Updated: December 15, 2008
This is the second article in a series of articles related to Internet security practices. The topic for today is: email security.
This tutorial will teach you the simple yet highly effective steps that you need to take to attain and maintain a high level of security when dealing with email. The article is mainly intended for Windows users, but there are some interesting tips for just about anyone.
Before or after reading this article, I also suggest that you read the first article, Safe Web practices - How to remain safe on the Internet. This other guide offers lots of useful information regarding browsing security and downloaded content management. Let us begin.
Table of contents
- Email as a blessing and a threat
- Preferred email application
- Basic security settings
- Discerning "good" email from "bad" email
- Links in email messages
- Attachments
- How to handle trusted mail, Part Deux
- Use Thunderbird instead of Outlook (Express)
- Good mail security practices
- Conclusion
Email as a blessing and a threat
Email is one of the most useful facets of the online world. It has revolutionized the speed and efficiency of communication between people. Email often touches our most intimate side, for we use it for business, to exchange words with friends and lovers, and even for other things we do not want out friends and lovers to know about.
It is not surprising that email present a highly profitable market for anyone trying to exploit it and take advantage of its myriad users.
To make things worse, the concept upon which email was built in the 70s, that of trusted computing between colleagues that know and trust each, allows for email to be sent by anyone to anyone, virtually without any restraint. It is for this benevolent reason that spam is so rampant and takes approx. 90% of bandwidth resources of all emails sent anywhere in the world.
Worse yet, the lack of any integrity check on the email sender, subject and content makes the email a highly potent weapon in the hands people with malicious intent. Some measures have been implemented lately, in an attempt to rein in the abuse of the email, like spam filters, attachment scanning with anti-virus tools and other methods, but they are only partially efficient.
Our goal is to be able to enjoy the email freely - and still remain safe from potential dangers that might lurk in the email messages. This article will teach how you can achieve a high level of confidence and fun, with just a few simple steps.
Preferred email application
Webmail
When asked what mail client I prefer, my answer is - none. I believe that email, just like the web surfing (HTML) belongs to a browser. In other words, I recommend webmail.
Webmail is an interface to using email by connecting directly to the mail server. Mail clients take the mail experience another step away by acting as intermediates between the user and the mail servers.
You do not need them. Mail clients were useful in the days when webmails offered very limited storage, in the range of several MBs - whereas you could store as much as you wanted on your computers. Today, with unlimited storage offered by all major mails, like Gmail, Yahoo or MSN, there is no need to spend hours downloading tons and tons of files to your machine.
The practical issue of cramming your drives with thousands of unnecessary files aside, the use of webmail also offers you integrated control of all web content through a single application, the browser.
Webmail is also accessible from anywhere in the world. Mail clients are restricted to your desktop. If your hard drive crashes, you might lose all downloaded email; on the other hand, they will stay safe on the server.
Take a look at the Gmail interface, for example:

It is clean and practical. Additionally, the webmail integrates with other Google applications. You also gain a solid level of security, by default. Just for fun, read what Gmail offers, then consider whether you really need a mail client.
If you do not like Google privacy policy or terms of use, then you can try their rivals, Yahoo or MSN - or tens of other free mail providers, all which offer highly useful packages, for free.
I must use a mail client!
All right, no problem. This is what this article is all about.
If you MUST use an email client, then you should carefully think through which application to use. Unfortunately, most (Windows) users will go with the default choice, either Outlook Express or Microsoft Office Outlook. This is not the best choice.
Why not Outlook (Express)?
Well, it's the same thing like with Internet Explorer; please see Safe Web practices - How to remain safe on the Internet. Outlook Express is a part of the Windows and thus more vulnerable to exploits than isolated, stand-alone mail clients. Many bugs plaguing the operating system itself will also impact Outlook Express.
But the goal of this article is not to convince you to use or not to use Outlook Express. The goal of the article is to educate you on security practices that are valid for just about any mail client.
And to demonstrate, I will purposefully focus on Outlook Express, with the knowledge that it is so frequently used by Windows users. I will show you how to secure Outlook Express - and then, trade it for superior alternatives.
Use Thunderbird
Windows users have a large pool of mail clients to select. The easiest and most sensible choice would be Mozilla Thunderbird, the Firefox's little brother.
Like Firefox, it is an excellent, continuously updated product, with many available add-ons, good default security, and a quick patch cycle. Thunderbird also has a very good built-in spam filter. And it is not enmeshed into the operating system, making it much more secure than Outlook Express. Thunderbird is also a much more customizable and efficient mail client. We'll talk some more about Thunderbird later on.

