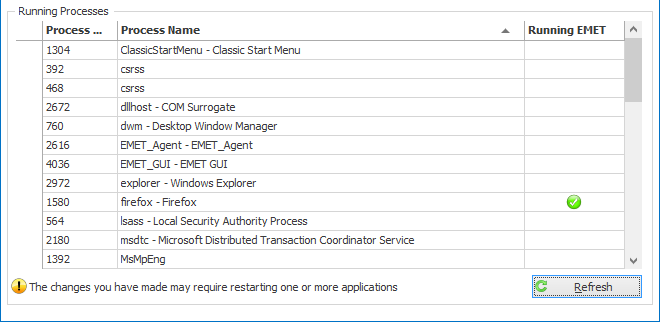
Running Processes
This table just shows your process table and the status for each one, whether they are covered by EMET or not. At this stage, it is not that important, but later on, we will examine how our mitigations come to play.
Applications
So far, we have configured the system. By that, we chose the desired profile, which in turn toggles on/off specific mitigations and their level for the core system files, and defines the default behavior. Now, it is time to configure out applications.
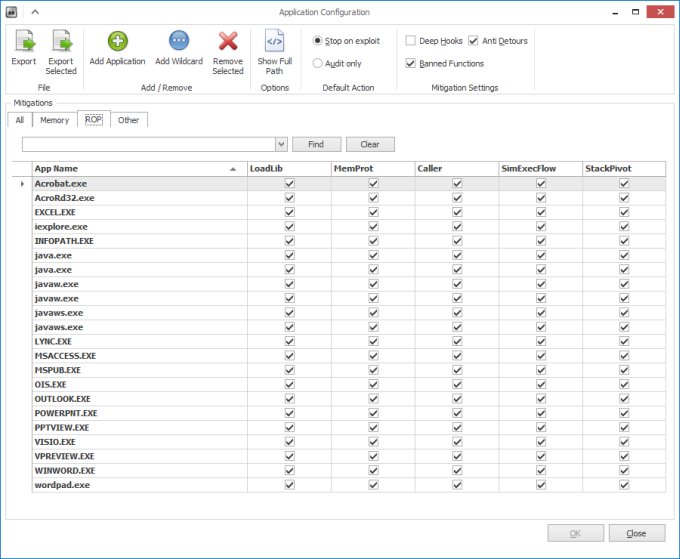
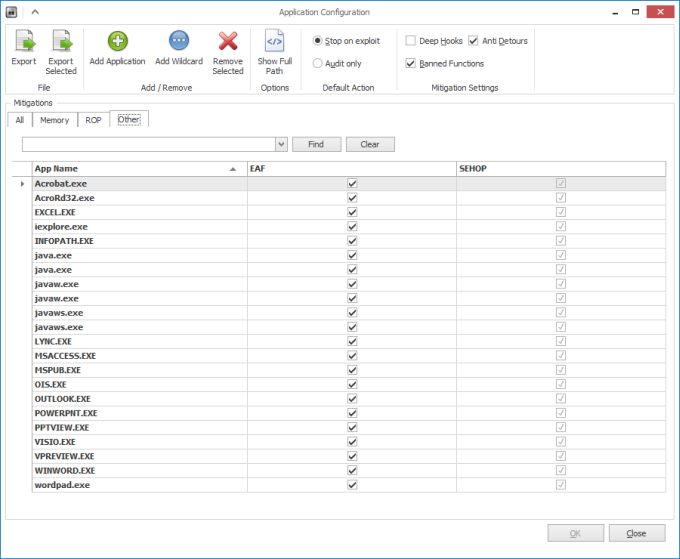
In addition to the general behavior, governed by DEP, ASLR, SEHOP and other mitigations, you can fine-tune the system protection by application rules for your programs. This is accessed by the Apps button in the program's toolbar.

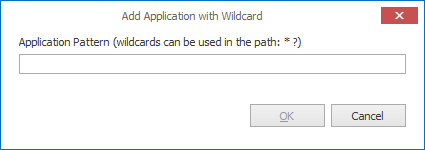
Once again, let's briefly overview what we have here. Export and Export Selected allows you to save rules for your applications. Add Application will open a wizard, where you can search for a specific program by its full path. Add Wildcard allows you just to specify a generic phrase, and all programs matching it will be covered.
