Updated: February 14, 2011
Normally, I don't bother responding to this or that article. But abnormally, controversial and provoking pieces of journalism slash marketing slash fear-mongering slash evangelism slash attention-seeking articles do trigger a response. Today is such a moment.
A few days ago, Paul Ducklin of Sophos, an anti-virus vendor, wrote his piece where he rants about Linux users' unwillingness to use anti-virus products on their machines. It all started when Sophos was given a VB100 award for Ubuntu, to which a handful of Linux users responded, to which Paul responded. To cut the long saga short, it became a publicity stunt laced with flame and trolling, all of which garner clicks, views, comments, and awareness. Now, it's my time to pipe in.
I will give you a lucid, objective, fair, and transparent view of how things ought to be, and what you get when you listen to either Paul and his business-oriented view on what reality looks like versus the community of angry anti-Microsoftians. Let's go.

Motivation
Asking an anti-virus vendor employee or affiliate about their products is like selling ice to Eskimos. Paul is the Head of Technology with Sophos. He has a clear agenda here. He wants to promote his company, his products, get more money. Simple and fair in this material world we live in. But, but, but, but, but for exactly this reason, he is not the authority to ask whether you need anti-virus software. In fact, this very reason invalidates him from being the source of advice and wisdom, even though objectively, he might be correct. Which is completely irrelevant here. Ask your insurance salesmen whether you need a policy. Right.

So what Paul did was make himself completely lose all credibility for the simple reason of being the champion of his cause. It's a paradox and the prime example of troll feeding. He was baited, he responded and he got into a flame war. Not only is this not dignified, as his nemesis might have been a 14-year-old living in him parents' home, but he also got into an impossible situation where you argue online. I will not paste the classic image of the Special Olympics meme here, but you know what I'm talking about.
Sophos may or may not have credibility. It may or may not succeed selling its products to Linux users. Marketing stunts could play a role here. But if they are going to be challenged by forum posts and commenters, then the company has a much bigger problem than the quality and effectiveness of its software. Now, let's move to the actual flame war and then some technical details.
Argument 1: Spreading of malware
An angry Linux user writes thusly:
I object to running a Windows virus scanner on my *nix systems just to help prevent the spread of viruses to/from Windows machines. They want to run an insecure system, so be it, but leave me out of it. And certainly don't expect me to expend my CPU cycles to try (in vain) to solve Windows' security issues.
Paul responds thusly:
Wow! With friends like that, who needs enemies?
There's more valiant fencing and whatnot with diseased animals and food used as a very bad analogy to the whole situation, but the counter-argument to above is:
The first comment doesn't actually say that Unix is secure by design. It takes an "us-and-them" attitude, and simply says that "they" are insecure.
Okay. So we have two things here. One, whether Unix, although I was under the impression we were talking Linux here, is secure by design. Two, whether users have the moral obligation and responsibility to stop malware in its tracks.
To answer question one, read my first of three Linux security articles. To answer question two, read my second Linux security article. In short, you do not need anti-virus software on your Linux box, period. For that matter, you do not need anti-virus software on your Windows box, either. Yes, read that twice so it can sink in.
Furthermore, on moral obligation: no user, Windows, Linux or elsewise, has any obligation to prevent the spreading of malware. For that matter, we should all also stop spreading spam, right. But spam includes 90% of all stupid content out there, useless blogs, Youtube videos, MySpace, Facebook accounts and whatnot, and everything else. It's not just about mails.
Malware is one facet of undesired content and it's no more harmful, detrimental or boring than the rest of it. Personally, I find reality TV crap to be more harmful than malware, since I can avoid malware easily, but I can't avoid my colleagues talking about Big Brother or similar diarrhea.
Second, users PAY MONEY to their ISP companies for the quality and availability of service. Users are not knowledgeable or skilled enough to know and discern what malware is. Users are not paid to play Internet police. Companies providing services must be responsible for whatever goes on through their wires.
It's not about us being nice and whatnot. It's not about spreading malware. It's about not having malware in the first place. Because if you do not get any, you don't spread any. Very, very simple. If no user ever forwarded their executable PowerPoint nonsense, then no one would ever have to bother with the Delete key on their keyboard. It's almost magical, the simplicity thereof.
Now, the big question, how do you avoid malware?
Well, regardless of what operating system you use, it's terribly simple. You don't execute crap on your machine. But some of you may shout, Dedoimedo, what about them embedded Flash and PDF exploits and suchlike? Boring.
Without repeating myself endlessly, let me just point you to a handful of mainly-Windows related articles on security. They all pretty much link to one another, so you are bound to get to read them all if you want:
Safe Web practices - How to enjoy Internet and be safe, without unplugging the cable.
Mail security - How to enjoy mail communication with peers worldwide without getting lost in spam and alluring offers of vast richnesses.
SuRun - How to run a limited account on Windows, easily.
Windows 7 security - Basics of security in the newest Windows release.
Windows 7 security - A few tips more - More basics of security for Windows 7.
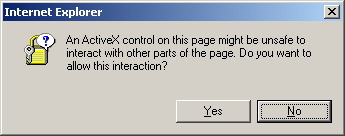
Windows messages - Learn how to answer those prompts, correctly.
How to improve Windows security - The revolutionary theory.
EMET - A new Windows security mitigation toolkit - The easy way around bad coding.
Linux security - A few useful, tactical tips - Some old-school tricks for Linux.
All right, relaxed? Good. Now, let's discuss the second part of this flame retort, which would be the existence, prevalence and significance of Linux malware.
Argument 2: Linux has malware, like more than 9,000 of those
Hide! Now! The Armageddon hath begun. Wait. The second part of Paul's piece elaborates on how Linux is vulnerable, too. To prove his point, he tells a story of some 12,000 unique IP addresses of Linux machines infected with some who-cares Linux virus between May and June of 2008. He makes his argument harder to fight by showing you topological maps of Europe and North America, the two pieces of our globe that seems to matter, pimpled with red dots of infection.

