Updated: May 19, 2017
I've used quite a few printing devices in my life, but never a Wireless printer. Recently, though, I decided to buy myself a somewhat cheapish, or should I use the more accurate term, budget all-in-one printing device, HP DeskJet 3630 All-in-One, which, among many things, also comes with Wireless connectivity.
Going cable free sounds like an interesting concept, so I decided to configure the device to be accessible using its Wireless functionality. Midway through the setup process, I began wondering what kind of security this printer might have. It all sounds so mysterious, and there might be implications to end users. Hence, this guide.
Ground rules
First, let's begin with a few clarifications. One, I will be writing about my particular model, but the principles outlined in this article are true for any printing device. In fact, any IoT device out there. The things I've written on router setup and security a long time ago still holds valid, and this tutorial follows the same idea. You need to treat your network-facing gadgets with a little bit of care and some small attention to details.
So what would a printer be, one that is capable of Wireless connectivity? It's a small computer that can produce nice pages of text and color, and it also runs a Web server. Popular terminology for this is Embedded Web Server (EWS). That sounds less glamorous than the notion of your printer being some blackbox that can phone home, order your ink and do all sorts of magic. Nothing of the sort.
But this means one thing - if it has a Web service, it means it listens for incoming connections. Therefore, we do need to make it secure, and this is a fairly simple and maybe even fun exercise. We will do it now, and if you do the same with your IoT devices, you will significantly reduce the noise levels and possibly some risk involved in letting them run with default user rights, open connections, no passwords, and such.
Access the Web server
After you've setup your printer, you will need to access it using an IP address. What might it be, you may ask? If you're savvy, you can scan your network to find it. For most people, this will be a local IP address in the LAN, as configured behind your router. The router may also be an ISP appliance, a streamer box or any connectivity device that lets you hook up other machines behind it, and let them all play and chat nicely to each other. Another way of doing this is to access the printer properties, which will open a browser.
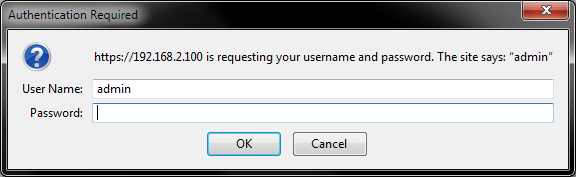
In my case, the printer had been allocated the first available IP address in the router's DHCP table, so it was granted 192.168.2.100. The connection is not secure by default, which is not a major concern if you connect using wired network from a desktop.
Tip 1: When trying to secure your printer, as there may not be a secure connection, do it over a wired network, at least until after you've configured the settings.