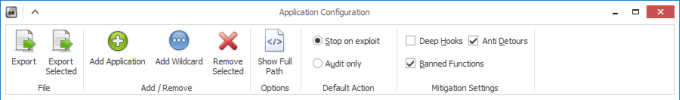
For example, there are two versions of Internet Explorer available, both 32-bit and 64-bit. If you use the full path, you will need to list two rules. The wildcard option will cover both. To wit, you can toggle the Show Full Path option to see what your rules look like.

Please note that the recommended settings, activated by the first-time wizard all use wildcards, which makes it simpler to deploy and govern. We will soon discuss mass administration.
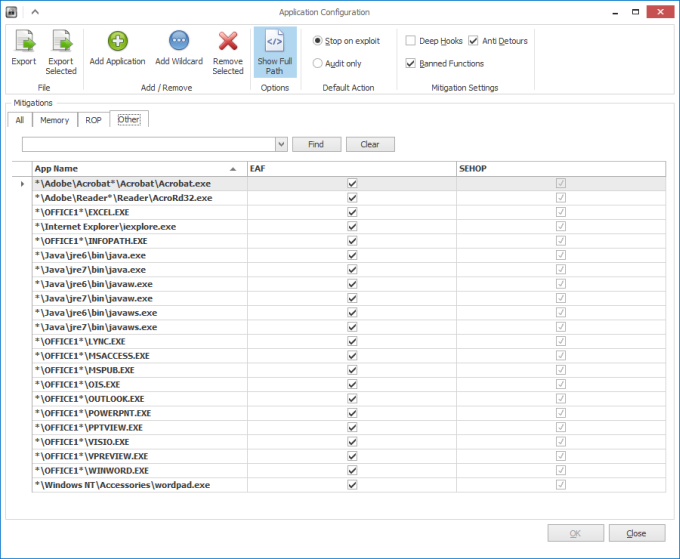
Default Action governs the application behavior - whether to just log, i.e. audit, or also stop the running process when an exploit is found. And please note that this does not necessarily mean malware, just any illegal instruction banned by the mitigation.
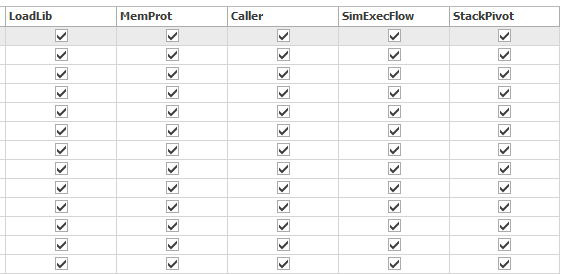
Finally, under Mitigation Settings, you can check on/off different types of mitigations, including Deep Hooks, which are disabled by default in the Recommended profile, Anti Detours and Banned Functions. You can treat these as the holy grail of sane coding practices, if you will.
The Mitigations field will list all applications covered, including those manually added, imported, or cooked by the wizard. There are three types of mitigations, including Memory, ROP and Other. Again, it is meaningless to try to explain these if you do not know or understand how the kernel works. For example, do you know what code, data or heap might be? What is stack? What is a system call? Do you know what an instruction pointer may look like on x86 architecture? If the answer is no to any one of these, then you do not need to know the internals of these mitigations.
Just treat them as one of the settings that will affect the behavior of your programs. If it works fine, leave them be, if not disable, one by one, until you figure out where the problem might be. But more about that later.

Application added
After you add your own application, which might not be listed here, you will probably have to restart the program to load with the EMET hooks. We have seen an example of this in the first article, and how to use Process Explorer to verify this.
Certificate Trust
This section allows you to configure websites that should be covered by certificates, so that you trust their behavior, so that mitigations do not kick in and kill your stuff in what is known as a false positive action.
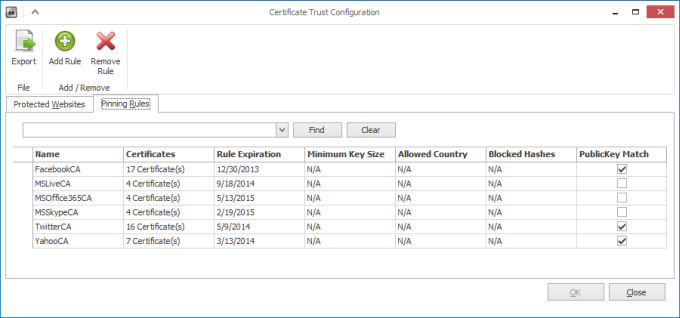
Again, you can export your rules. You can add websites, or remove them. Once you configure them, they will be listed in the Protected Websites table below, and will also include the Pin Rule, which means the sites will be trusted only if they are digitally signed by the certificate authority shown in the rule. You can use the drop-down menu to change the rule, but I strongly advise against it. It's tantamount to manually tampering with digital certificates in your browser.