Now, we will review the basic security settings and practices that should ensure your mail experience is a more pleasant one.
Basic security settings
We will demonstrate using Outlook Express. By default, the security settings in Outlook Express are generous. HTML (and scripts) are allowed, external images are allowed. All these pose relatively high security risks when misused.

By default, Outlook Express will also preview any highlighted message. This means that the message body will be parsed, and if it includes scripts, they will be parsed too. Parsed means executed. If the message body contains malicious code that aims at exploiting a hole in the mail client, you might accidentally infect your machine.
This is definitely not what you expect from your mail client. Furthermore, you may not wish to see every message, so why enable the preview?
Furthermore, whether the preview is enabled or not, any time you open a message, the body will be parsed and rich content contained therein executed, including scripts and embedded images. Again, if this rich content contains malicious code, it is possible that you might get infected.
The best security practice is therefore:
- Disable the preview pane
- Disable HTML content in emails (external images, scripts etc)
This will impair your email experience, for sure. However, you need to ask yourself, can you afford to get infected? Is the potential security breach worth the risk?
If the answer is no, then you will sacrifice some comfort and beauty for plain functionality. Indeed, if we consider the core fact the purpose of mail messages is to send a communique to the other side, then it can be done with as little bells and whistles as possible. This also conserves your bandwidth and the server load.
Let's see how we can do this.
Disable HTML and images
Click on Tools > Options.
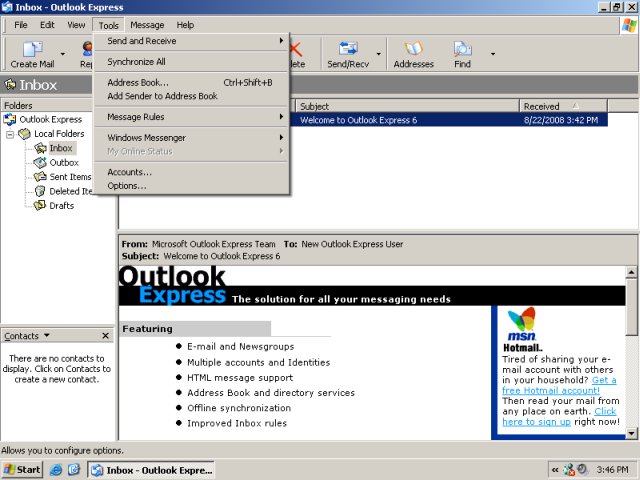
Let's review the Security tab first.

The few items you should pay attention to:
You should select the Restricted sites zone to use. While this does not gurantee much security, it is better than the Internet zone.
Check the boxes: Do not allow attachments ... and Block images and ... We will discuss the first setting later. The second one is what we require for the task at hand.
Next, let's review the Read tab.

We need to check Read all messages in plain text. This means that all and any email we receive will be automatically converted to text. This means that any malicious code of any kind embedded in the email messages is now completely harmless.
Lastly, let us review the Send tab.