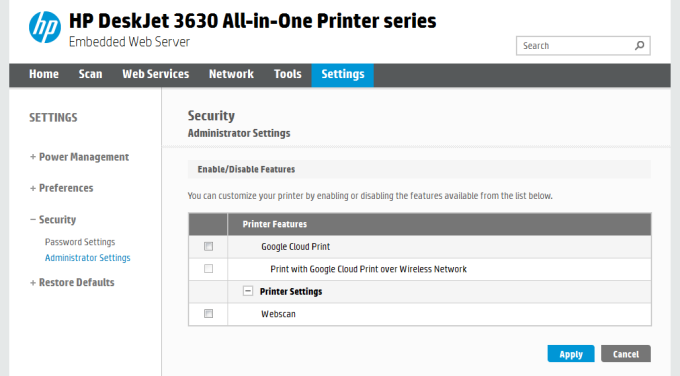
On this page, you can configure every aspect of your printer device. This is just like any router's main page, and you should carefully go through every single option to fully understand what gives. Now, the bulk of interesting things will be under Tools and Settings, of course.
Wi-Fi Direct, AirPrintTM
HP advertises this particular model as being very easy to use for printing from a smartphone or a tablet. But what does that actually mean? If you think about it, mobile vendors are very anal when it comes to driver installations, so unless you can find a driver in an application store, you probably won't be able to install it. Drivers also require elevated permissions, and they can be quite messy.
So the alternative is provide some kind of quick, Web-like connectivity for mobile devices, and this is exactly what these two protocols allow. The idea is good, but it cannot be designed as secure, because it limits functionality.
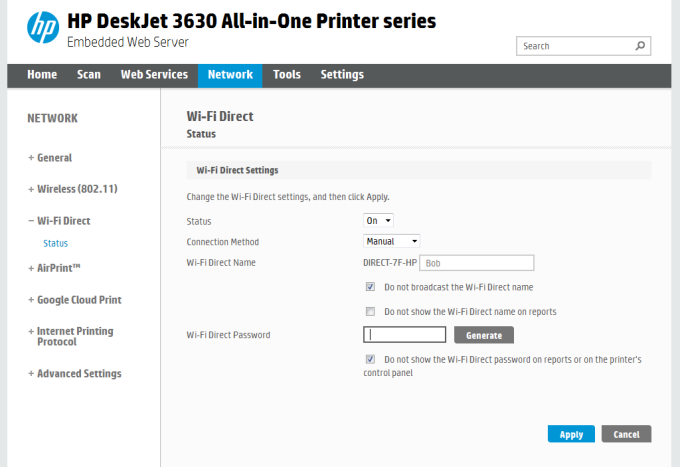
Indeed, Wi-Fi Direct comes with a default name and password, which are true for any printers of this series, and probably dozens of other models. Much like any admin:admin setup. So you may want to edit the settings, change the defaults, or even completely disable this service.
Tip 2: Edit default user names and passwords for enabled sharing/connectivity services that may exist on your printing device.
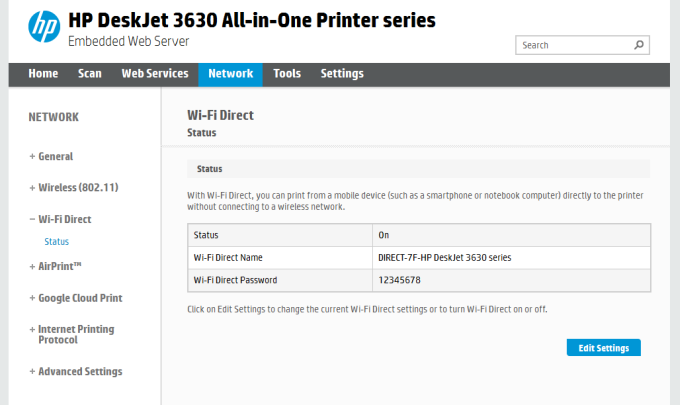
To be fair, you can really tweak this service. Enable/disable it to begin with, change connection method, name, password, broadcast options, reporting, etc. Quite handy. This is your first step to gently hardening your printer. It's not like l33t hax0rz are going to pwn you any moment, but you should really not be using the defaults. It's disrespectful to yourself and the wider Internet, even if no one is going to actually be using your network or your printer.
AirPrintTM is a similar concept for Apple products. You can even geo-mark your device. Specifically for this particular printer, I did not have the option to turn AirPrintTM off, which looks worrying, but it is not. Later on, as we go through the Web interface, we will see this service, and the additional services that it depends on, can be disabled.

Internet Printing Protocol (IPP)
This brings us to the next step in our printer configuration. We will come back to Google Cloud Print shortly. Anyhow, your first impression is that you may need this functionality to print over the network, because Internet and such. Nope. If you do not plan on accessing your printer outside your home LAN, disable the protocols.
Tip 3: Disable services you do not need.
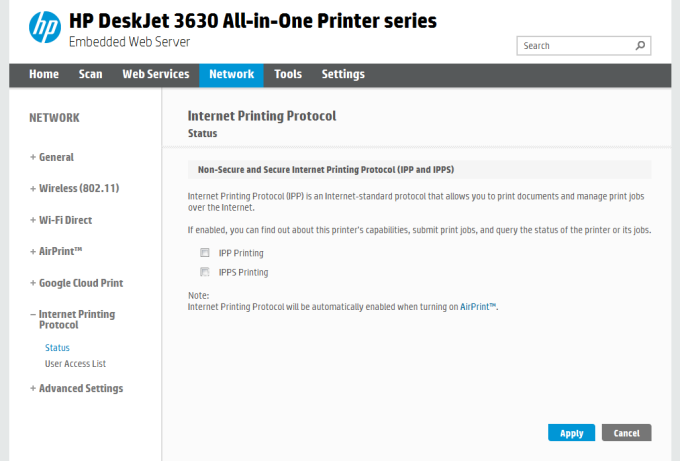
User Access List actually specifies who can connect. But this might not be the smartest thing in the world, because access lists are usually trivial to circumvent. Moreover, you cannot really print from the Internet if you do not configure your router to actually allow incoming connections. So this really means opening a port. That's not an ideal thing for most people.
Bonjour
Top of the morning, sir! Bonjour sits under Advanced Settings for HP 3630. What it does, it's a zero-configuration networking implementation (by Apple) designed to help with the discovery and name resolution of devices, such as your printer. In other words, if you do not use Apple products or do not intend to use AirPrintTM, you can disable Bonjour, which together with IPP will turn AirPrintTM off. Bob's your uncle.