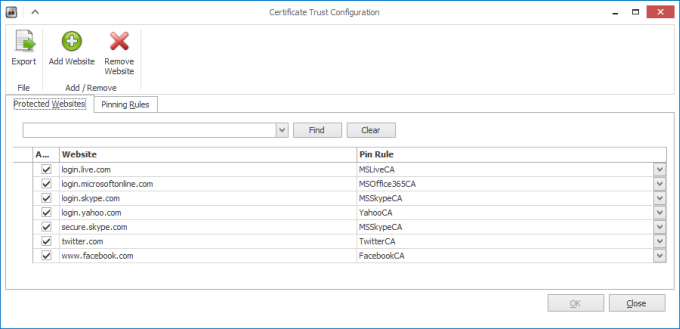
Pinning Rules allow you to fine-tune their effect. For example, their expiration date, the countries they apply to, blocked hashes, public key match, and so forth. For a good reason, most of these settings are not in effect, which means the certificate defaults will be used, without any filtering. My warmest recommendation is not to fiddle with these at all.
Safe practices
The trickiest question is, how do you use EMET smartly? If it comes down to making manual changes and tweaks, you will invalidate your security software, because you will have become the weakest link the chain. You want EMET v4 to run smoothly and without any disruptions. It must be completely transparent, and the only thing you might care about is an occasional exception here and there, like VLC, Skype, etc.
Going back to my earlier suggestion, use the first-time wizard. Use the recommended settings. Add your own programs. Make sure everything works and runs as expected. Let it simmer for a while. Once you're confident, you may notch it up a little, one step at a time, and carefully examine all your software. If programs crash or do not function properly, start disabling the mitigations, one at a time, until you get to the minimal level that allows them to run well.
This can be tedious, but do not be discouraged. My experience shows that only one or two programs will need occasional adjustments, if ever. VLC, Chrome and Skype come to mind, and I have not encountered any other programs that do not work well.
Regarding Certificate Trust, this is a new and possibly somewhat experimental feature, geared toward the merging of the Web and app, and what the combo can do on your local host. In other words, software purchased through an app store and/or running as a Web app could have a potential to make risky changes to your system or be exploited easily if not coded well. On the other hand, you can seriously harm the user experience if the mitigations are too aggressive, which is where the idea of trust comes into place.
My brief experience here shows that the default settings are good enough. Moreover, additional browser security can be achieved through the use of security extensions. But this is a separate topic. To sum it up, leave the certificate trust in place as it is, add sites slowly and carefully if you must, and do not make any changes to the pinning rules, because you might end up with some really weird and unexpected behavior.
Enterprise deployment & profiles in depth
We have discussed Protection Profiles when we talked about EMET version 3. I will briefly recap what we did there, but you ought to read carefully. The section also covers the use of Group Policies for easier management.
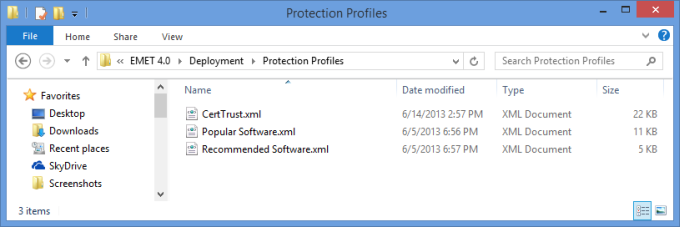
EMET profiles are stored under Deployment\Protection Profiles in the default installation directory, in the XML form. There are three profiles by default, including CertTrust.xml, Recommended Software.xml and Popular Software.xml.