Choose the Mail Sending Format to Plain Text. We do not wish to inflict upon others what we do not want ourselves. And after the change, the email message that we previewed before in its rich form becomes this:

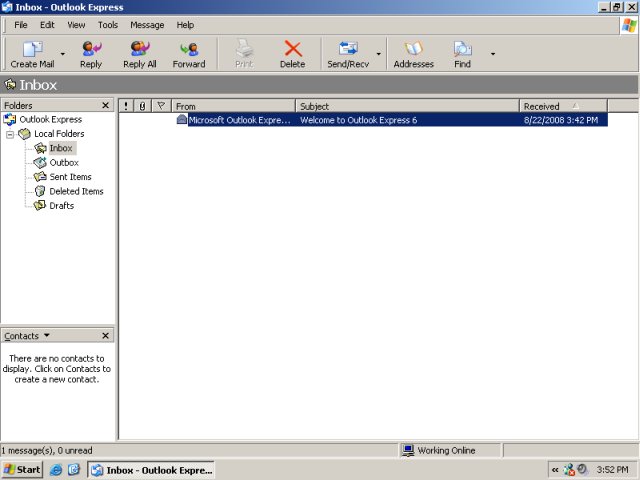
Disable the Preview pane
We want to disable the Preview pane altogether and only read emails that we explicitly open. Click View > Layout.

Uncheck the Show preview pane option.

This is our final, secure Inbox:
Test setup
Let's test the setup. I'll send myself an email, containing HTML (image).
This is what the email message looks like, originally when created:

And this is what we get in our Inbox:


Excellent! We blocked the images (and all and any other HTML code, including scripts). But there's still one culprit we did not take care of - the link that was in the message. We will talk about links shortly.
Now that we have setup our mail client to be safe, comes the most difficult part of email usage: how to tell good email from bad?
Discerning "good" email from "bad" email
How can we tell if the contents of an email sent to us are genuine? How can we know if the links in the email lead to the right sites? How can we tell if the mail attachments are not infected with viruses?
We will discuss links and infections later. Because if we can tell good email from bad, we will automatically solve the other two questions. We will not open suspect email. Period. And we will be very careful when opening email we trust.
Yes! Please note the last sentence! The most dangerous email is from people you trust. Because when you're alert to possible danger, you are less prone to slack your defenses and make a mistakes. It is when we are imbued with a false sense of trust that accidents happen.
This is because we can never be sure that the person on the other side has not made a mistake. Humans are imperfect (except me) and so are their actions. A friend could accidentally send you an infected file or a link to a site that has been compromised.
How to identify bad email
If you did not ask for it, you probably do not need it. This is the golden rule. Remember, 90% of all mail is junk. On average, every 9 out of 10 emails anyone recieves is not worth reading.
So, what kind of emails you should never even consider opening and reading? Well, being able to tell good emails from bad, bogus, fake, spam, or just about any other undesired emails is not that difficult. We have already reviewed the basic rules in the above article, under Links.
Find below an excerpt from the other article. Not all bullets apply to email, but the advice is sound and applicable in most situations.
If you are a savvy Internet user, you will probably be able to dismiss the tricks without thinking. Still, quite a few people take alerts, prompts and shiny red warnings too seriously. Here are several guidelines that should help you better understand when not to click:
One - There is no such thing as a free meal. Well, there is, but not on the Web. No one will give you money if you just install this or that. No Nigerian general's daughter will give you her millions. You did not win a lottery. Simply disregard any "incredible" offer, no matter how well designed it may be. Do not click on links that promise to take you to wonderland.
Two - You may also be enticed to check your system for errors, viruses or whatever. Again, your browser does not have the ability to perform any such activity and cannot inform you of any system errors. Therefore, any such link inside web pages is an attempt to draw your attention and possibly "force" you to click on a link.
Three - Links embedded in mails or Instant Messaging (IM) sessions should be treated with care. Do not follow links if you received them from people you do not know. Even if you receive links from people you do not and supposedly trust, you should still avoid clicking on links. If you must see what's behind the sent link, COPY it into the browser address bar.
Four - Think before clicking. If you receive an email - or any other form of message - telling you should login in to a certain website and approve, check, validate, or confirm your personal data, you should NEVER do this.
This is why:
- Ask yourself if the message is relevant. An email with the Subject: Your website is completely irrelevant for someone who has never had a website. So why click on such a link?
- Almost every single scam message is generic: the subject, the addressee and every other supposedly identifying information will always be in the form of you, your site, your country etc - never personally addressed to you specifically (e.g. Roger Bodger).
- Never trust the sender's name or email; they can be easily forged.
- Websites like Paypal (and probably every bank in the world) will NEVER ever send you emails asking you to confirm your credentials. They have them, they do not need a confirmation.
To sum it up, here are the emails you do not need:
- No one will offer you anything for free.
- Emails with the title Re: Your website and similar are 99.999857% pure spam. Most people do not have websites, so why bother reading such an email in the first place?
- Emails with curious sender names (like Fredon Malevolent) or meaningless titles (like she m3t Z00n here) are 110% pure spam; this should be kind of obvious, though.
- Genuine emails will be addressed to you personally (not a generic term YOU).
- Respectable institutions will never ask you to confirm your credentials in an email. EVER.
- Microsoft, FBI or any other "big" name will never send you emails.
Do not be tempted to read these emails. Even if we have covered the security aspects by disabling rich content in emails, it is a tremendous waste of time. Of course, opening any sort of attachment or clicking on links contained in these emails is a no-no.
What to do with good email
Here comes the tricky part. Good email falls into two rough categories: business mail and mail from friends, containing links and attachments. So before, we can fully elaborate what to do with good email, we need to review several other subjects, namely how to treat the supposedly "must-see" content in trusted messages.
After that, we will get back to this section again.
Links in email messages
Links are neither good nor bad. They are merely pointers to something else. All in all, they are quite useful. Instead of bombarding the email with tons of information that exists somewhere else - simply point the user to that somewhere else.
When you click on a link, your browser will open up. And here we land squarely into the browser security domain, which we have discussed in Safe Web practices - How to remain safe on the Internet.
You should be choosy about links. They may lead to web pages containing potentially harmful content, plain untasteful content or simply things you may not wish to see. The harmful content may include both programs containing malicious code or carefully crafted web pages aimed at tricking the user into divulging personal, confidential information that he/she would not otherwise volunteer.
If you MUST follow a link, then COPY it into the address bar of your browser. Try to exercise the highest possible level of browser security, as we have discussed in the other article, i.e. use Firefox, preferrably with Noscript extension installed and active.
But wait! I receive hundreds of emails from friends, it's impossible to do what you ask!
Well, it's all the matter of profit versus gain. Can you afford mistakes? If no, then you will be careful and choosy about what you receive in email. Most likely, you will begin filtering lots of email messages until you reach a comfortable equilibrium between security, productivity and fun.
I will give you a personal example. I used to receive about 500 "funny" "must-see" emails every day. Eventually, I realized that most of these 15-times-forwarded (Fw: fw: fw: fw: fw: re: re: looks familiar?) messages were in a way well-intended spam, sent countless times over - and not that funny.
My list of "trusted" recipients narrowed down to about 10 real friends, with whom I share interests and humor. These are the people whose emails I consider worth reading. These are also people whose judgement in discretion and security I trust, aware that they will have also taken similar considerations to mine before sending the email.
Please note that you do not have to be as anti-social and radical as myself. You can enjoy tons of email every day without any problems. It's matter of good security strategy and discipline.
Attachments
Every once in a while, someone will send you a file. And you must open it. So what do you do?
Well, several things, in fact.
First, if you are using an anti-virus application that is capable of scanning incoming email, you may consider putting it to good use. Still, there is no guarantee that your anti-virus will correctly flag every attachment it scans, or even be able to scan the attachment. For example, files inside passworded archives cannot be scanned by anti-virii.
This brings us to the point we have already discussed in the first article, under Downloads.
For the sake of clarity, please find the entire section pasted here - it is identical to the section linked just above:
Being able to tell a good file from a bad one just by looking at it is some sort of a hacker art. Most people cannot do it. Therefore, they must rely on tools written by other people to perform some sort of code analysis and then, based on the result displayed by this tool, decide whether to run the file.
First, here's the best advice ever - if you have any, even the slightest doubt that the file might be infected - do not run it. As simple as that. Consider the risks involved. Does the computer you're about to execute the file contains personal, valuable information that you do not wish to be corrupted, damaged, lost, or sent to a third party? What will you gain from the execution? What will you lose?
If you absolutely have to run a suspicious file, there are some things you can do to minimize the risks.
Scan the file with anti-virus
If you are running some sort of anti-virus (or any anti-malware) program on your machine, put it to a good use. Still, results from a single application might not be satisfactory - or reliable enough. However, running tens of anti-malware scanners on your machine is simply impractical.
For this purpose, two highly popular websites exist, whose entire purpose is to allow people to upload suspicious files and then scan them with a whole army of anti-virus and anti-malware scanners. Files are then forwarded to the vendors of these products for signature updates.


