Updated: December 22, 2008
A friend of mine asked me how to do this, so I decided to write a tutorial. If you're using both Windows and Linux on several computers, a need might arise for you to connect to the Linux machine now and then. Your Linux machine might serve many purposes: it could be a server, a media center (like MythTV), a backup storage area, or just another desktop. You may want to connect to this machine - or even control it. Well, for sharing, we have Samba.
Configuring Samba is very easy. I have demonstrated this in several articles. You can find detailed
step-by-step instructions in the reading section below. Now, for remote control, we have this tutorial. Let's
see how we can configure our Linux box to be remotely controlled from Windows.
I will demonstrate how to take control over a Linux machine using SSH and VNC. SSH stands for Secure SHell, a network protocol that allows you to exchange data between two connected network devices using an encrypted tunnel. The tunnel is not limited to just transferring data. You can use it to control the machine on the other end, forward insecure applications through the tunnel and more. VNC stands for Virtual Network Computing, a desktop sharing system that allows you to control other machines.
Prerequisites
Before we begin, I would like to point out that the purpose of this tutorial is to demonstrate how remote connectivity and control can be achieved. It is not a comprehensive security guide into the pitfalls and dangers of opening a port to remote connections and the integrity of transmitted information. This tutorial assumes a safe network where both ends strive toward a mutual goal.
If you plan to deploy a setup like this over the Internet, you must be aware that there could be people who might try to break into your system and take control over it. Or they might want to sniff sensitive data you exchange using these protocols.
A local area network (LAN) setup behind a firewall is one thing. A world-wide open setup is something else entirely.
At the very minimum, the use of SSH or VNC over the Internet will require the use of firewalls with logging enabled, mandatory encryption with long and frequently rotated keys and strong passwords, non-standard ports, a limit on the number of unsuccessful attempts, a time limit between failed logins, no root access, and possibly even other security precautions.
In our setup, we will talk about a cozy LAN at your home or an office, far from the dangers of the Internet.
So, now that we know what we're about to do, let us begin, VNC first.
VNC
We will demonstrate using Ubuntu (8.10). Ubuntu comes with the VNC software already installed. You only have to configure it for remote access. Furthermore, Ubuntu makes things simple by using no firewall in its default configuration, since it comes with no open ports - and thus, the use of a firewall is unnecessary.
Ubuntu uses the Vino program for VNC connectivity. You can power Vino by going to System > Preferences > Remote Desktop. This will open the configuration menu for Vino.
Now, we need to check several boxes: Allow other users to view your desktop and Allow other users to control your desktop. We also want security, so we will require a password and a confirmation.

Under Advanced, we can further configure the connection. Encryption is strongly encouraged. You may also want to consider a non-standard port.

Check that your VNC port is open now. You can use nmap to do that. It's included in most distributions or can be easily downloaded from repositories.

