Updated: December 17, 2010
Technology is not a panacea, so they say. It's one of the 10 immutable laws of security, according to Microsoft. Well, security is not a panacea, either. Perhaps it's a paramecium? While we're trying to be posh in Latin, the average Joe has no idea what we're talking about. For that matter, I don't know what panacea is in regard to security.
I do know that most Windows users are at the mercy of security companies and security poachers alike. While the latter try to make money from the honest and gullible, the former try to scare them into buying cures against doomsday scenarios. So how about you stop meddling in tactics and go for a strategic solution? How about a Microsoft tool that offers that, for free?

Introduction
EMET is a new security solution from Microsoft. It's a whitelist tool, meaning it does not need constant signature updates to work. The tool does not try to predict malicious behavior, either. No signatures and no heuristics. What you get is system hardening.
In a nutshell, EMET performs input validation against various bits of code in your programs, preventing exploits of possible holes. It's not rocket science; it's basic programming. Hence, the beauty of the solution. It's simple, it's fundamental, it does not rely on the user, it takes no system resources, and it just does what it's expected to do.
You get one or more security mitigation applied to your programs, sort of like policies. From that moment on, the programs will run in a restricted mode, unable to do illegal operations that might lead to security risks.
But it's not all golden magic. The caveat is that if the programs are written in a bad manner so they must perform illegal operations as part of their routine functioning, such operations will be blocked and your programs will crash. Therefore, using EMET could in theory impair your legitimate programs, through no fault of its own.
Anyhow, let's see how this thing works.
Installation & use
Installing EMET is very simple. Click, click, next.

EMET has a very simple GUI. It's a control interface, allowing you to easily apply one or more mitigations on your system. Some of the technologies will not be available on certain editions of Windows. For instance, XP does not have ASLR, which was introduced in either Vista or Windows 7. DEP, on the other hand, in an old friend.

Click on Configure System to change the system-wide settings. For instance, you can reconfigure your default DEP policy using the tool - instead of going via the right-click into My Computer properties and digging for the right option.
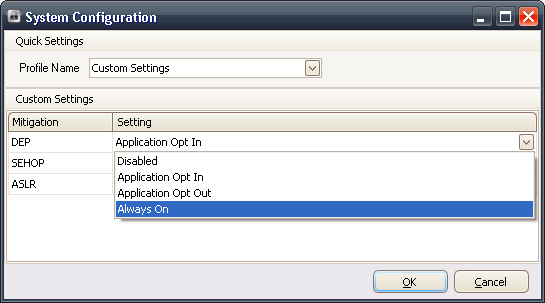
Similarly, you can configure applications in the bottom view. Unlike the system settings, which may or may not be globally enabled, here you can fine-tune the mitigations for each program separately, across a range of geeky categories.
Click Add/Remove to manage the list; the list will be enforced based on the path. Personally, I think using several methods, like those available in the Software Restriction Policies would work better to ensure the correct programs are flagged at all times.

Now, remember that some programs may not like your changes. In fact, down the road, some programs will definitely NOT like the limitations. So you may experience crashes now and then. Your best option is to test slowly and carefully, one setting at a time.
An alternative approach is to enable everything and reduce per-application restrictions one at a time, until you are satisfied with the results. If you're using other security measures, like limited account, UAC, sandboxing, and other stuff, you could see a complex interaction, so keep that in mind. Furthermore, don't introduce EMET alongside other programs. And make sure your system is stable, so you don't mistake configuration issues for the new mitigation policies.
After enabling the settings you want, you will need to restart the programs for the changes to take effect.

After relaunching the program, take a look at the column labeled Running EMET. It will tell you if the particular process has the mitigations enabled. You may need to refresh the list of running processes by clicking on the green icon above the table.

Process Explorer
If you're a geek, you can verify that EMET is enabled for your processes even after you close the main GUI. Oh, by the way, that's the beauty of it. Once you close the main program, EMET keeps on doing its magic. For all practical purposes, the impact on the end users is none.
Open the Process Explorer and take a look at the DLLs list in the bottom window. You will see emet.dll attached to the process, which means it's running with the extra protection.

And here's a handful of screenshots on Windows 7, just for good measure. Notice the difference in available and enabled mitigations.


Bonus: Command line
EMET also has a command line, so you can easily script and automate the use of the tool in your environment. Indeed, EMET has been designed with system administrators in mind, so they can deploy the utility in the background, without anyone noticing.
For more about EMET command line, take a look at the user guide, which comes installed along with the application.
Should you use EMET?
If you google for EMET, you will learn that the tool successfully managed to stop the latest slew of exploits in various Adobe products. This means that even if you are running an unpatched, vulnerable program and stumble upon a piece of malicious code that might try to break through, there's a fair chance the extra mitigation will prevent the code from executing. Sounds good.
You can still go for traditional solutions, like anti-virus and suchlike, but I would advise you against it. Not only will you be wasting your money and resources, you will merely be reacting to threats. Speaking of poor windows users, the stupid scare mails keep on coming.


The legendary classics keep coming. Superb uniform styling and formatting. Click here to verify your account. Your PC and everything on it is at risk. Blah blah. You're better off trying a whitelist solution. It's cheaper, too.
More reading
For a long series of articles on security, you may want to take a look at these:
Safe Web practices - How to remain safe on the Internet
Mail security - Keep your inbox safe
Group Policies - Beginners' guide
SuRun - SUDO in Windows - Tutorial
Windows 7 security - Everything you need to know
Windows 7 security - A few tips more
How to improve your Windows security
Conclusion
EMET is an excellent security concept. It goes down into the heart of problem, the code itself. Rather than letting users go wild with their imagination and ineptitude or relying on third-party vendors to cook out solutions for their operating system, Microsoft has come with a smart, robust whitelist tool that works against known and unknown threats.
It's dead easy to configure, it tolls no resources and it extends into the realms of unknown, which makes it a fundamentally ideal solution. As a geek, you should start using EMET. Then, once you're satisfied with its potential, have it deploy on the computers of your less skilled friends and family.
EMET is a work in progress and has yet to grow to full potential, but it looks like a very promising security solution. It seems like Microsoft are starting to get serious about their stuff. They nailed it with Internet Explorer 9, and now this. Not bad.
Anyhow, take EMET for a spin and enjoy yourselves.
Cheers.