If you upload a file to both these websites and the results come clean, you are most likely OK. Still, it is entirely up to you to decide what you want to run on your machine.
At the very least, you should have backups of your important documents and preferably run a firewall with outbound control.
Search for answers on the Internet
The sentence "Google is your friend" has some truth to it. There will always be someone somewhere who has tried before whatever you are doing now. If you are not sure if the file you're about to run is malicious, open a browser, head to your favorite search engine and then type its name, in conjunction with malware, spyware or similar terms.

Then, spend some time reading, trying to find useful information on the relevant topic. You will most likely find the answers very quickly.
Virtualization
This is definitely an advanced topic, but if you want to test a file and are not really sure what its impact on the system might be, you may want to try it on a separate machine - or even a virtual machine. While not the silver bullet, this method can go a long way to ensuring the files you want to run on your machine behave as you expect them.
I will not elaborate here. Please read VMware Player - A great friend for more details.
So, to sum it up:
- Scan the file locally, if possible.
- Upload the file to an anti-virus scanning service site.
- Test the file in a virtualized environment.
And still, there is even more you can do.
You may not wish to upload a personal document to Jotti or VirusTotal. In this case, you will have to perform a little bit of home hacking to make sure the content is safe. Please note that some of the subjects discussed in this section might be unsuitable for novices.
Open the file with alternative application
If you get a Word file as an attachment, this does not mean you have to open it in Microsoft Word. Nor does PDF mean Adobe.
You should consider opening the file in a less-known, less-popular, less-mainstream program. It is quite likely that a file containing malicious code has been specially tailored to trigger a vulnerability in the most common application designed to open it. In other words, Microsoft Office files, if and when infected, will usually be infected with Office-specific malicious payload, for example, and this payload will not work in other programs.
While opening files in other programs does not guarantee safety, it can significantly reduce the risk. Just like opening HTML files in Firefox is preferrable to Internet Explorer, so it is with many of the popular, typical file types.
Here are some of the basic tips for the most common file attachment types:
| Type | Alternative application |
| .doc | OpenOffice writer * |
| .rtf | Wordpad |
| Foxit Reader | |
| .mp3 | VLC for Windows |
| .avi | VLC for Windows |
* this applies for all Office types (.xls, .ppt etc)
In general, whenever opening suspicious files, you should set the security of the application at hand to highest level. For example, if you must open an unknown .doc file, then you should set the Macro security in Word to the highest setting, so no macro runs when the file is opened.


