Updated: December 26, 2008
Contrary to what many security experts may tell you, I think that an automated, un-supervised deployment of security updates is quite dangerous - and even counterproductive to gaining security. Let's elaborate.
First, some things that you should consider before deciding whether you can entrust the health and integrity of your machine to the vendors delivering security updates and patches in an automated manner.

What if the update is corrupt?
You will certainly want a few million people to find out about this before you, don't you? You do not want to be the first to have a broken system. Let others sweat it. Let the vendor solve the problem first. A few examples that come to my mind:
Microsoft update breaks Realtek audio
Norton anti virus cripples thousands of PCs in China
You're not running a mission-critical server
Your home environment is not a DNS server that must be in top-notch shape at any given moment. Even if you miss an update for a few days, what's the big deal? What can happen? If you're running even the most rudimentary firewall, you're safe from brute-force attacks. If you're not downloading just about all possible and impossible programs and executing them with wild abandon, you're not likely to get hit by nasty, doomsday malware.

You could be running an anti-virus software. Do you really think the bi-hourly update is going to save your skins from the devils of the Internet? Well, if you're the kind of user that gets infected every second Thursday, you may consider changing your security practices rather than tightening the update cycle.
I have Windows machines that have not been updated for months and they run perfectly fine. Most of the updates would be relevant if I were using this or that Microsoft software, like Internet Explorer, which I don't, or running services that listen to the Internet, which I don't.
What if the update server goes rogue?
The likelihood of this happening is slim, but you certainly don't want to be the one informing CERT about it. Blind trust shows trust - on your behalf - but it does not add to your productivity or security.
For instance, do you want Windows Genuine Advantage Notification bundled with your monthly updates? What if you don't want Internet Explorer 7 on your machine? With automatic updates, you'll be worrying about these things after they happen.
What if the update kills your data?
How can this happen, you ask? Well, damaging the operating system is one thing; tampering user's personal, priceless, irrecoverable data is something else.
If you regularly use imaging software to clone your system state before deploying any significant update, you can easily avoid system damage caused by faulty update. But user data is often not included in these kinds of backups, especially if it resides on removable devices, like USB thumb drives or external hard disks. Which is exactly what happened to me. Here's the story:
I was running VirtualBox inside Mojopac installed on an external hard disk, connected to a machine (Windows XP, not mine) that had automatic updates enabled. I did not notice this when I went to have a lunch and left the hard disk connected with all its software running, including a virtual machine.

When I came back, I found out that the machine had rebooted after installing the updates. Oh yes, it had displayed its 30 minute warning, but since I wasn't there to acknowledge or decline the reboot, the operating system went ahead and rebooted, killing my open Mojopac session and my VirtualBox virtual machine without any consideration.
If you're wondering what I'm talking about, please check this article. I do not have an image to show you the desired result, but this article presents the subject in a well-laid manner, so there you go.
Needless to say, the Mojopac was dead, the VirtualBox was dead, the virtual machine was corrupt. I ended up running chkdsk on the drive, which did not help, and had to reinstall everything. Well, you can say it was my fault. But at my home, no machine ever reboots without my explicit permission, so I saw no reason why this should be any different. I guess I was wrong.
The morale of the story
Automatic updates are dangerous - especially if they're followed by a merciless restart. They can destroy your precious work, especially if you have files left open when the feces hit the fan. This is particularly true for Windows machines. Therefore, I warmly suggest you set your updates like this - Turn off Automatic Updates:

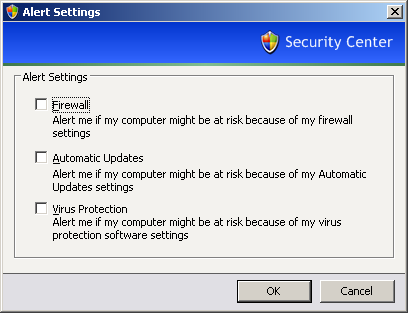
This will require some responsibility on your behalf to manually check and install the patches. At the very worst, you may want to consider using the Notify me. The Security Center will probably nag you, but you can turn the notifications off. Furthermore, it is possible to disable restart after automatic updates, but it sort of requires slightly messing up with Group Policies, definitely not a task for the average user.
Me likes updates
Do not get me wrong! I think updating the software on a regular basis is a good thing. But it should never come on the expanse of personal data safety. Once burned, never cooked, or so they say ... I think. Do you think a person who has once suffered from a botched automatic update will ever bother to update that software again - or even use it at all?
Updates are important - but they must be delivered in a safe, non-intrusive and user-dependent manner. It's the user who controls the machine and its contents, after all.
Conclusion
Automatic updates can be a serious problem. You'll probably never experience the dark side, but when it happens, it will hurt - a lot. This is particularly true for system-wide updates and security applications, especially scanners of all sorts that have the ability to delete files from the system without user interaction.
Make sure you control your machine - not the other way around. Perform frequent backups of your data and be very careful when leaving your machine unattended, especially if it has some sort of self-updating software installed on it. The best solution is to keep productivity machine pristine and devoid of any aggressive software that might eat your critical files. It takes just a single error. That would be it.
Enjoy.