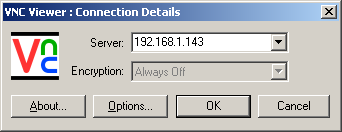
Now, we need to configure the Windows machine. We require a VNC program to connect to our Linux box. Therefore, download a VNC program and install it. There are many choices, but your easiest best is either RealVNC or TightVNC. Once you launch the program, specify the address of the remote machine:
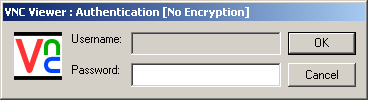
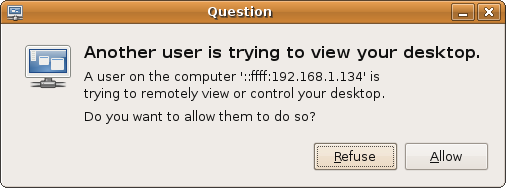
P.S. Please note that your choices may differ. It depends how you wish to configure your software. In this case, I made no adjustments and just fired up the program with the default options set. On the Ubuntu machine, you'll be asked to confirm the connection attempt:
And here we have a Linux box controlled by a Windows machine:
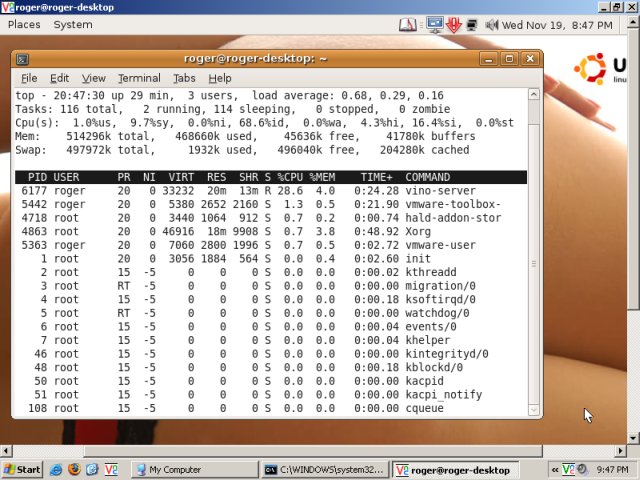
Job done. Easy peasy.
SSH
This time, we need to install the ssh package in Ubuntu. Some distributions will have it installed, others will have it in the repositories. Once it is installed, either via Synaptic or the apt-get (on the command line, sudo apt-get install ssh), check that the SSH port is open:
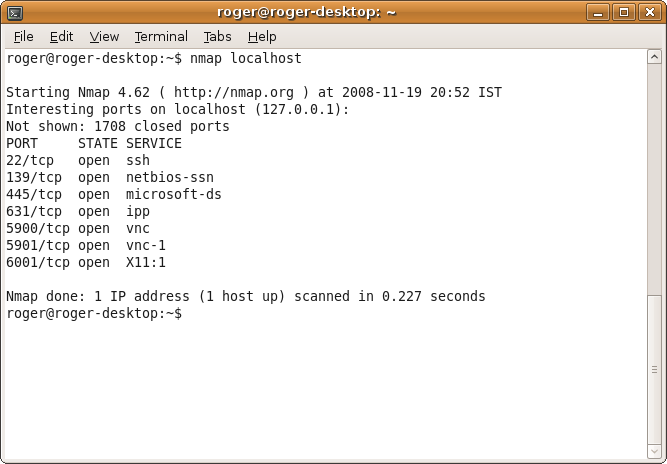
The default port is 22.
Now, in Windows, install an ssh client software. A good choice is PuTTY. It is simple, lightweight and will also run from removable media like USB drives.
PuTTY is a command line tool. Open the command line (Run > cmd), navigate to the PuTTY folder and run PuTTY against the remote IP address, something like:
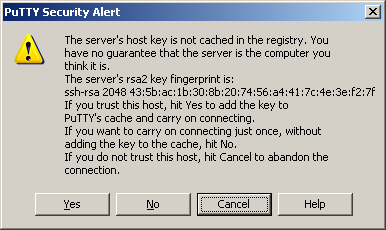
You'll be asked to import the key of the remote machine. This is a security precaution, so that you really know you're connecting to the computer you want.
Authenticate with the password:

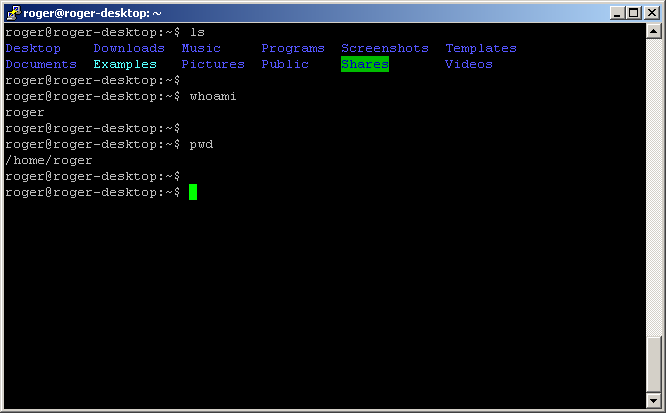
And you're logged in:

Now start working:
More reading
And a few more links you might like:
Installing PCLinuxOS - Full tutorial - Page 4
Sharing folders between Windows and Linux
Conclusion
The task of establishing a remote connection with Linux machines is a very simple thing. The entire procedure should take you less than 5 minutes. Of course, if you're trying to achieve this in an insecure environment, you should take many necessary steps to make sure that both your Linux machine, your client and all the information you're about to exchange are safe from intrusion, snooping or other potential dangers. This means strong encryption, non-trivial passwords and several other tricks.
In your home environment, where the task is so much simpler, there are simple and easy-to-use tools for the job. If your Linux machine serves a file or printing server, a media center or is simply located beyond the reach of your lazy fingers, gaining control over it takes very little effort.
In the case of ssh, you may also want to use remote connectivity if you're short of another monitor or just to practice Linux command line. Either way, it's simple - and fun.
P.S. If you find this article useful, please support Dedoimedo.
Enjoy!