You can also use Microsoft Online File Viewers and Converters for the purpose of opening unknown files. Most are free for download. Security wise, they are a good choice, because they will not execute any scripts embedded in documents.
Regarding PDF files for example, Foxit Reader has been known to be a very robust and bug-free program. If you still prefer to use Acrobat Reader, make sure it is fully patched and that you turn JavaScript off when you're opening suspicious files.
If you receive archives (.rar, .zip) as attachments, you should be extra careful when considering opening them. You should not be afraid to contact the sender and ask for clarifications regarding the contents and even suggest an alternative format. This is especially true for business mails.
Which brings us to the next important topic - being able to identify file types properly.
Identify file types
Executable files are what we need to avoid. Unfortunately, Windows has too many executable types to count. Worse yet, Windows uses the file extensions to categorize files. This means that a file with the extension .doc will be "marked" as an Office document, regardless of what the file may contain. But the little icon near the file name will definitely confuse the user.
Therefore, it is crucial that you use every possible tool to expose the true nature of the file, so you can use the right application to try to open it - or not. In general, any file that purports to be something else is usually not worth bothering with.
One of the Windows serious downsides is the fact it hides extensions from the user, by default. This is a terrible engineering mistake. Here's an example:
Extension hidden, we think we have a .doc file.

Extension shown, the file is in fact an executable!

Therefore, you should make sure Windows does not hide extensions from you.
In Windows Explorer, click Tools > Folder Options, View tab.
The options you should select:
- Check the Show hidden files and folders radio button.
- Uncheck Hide extensions for known file types.
- Consider unchecking Hide protected operating system files (Recommended).
The last option is meant for power users, because you may accidentally delete critical system files if they are visible in the Windows Explorer. However, when dealing with files sent by other people, especially archives containing several items, it is wise to be able to see everything. You may consider temporarily disabling and enabling this option as the need arises.

Long file names are another problem. If the file name is just too long to fit into the view of the Windows Explorer, you might not notice its real extension, even if you have the option Hide extensions for known file types unchecked (see above).
Here's an example:
We have a file called File with a very long name.txt. We have the extensions visible, so on the first glance everything looks ok. We think it's a text file. However, you may (or may not) notice the three dots (...) at the end of the Name column. This means the file name is long and does not fit into the select column width.

If we expand, we get:

Aha! So we have an executable file, with the name padded with lots of empty spaces! Most people would not notice this and fall for it. The truth is, the file is just an empty placeholder, with .txt and .exe extensions added.
This means that we CANNOT visually trust Windows to tell us what the file type is, whether it is masked as a different file type and whether it is executable and could potentially harm us if run. Solution? Use a dedicated utility capable of detecting file types.
The most sensible choice I can recommend is the Windows port of the GNU/Linux utility called file. This command can examine file types based on a number of smart criteria.
If you are interested to learn more about the file command, please refer to the Linux man page for file. The only downside is that the utility requires some use of the command line. Nevertheless, it works really great. Here's how it works on a file with its genuine extension set (.exe):

Here's how it works with a file pretending to be something else (.exe changed to .doc):

And here's a zoom-in:

That's it. We have all the tools. So let's re-examine the proper strategy for handling email.
How to handle trusted mail, Part Deux
We're back. Now, we have all the tools to properly ascertain whether the content is harmful.
Links
Here's how you should treat links in email messages sent by trusted friends and colleagues:
- If your setup is robust - Firefox + Noscript, you can quite safely afford to click on links, but don't get drunk on your own invincibility. Always exercise caution.
- If the sender is a truly trusted person - capable of making sure his/her end is secure and practices similar security habits to yours - then you can probably get away with clicking links.
- If the sender is someone somewhat frivolous and carefree in regard to computer security, then you might
want to think twice before following links sent by these people.
Attachments
Several things you should do:
- Download only attachments from people you trust.
- Perform an anti-virus scan on the downloaded content (one or many scanners).
- Examine its file type using file command.
- Open the file in isolated environment (a second, firewalled machine, virtual machine etc), preferably using an alternative application with security settings set to the highest level (no scripts allowed).
Business mails
This is the trickiest part, but here we go:
- Confirm with the sender what exactly they wanted you to receive; make sure the contents match. For example, if someone wanted you to review a new experiment proposal in PDF form, then you don't need any executables in the attachment, do you?
- If you receive attachments in a format you do not recognize, ask for a resend in a friendlier form. Business should not send their documents archived, unless a security consideration is involved, in which case you will probably know what to do (digital signatures, encryption etc).
- Treat the attachments as above.
Use Thunderbird instead of Outlook (Express)
OK, we're back to the mail client. If you really, really must use one, then use an alternative application. The same we did with the browser, the same we do with attachments.
Now, let us review the basic security settings for Thunderbird.

