Updated: August 26, 2016
Recently, I have begun exploring alternative tools to Windows Update, in order to help solve the issue of slow updates. My quest took me down the shadowy path of several official patches, which had not yielded the desired results - more to come on this with some good results, stay tuned. Then, I tried Autopatcher. The tool was mostly safe for use, but it is not 100% accurate, and there is some small risk associated with possible future complications.
WSUS Offline is another such tool. It is designed to give you a relatively fast offline capability for Windows and Office updates, similar to what the standard WSUS tool does. Anyhow, let's see how well it competes against Autopatcher, and if it provides the right amount of safety, ease of use, and good, solid functionality to become our favorite updater. Commence to follow.

Analyzin', analyzin'
WSUS Offline is less intuitive. Period. Even running the tool correctly takes some small guesswork. It also comes inside an archive, but then, there are two separate binaries. UpdateGenerator.exe is the main binary in the top directory, and it is used to pull downloads from the official site. UpdateInstaller.exe is the tool that you actually run to configure and install the updates once they have been downloaded by the former, in a fashion somewhat similar to the two options offered by Autopatcher, except these come as two separate tools. To make things a little more complicated, the installer is located inside the client sub-directory.
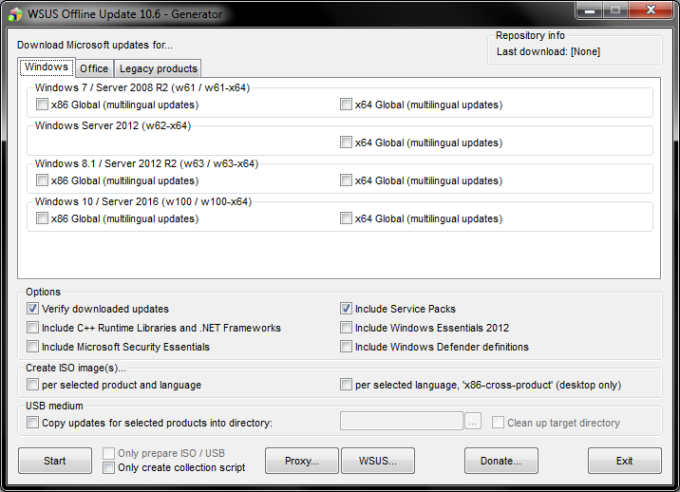
The main interface is a little busier than Autopatcher, as well. You can select releases separately for Windows, Office and legacy products. Both Windows 7 and 8 are covered, and you can add additional runtime libraries, security tools, .NET stuff, and Windows Defender definitions.
The very neat thing about the program is that you can actually create an ISO image with the updates, so you can easily distribute them to other systems, and even use your own official WSUS servers as the source, rather than going to the Internet.
Once you start the download process, WSUS Offline will spawn a command line window, and you will be able to monitor progress there. It is slower than Autopatcher, although the overall number and amount of patches is only about half of what the other program offers. You go through the usual motions of check, compare, download, validate. The command line stuff makes it all the nerdier.


Once the download is complete, you will be able to check for warnings. And the program will prompt you for updated releases. The total download process took about 2 hours for roughly 205 updates.


Installer
The next step was to run the actual installation. But being slightly confused, I tried the generator. It ran for a long time, so I'm not sure if it keeps and compares the cached data, because I was under the impression my bandwidth was being bled in vain. Whatever the actual technical reasons, WSUS Offline seemed to have a very slow rebuild of the indexed data. The workflow was also convoluted, with the two binaries and their non-uniform placement. And then, there's the IE11 prompt when you start the installer the first time, which tells you your browser will be updated to the latest version, and this does not help either.