Other configurations
Certificates
In general, most printers will use a self-signed certificate for pages that need to be displayed in a secure manner (HTTPS), such as the page where you can change the admin password. You can change certificates, but this will reset existing connections. Simple Web stuff.

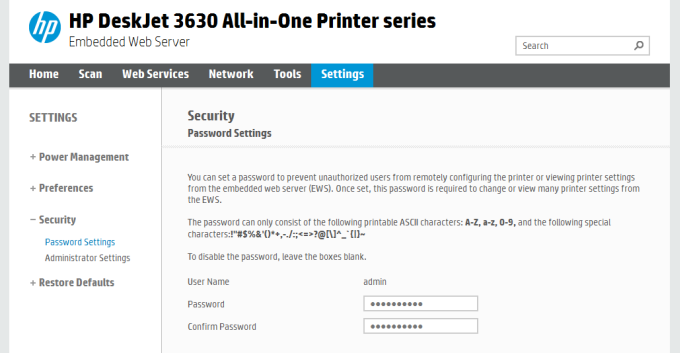
Admin password
Password management is usually done through a basic .htaccess file, which prevents people from reaching the configuration page and messing about. For instance, my printers comes with no password at all. Change it to anything you want. Remember tip 2. Like they say in Ronin, what's the second thing they teach you in CIA? Also, do remember that some printers may store your password in clear-text. So you may want to go for something other than your bank account credentials. Kapish?
Firmware updates
It can be helpful to keep your printer's firmware up to date. Normally, I am quite wary of firmware updates, as they may introduce products, brick your device, or reset your settings, but they are important for Internet-facing devices, especially those that are capable of running services. Budget IoT stuff usually comes with lightweight security, and they are often easy to exploit, so you might also want to consider firmware upgrades now and then. Remember, this is a little computer, and it might need some love from you.

Other services like Google Cloud Print, Webscan, etc.
Google Cloud Print one isn't trivial, and it is also not enabled by default until you've actually allowed your printer to connect to Google's services and share your printer's unique ID. So this one will not really be an ET Phone Home capability unless you explicitly do it.
Webscan, again, you get the idea. Do things locally, on your network, or let people, including yourself, do this over the Internet. Now, everything the printer does ignores the actual router settings and firewall, so most of the stuff won't work, even if enabled, but it is always good to be the master of your destiny, like He-Man.
Last but not the least, you should also think about IPv4 versus IPv6, proxy settings, network identification hostname, by which your printer shalt be known. Again, for some odd reason, I'm having these Monty Python and Blackadder flashbacks. I guess the printer should be called Tim. Or Bob.
Conclusion
There you go. Now, please do not forget this tutorial uses one specific printer model to showcase the basic principles of security for Wireless printers and other generic IoT devices. Some options, features and settings may be missing, or your device might not have all of what is discussed here. Do not let that discourage you.
Ignore the noise and the hype and the million acronyms and trademarks. Your printer is just a computer that can do some physical stuff. Nothing more. If it runs a Web server, it should be secured. Configuration over wired connections or secure HTTPS Wireless connections if possible. Disable unnecessary services. Change default passwords, usernames and identification strings. Consider firmware updates.
In essence, this is all you need. True, the setup process can take a couple of hours to fully go through, check and tweak to suit your needs. And remember, any option you turn off also means less functionality, or at the very least, immediate functionality. If you do not allow zeroconf services, it is likely your tablet or phone won't print. And if you do not allow any over-the-Internet features, you won't be able to use this device when away from home. It's a tradeoff between convenience, security, paranoia, and risk. But then you are reading this article because you are ever so slightly concerned about your Wireless printer. Well, hopefully, this tutorial has cleared some of the fog and uncertainty. IoT devices may sound like wild AI-powered things that constantly spy on you, but they can also be useful, practical modern commodities. Just double-check the settings, and this guide is a neat starting point. We're done.
Cheers.