Again, we want to disable the HTML, scripts and external images in email messages and remove the Preview pane. In Thunderbird, it is called the Message Pane.
Remove Message Pane
Click on View > Layout. Uncheck the Message Pane (keyboard shortcut F8).

Disable HTML in emails
Click View > Message Body As > Plain Text.

Test setup
Here we go. Everything works as expected.

Updated: Thunderbird anti-spam capabilities
I think it's also worth mentioning some of the useful features that Thunderbird has.
For one, Thunderbird also features a quite powerful anti-spam filter, far superior to Outlook Express, which has none by default. This means you will have to handle less "suspicious" mails, reducing the chance of getting fooled by one.
Updated: Thunderbird extensions
Regardless, like Firefox, Thunderbird can be enhanced by extensions, allowing you to boost your mail client to a higher level of passive security. The choice of extension is entirely subjective, of course, but good candidates for security and privacy include Adblock Plus and ThunderBayes.
Additionally, you may also want to consider some "advanced" add-ons, like Enigmail, which provides OpenPGP encryption and authentication for your mail messages.
Good mail security practices
Well, finally, let us review some general tips regarding email. They may not directly impact your security, but they can help.
Use multiple email addresses
Separate your areas of interests, make sure the business mail goes to a business email address and private mail goes to a private inbox, and then some. You should never use a single email address for all purposes, especially if you visit sites of somewhat "colorful" nature.
I recommend you create separate accounts for your forums, for gaming sites, for adult sites, for business, for family affairs etc. This may somewhat increase the administration needs, but it's worth it. You will receive much less unsolicited email to your private addresses, reducing the chance of opening a "wrong" email or downloading the "wrong" attachment.
Updated: Use disposable one-time mail for registrations and "unsafe" communication
To keep your real inbox safe and clean of spam, you may also want to consider using disposable email address services, like KasMail. The service allows you to create temporary email accounts that can expire within hours or days, long enough to allows you to complete mandatory registration processes at various websites. While active, the accounts will forward the messages to your real account, but as soon as they close, the websites you used these accounts to register to will no longer be able to contact you.
KasMail is particularly useful for the sites you just know they're going to start spamming you. Combined with separation of email accounts by purpose, as explained above, allows you a very thorough level of filtering of mail messages before the user becomes a factor in the equation.
Consider sandboxing your mail client
If you are using a mail client, then you can isolate it further, just like we did with the browser. Please refer to Safe Web practices - How to remain safe on the Internet, under Isolating the browser further still. The same principles fully apply here.
Avoid opening email in unsafe locations
If you must use your computer in "unsafe" locations, like airports or Internet cafes, or if you must use a computer other than yours for accessing your mail, think twice before typing in your credentials. If the network is insecure or if the machine you are using is key-logged, your username and password could be stolen and then later misused. Additionally, any data you send or receive could be intercepted and read by other people.
The chances of this happening are not that high and you shouldn't spiral down into paranoia - still, be careful, consider the risks and benefits involved.
Conclusion
Email security seems a little more complicated that the browser security, but it is not, especially if you're using webmail. Make sure you trust the sender before you click on any links or execute any downloaded attachments. Google out suspicious items, scan downloaded files with anti-virus software and open them in non-default alternative applications.
All in all, you should be fine. The same guidelines that safeguard you in your day to day life when dealing with strangers, like "sudden" door salesmen or telemarketers, apply here. Do you simply give away your credit card to someone showing up at your threshold? Or the lady on the phone with the sexy voice telling you she's from this or that company offering you a tremendous deal?
That's about it. Stick to these few simple, yet highly effective practices, and you should be able to enjoy the world of the electronic mail with joy and safely.
Take care.