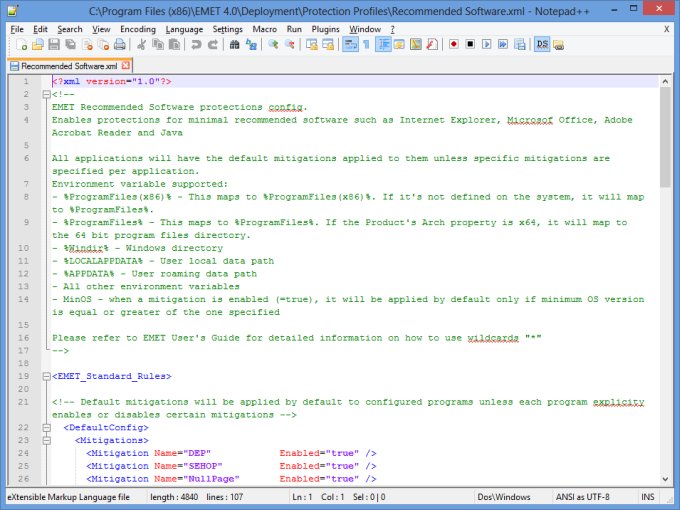
Any profile or profile change added there will be used to create the relevant cross-section of mitigations for your applications the next time EMET rereads its rules. The profiles can be tweaked to match any kind of security granularity you wish to achieve with EMET. The profiles come in the following format, for example:
<Product Name="Windows Media player">
<Version Path="*\Windows Media Player\wmplayer.exe">
<Mitigation Name="SEHOP" Enabled="true" MinOS="6.1"/>
<Mitigation Name="MandatoryASLR" Enabled="false" />
<Mitigation Name="EAF" Enabled="false" />
</Version>
</Product>
<Product Name="Skype">
<Version Arch="x86" Path="*\Skype\Phone\Skype.exe">
<Mitigation Name="EAF" Enabled="false" />
</Version>
</Product>
What do we have here? It's XML, so you have a hierarchy structure of value-key pairs that eventually form the full profile logic. Let's briefly look at the two sample rules here, taken from the Popular Software.xml profile.
For Windows Media Player, we have the name definition. Then, we have the path, which comes with a wildcard. Then, we have three mitigations listed, and their status, false/true. For SEHOP, we also have the minimal OS version, which is the Windows NT kernel version, where this mitigation can be used. So if you deploy this profile in Windows XP, it will not work.
For Skype, we have another new field, which is the architecture, Intel x86. This means the mitigation rules will probably not work on Windows RT, which uses ARM, for example. Again, some of the mitigations have been turned off, because Microsoft knows they might cause problems. We're talking about the recommended settings, so you can definitely make changes.
On top of that, you also have defaults, so you need not apply everything all over again for each and every application. The XML files also have a somewhat lengthy comment section at the beginning, which explains in thorough geek lingo how things really work, but you definitely need a more humane guide like this one to figure it out all properly. And the comments also come with a number of spelling errors, believe it or not.
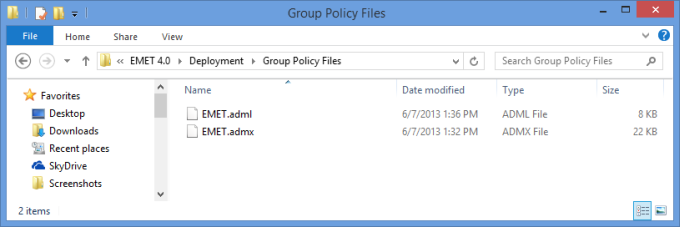
Lastly, for Group Policies, you get the EMET.adml and EMET.admx templates under Deployment\Group Policy Files, so you can use those for configuration of the hosts in your domain. But this tutorial is mostly aimed at home users, so we will skip this setup, and only revisit it if there's serious popular demand.
More reading
You will be most wise to read all of the below, carefully:
Microsoft EMET v3 overview
Microsoft EMET v2 stuff
General safe web and mail security practices
Once upon a time, there was SuRun for Windows users
Conclusion
I stand by my word. Microsoft EMET is the dandiest security toolbox for Windows, and this version 4 is no exception, It's about creating a fire-and-forget security setup that will not prompt you in real time, will not toll any resources, and will not let you make silly yes/no mistakes, while offering genuine, proven security.
Alongside this important message, you get a very detailed tutorial that explains in rich details the ins and outs of this software and the associated technology, and how you can configure EMET for your system and applications, so that you enjoy an unobtrusive and efficient security setup. I hope you liked it. You see, I'm not all negative about Microsoft, sometimes they do make amazing products. There you go.
Cheers.