At this point, I was a little reluctant to proceed, because I was not sure what the system would do. I didn't have any visibility into which updates would be selected or why. I have not had any chance to select or mark anything. The fact the generator had run twice for such a long time and seemingly redownloaded everything did not inspire me with confidence.
But then, most interestingly, it actually installed the ONE patch that Autopatcher had missed, re-indexed what's missing and what's not, and grabbed two more files, which corresponded to other leftovers. I'm not sure what the logic is, but it seems to cover the stuff omitted by Autopatcher. The malware removal tool was also skipped, which is good. The process completed successfully, and I had my Windows login prompt after the reboot. In the end, all's well that ends well, but I didn't have the right amount of control that I expected, especially when it comes to choosing individual files.
Medium build date: 03/18/2016
Medium supports Microsoft Windows (w61 x64 glb).
Checking Windows Service Pack version...
Checking Windows Update Agent version...
Checking Windows Installer version...
Checking Windows Script Host version...
Checking Internet Explorer version...
Checking Windows Defender installation state...
Warning: Windows Defender definition file (..\wddefs\x64-glb\mpas-feX64.exe) not found.
Checking Windows Update scan prerequisites...
Warning: Update kb3134214 not found.
Installing Windows Update scan prerequisites...
Installing update 1 of 1 (stage size: 200)...
Verifying integrity of ..\w61-x64\glb\Windows6.1-KB3138612-x64.msu...
Warning: Hash files ..\md\hashes-w61-x64-glb.txt and ..\md\hashes-w61-x64.txt not found.
Installing ..\w61-x64\glb\Windows6.1-KB3138612-x64.msu...
Checking state of service 'Windows Update'...
Verifying integrity of Windows Update catalog file...
hashdeep64.exe: Audit passed
20:57:31.18 - Listing ids of missing updates (please be patient, this will take
a while)...
Listing update files...
Warning: Update kb3126036 (id: 06cd01f0-9dfa-4950-8781-e799958c48ce) not found.
Info: Skipping update kb890830 (Malicious Software Removal Tool) due to matching black list entry.
Stopping service 'Windows Update' (wuauserv) - previous state will be recovered later...
Installing updates...
Installing update 1 of 2 (stage size: 200)...
Verifying integrity of ..\w61-x64\glb\windows6.1-kb2981580-x64_6a7f92da16676c89b
44e102a1979b1870bd3db35.cab...
Warning: Hash files ..\md\hashes-w61-x64-glb.txt and ..\md\hashes-w61-x64.txt not found.
Installing ..\w61-x64\glb\windows6.1-kb2981580-x64_6a7f92da16676c89b
44e102a1979b1870bd3db35.cab...
Installing update 2 of 2 (stage size: 200)...
Verifying integrity of ..\w61-x64\glb\windows6.1-kb3072305-x64_183ac3b173dc02ba9
32c181e555f74e860cec878.cab...
Warning: Hash files ..\md\hashes-w61-x64-glb.txt and ..\md\hashes-w61-x64.txt not found.
Installing ..\w61-x64\glb\windows6.1-kb3072305-x64_183ac3b173dc02ba9
32c181e555f74e860cec878.cab...
Checking Microsoft Security Essentials installation state...
Starting service 'Windows Update' (wuauserv)...
Installation successful. Please reboot your system now.
Conclusion
WSUS Offline is another tool you could use as a replacement or alternative for WU, or as a complementary utility that helps work around the slow updates issues. Whether you should really do that is a different question.
Autopatcher proved to be okay, but not perfect. However, it was consistent in how it behaved and what it did. The final tally was two updates not being in line with WU, and the system was working fine. The errors on the index rebuilt were annoying, but they did not jeopardize the system health. With WSUS Offline, I was more skeptic, somewhat more hesitant. I bit the bullet, and it completed without errors or damage. But it was a bit of a risk.
And so we go back to the same question I asked you when we tested Autopatcher, with even more disclaimers. WSUS Offline seems to be even less intuitive, and there seems to be no way to individually hand-pick updates. Or maybe there is, but I'm missing it. All in all, this is another tool that works fine, does what it promises, but it also introduces a healthy dose of worry that I would not trade for some slowness in the process. You will need to decide what you care about more, and you will need to thoroughly test these two before you choose to use them, if ever. We shall soon follow up with a nice guide that is going to fix all our WU slowness issues. Bye bye, children of the Internet.
Cheers.