Now, to be fair, Paul wraps his piece with a fairly moderate message. Linux malware exists, it can be easily avoided. Windows machines can also be secured properly. Stop hating, start participating. All right, so let's walk through Paul's piece.
First, the conclusion ... Yes, he got it more or less right. But I fail to see the magic dot between malware and anti-virus software. In fact, if anything, Paul tells us that malware is not a big deal, as a would-be serious Linux malware managed to infect the staggering lot of 12,000 machines. Staggering, in double quotation marks, for the slow amongst you.
In 2010, 134 people were injured by toilet seats in USA only! Holy banana! Does this mean toilet seats are dangerous? Or perhaps, there are people out there, who frankly, should not have joined the global genetic pool in the first place?

The reason 12,000 Linux machines were compromised does not indicate any malware problems. It shows that users, given the right amount of permissions, will self-inflict damage. The fact these are possibly administrators of SOHO networks is a little more troubling, since someone certified these people to do their job and given them job offers. However, truth to to be told, we do not really know anything about these machines.
But there's nothing in the computing model design, no matter how evolutionary or revolutionary that can prevent stupidity from taking its toll. On average, Linux users happen to be more skilled, but there will always be people prone to cause harm. It's just the matter of percentage.
It comes to down to the user. That's all. It has nothing to do with malware or Windows or anything of that sort. There's a long list of things that need to be sorted out before we ought to give the malicious code a glimpse. Like people keeping files on their desktop, for instance.
Now, let's go back to the first piece of the second part of his flame, the infections map and statistics. First, everyone can invent figures on the spot, or at least twist them into any kind of semblance of reality they want. PhD students do this all the time. This is how the world of academics run. Outliers this, outliers that, bad weather, a software glitch, you polish out the numbers to prove what you want to prove.
Second, fear-mongering is really so yesterday. You may be an average person and have this deep desire to watch news casts every day, listening and believing to anchors telling you about the dangers of the world, but the reality is a little different. And the same applies to software. Nothing is happening. Nothing at all. If you decide not to participate in the herd mentality, then don't. As simple as that. You don't have to be the masochistic guinea pig of the global scarefest.

