Updated: October 14, 2009
A few days ago, I've received a lengthy email from a reader, explaining why using Noscript extension in Firefox is not only not recommended, but also unnecessary and even hazardous to the Internet experience.
While I personally disagree with the binary definition of Noscript usage, as I do think it has a strategic importance in the long run, some tactical adjustments are needed in the short run to make it a useful addition to one's arsenal. In other words, using the tool blindly reduces its effectiveness - that of the whitelisting approach.
The email was a good reminder of that - and an opportunity to elaborate on the subject and provide the right formula for proper Noscript usage. While it may sound trivial to many a geek among us, it is not so for the average computer user. Let's go through the mail, sans personal details, and discuss the points raised.

How to use Noscript correctly
Here's the first point:
Javascript exploits are overhyped
That's an interesting point. To answer it, let's first take a look at what Noscript does. Noscript is a Firefox extension that blocks the functionality of scripts and plugins in Firefox, including Javascript, Java, Flash, and other plugins. This means that scripts included in HTML pages and designed to run on the client machine will not run.

This means that Firefox breaks functionality. It is one of its intended goals - stop certain parts of the browser from doing what they are meant to do. To what end, you ask?
The first and foremost claim for Noscript usage is security. By blocking dynamic content on untrusted sites, Noscript prevents the running of all known and unknown and potentially malicious exploits targeted at browser vulnerabilities. This significantly reduces the exposure vector, as only static, text content is displayed.
Noscript is designed to block everything and only allow scripts and other plugins on trusted sites. The default-deny approach is also known as whitelisting and is more effective than the signature-based, blacklisting approach. This is because Noscript allows only a small number of trusted sites, a finite group, whereas the blacklisting tools allow everything and have to keep up with an ever-growing, infinite group of threats.
One of the greatest browser threats are exploits in the Javascript engine. By default, Javascript is limited in it what can do. Among things it can't is the interaction with files on the host outside the browser directory. It's a sandbox, if you will. However, bend the rules and you get out of the box.
Theoretically, there could be an unpatched vulnerability in the browser Javascript engine that might allow escalation of privileges and execution of code outside the browser sandbox. Well, this happens all the time. Vulnerabilities are found and patched, not only in Firefox, but in all browsers.
However, since Firefox has a built-in autoupdater and a very fast patch cycle, the chance of a user stumbling across a malicious script capable of exploiting the yet unpatched hole in the browser is quite low.
This is probably the main point addressed in the claim that Javascript exploits are overhyped. In a way, I tend to agree. There are other reasons beyond security to using Noscript. I will elaborate on them later. Let's take a look at the other claim.
Broken functionality; for example, you go to a site that uses a form. Only you discover that too late. Let's say you have a dropdown box in a form, which requires Javascript. What are you going to do if this is a multipage form? On the first page, you will provide your data and maybe a credit card number for this or that subscription. On the second page, you choose a value from the dynamic dropdown box. What then? It won't work. So, what do you do now, enable scripting on that page and risk your credit card number being resubmitted twice. Then, there are sites where you won't even know things aren't working properly, because of Noscript.
Again, valid points all. Using Noscript when going to pages where you are expected to interact with the server and exchange information requires a careful approach.
Enable all scripts
When you go to a website where you expect to provide your information, make sure you enable all scripts. This means enabling them one by one until no more blocked scripts are left. This implies trust - but you are about to provide your information to the server, so yes, there's trust involved.
Remember to do this any time you are expected to fill out any sort of a form or buy online, including sites like Amazon, eBay, PayPal, forum registrations, etc.
You will have visual clues to help you determine whether you have enabled all scripts on the particular page. When scripts are blocked, you will see the standard Noscript "no parking" icon in the status bar. For as long as there is even one script blocked, the icon will remain in that form.

Once you have enabled all scripts, the icon will turn into a white circle with blue S in it, without any red lines. This means that all scripts have been enabled and you can now continue with the registration, online payment, etc.

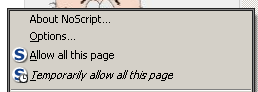
The simplest way to go through the process is to use the all sites feature. Either click on Allow all or Temporarily allow all. Repeat until all scripts are allowed.
Ordinary users running Noscripts and going to a website that does not function well will not know that they need to enable Javascript. They won't even know that something is missing or will think it's supposed to be that way. They won't have a clue there's a relation between Javascript and broken functionality. Whitelisting is for people who know what they're doing and they don't need Noscript.
True, this is true! The sad paradox of security. Those who need it can't use it and those who can don't need it. What more, ordinary users have no clue what they're doing most of the time. While I'd like to see Noscript used more widely, I admit it's a geek tool. Noscript is not very useful for clueless people. So what to do then?
Ordinary users should not run their browsers with plugins and scripts blocked. But this exposes them to some risk, you might say. Well, this is why most people should not be running their operating system with the default administrator account enabled and should instead be running a limiter user account. In Windows XP, there's SuRun. In Windows 7, there's UAC. In Linux, things are simpler to begin with, as the operating system comes configured with higher default security settings, including the reduced user privileges. This way, while there might be security issues, their scope will be limited.
Noscript blocks Flash, too. Many Flash sites, to say nothing of Web 2.0 sites, rely on Javascript (and Flash) for all sort of things. They won't work and the users might think there's a problem with their Flash plugin, not knowing it's because of blocked scripts.
Same as above. Ordinary users will have trouble troubleshooting site-related issues when running with scripts and plugins blocked or partially blocked. Unfortunately, there's no easy solution that leaves them with full functionality and Noscript.
What about Ajax? It's a great thing that allows servers to pull new information from the server without reloading the pages. Works only with Javascript enabled. Example: Gmail. Without using the full interface, the users won't ever know what they're missing.
No beef here. Noscript breaks functionality. It's one of its mission statements. Users running Noscript need to be aware of this. The whole idea of the extension is to stop scripts from executing. This has a price.
But what about the benefits?
When should you be using Noscript? Or why should you? I'm going to give you my own perspective. It is not security related, although security comes as a bonus. Here is the one simple reason why I use Noscript on most of my Firefox installations:
I like quiet
Quite a few websites are too noisy in my opinion, with too many elements dancing, drawing your attention and distracting you. Call me old-fashioned, but I just need the raw, naked content and little else. Most of the time, I merely wish to sit down and read what's there.
Noscript makes this task easy as it filters away some of the potential garbage, making sites load faster and with much less background noise than they usually do. Of course, there are sites where you require the functionality. This is exactly what the whitelisting means. Enable all and everything on sites you trust - but also on sites you want or need. Very simple. It does require discipline and is definitely not meant for everyone.

Extra reading
That's about it, I think. It answers the questions in this mail.
You may also might be interested in a number of related articles:
Firefox addons - Manage browser addons in a centralized manner - Tutorial
10 must have Firefox extensions
There is also a number of other Firefox-related articles, covering Flash installation, how to open .mht files in Firefox, the review of Firefox 3.5 and its memory usage, how to get Flash installed in Firefox on Linux, Ubiquity, Perspective, and more. You can find all of these in the Other sub-section on the Software & security page.
Conclusion
Hopefully, this articles answers some of questions and doubts you may have about Noscript and its use. I do admin there's quite a lot of material to chew on. Noscript is not trivial, even for experienced users.
Using Noscript correctly will ensure much more than security. It will keep you happy and productive, without losing or wasting your time and effort on a misconfigured browser. It will save you the trouble of refilling online forms or dreading that double credit card charge. With some luck, this article cleared out the fog. Now, you know what to do. Using a tool is only the beginning. Using it correctly is art. I hope you liked it. See you around.
Cheers.