Saying malware of Linux exists is like saying Ebola virus exists. So? How is that relevant to anything? Why should you care? How does that make your life any different? If you take a look at the infections reported by Sophos, we're talking 2008, almost full three years ago, as relevant today as Mayan prophecies. Then, considering the fact that at least 65% of world's infrastructure and computing resources use Linux, in conditions that mandate older kernels and infrequent updates and root privileges 24/7, then 12,000 machines sounds awfully little.
On top of that, we may also assume that some of these machines were improperly configured and exposed to the external world, with their owners not having the time, ability or knowledge to follow up on the infections, whether by being able to monitor and identify the problems as well as resolve them and patch the systems.
So we have several layers of FAILURE by design and use that could have resulted in a million outcomes other than malware infections. Bad configurations and servicing and buggy software will normally cause disruption of service, outages, corrupt data, and a lot more, all without any regard to any third-party malicious code being executed on the target host. And frankly, if you ask me, I'm more worried about hosting companies not validating their database inputs and keeping encrypted backups and such than someone having an extra entry in their process table, called virus-whateverd. The extra d is not a typo. Finally, a little fear-mongering poster, just to show you the beauty of it all:

To sum it up
Message to Paul: Your program got its award. Why do you care what anyone else thinks? Your salary is probably higher than those of all your commenters combined, so why bother wasting CPU cycles on flames?
Message to the world: Anti-virus software is a state of mind. It's software, just like any other, and it could work for you, if you are convinced that it does. It's a self-feeding dependency cycle. For most people, the truth is irrelevant. What more, the truth can be frightening. The absolute reality of either Windows or Linux security is so trivial and boring that it makes people scared. What are they going to do with their lives now that they do not have some greater evil to worry about? They might actually start wondering if there might be something really wrong with their computer usage, after all.
Second message to everyone: Integrity should play part in the world of business, but it takes a honorable last after profit, more profit and yet more profit. The fact Sophos could have an excellent product is irrelevant. The fact that in the long run, it may or may not be contributing to the quality of Internet services and peace of mind of users is irrelevant, too. What people get riled about are the little things. They won't remember infections or numbers or wasted CPU cycles or ideology wars. They will remember that some salesman tried to preach his holy sermon and take personal grudge. Not as bad as some, but still not quite as elegant as you might expect.
Conclusion
What has Paul's piece really shown us? Three things, mainly. One, even senior executives of software companies can be lured into a flame trap. Two, statistics are overrated. Three, when you are so desperate to champion your cause, you actually scare people away.
Additionally, we also learn that Linux malware can be brandished like a weapon in all kinds of arguments. And for all the wrong reasons. Because malware itself is nothing important, just a symptom of a much larger phenomenon. Today, a user may execute a stray binary on his machine. Tomorrow, that user will wipe his files off the hard disk. It has nothing to do in how the code manifests, it has everything to do with granting unskilled people with the power to destroy.
We also learn that arguing online is absolutely pointless. People do not need reason, logic or hard facts to believe in their imaginary ideas and promote them. If someone is convinced they are not supposed to be saving their Windows buddies, there is no amount of numbers, graphs or technical explanations that could convince them. And the other way around. Some Windows users will prefer the shackles of fear to the terrifying liberty of boredom.
I don't know who Paul is and have never heard of him until his last article. So if his hidden agenda was to carve his name in the wider consciousness of Linux users worldwide, he has definitely succeeded. Whether his flame retort helps promote Sophos is questionable, even if it is not explicitly stated in the article, which makes it insidiously cunning. One thing is sure, if you know that Linux users will never use your product, then you might as well give them a good fight.
Cheers.