Updated: April 20, 2016
If you happen to follow the security scene, you must have noticed a lot of buzz around various security issues discovered this month. Namely, a critical vulnerability in the Microsoft Graphics Component, as outlined in the MS16-039 bulletin, stories and rumors around something called Badlock bug, and risks associated using Firefox add-ons. All well and good, except it's nothing more than clickbait hype nonsense.
Reading the articles fueled my anger to such heights that I had to wait a day or two before writing this piece. Otherwise, it would have just been venom and expletives. But it is important to express myself and protect the Internet users from the torrent of pointless, amateurish, sensationalist wanna-be hackerish security diarrhea that has been produced this month. Follow me.

All your Ragnarok are belong to us.
Noscript and other add-ons open millions to new attack
I will not link to the article in question in order not to drive traffic to something that can only be described as digital goatfest. In essence, the article tells us that, because all Firefox add-ons share the same namespace, i.e. no memory isolation, a potentially malicious add-on could snoop on other add-ons. That's the story. Noscript, a supremely useful and important add-on providing tremendous silver-bullet security to Firefox users, has been singled out in this article, in order to give it an ironic spin.
Complete nonsense.
The thing is, apart from driving traffic of course, and nothing breeds and generates page views like good ole fear, the article does not provide one shred of useful, actionable information to the readers. Because the highlighted problem could only become a problem if a user installs a malicious add-on themselves. Yes, that's right. You could be infected if you infect yourself. Holy crap, Sherlock. Now, how could this happen:
You install an unsigned add-on yourself. Please electrocute yourself.
You install an add-on from the Mozilla repository, after it has been screened, tested and digitally signed. In other words, if the add-ons servers were to be hacked, the users would have much bigger problems than an extension that targets other extensions.
Then, there's the validity of such an attack. If you can gain privileged access to the system, eavesdropping on other extensions is the least useful thing you could do. It's like wire-tapping someone's phone and then hiding under the bed, listening on the calls. Or some such analogy. Who cares.
In other words, this would-be security issue is not an issue at all. It requires active, deliberate interaction from a user keen on damaging their system. For that matter, you can just infect your machine with any which malware. You know what else has a single namespace? Your kernel.
Microsoft bulletin MS16-039
This is an interesting one. The top 20 results for this particular item all have one thing in common - a word-for-word copy paste of the actual advisory, without providing a single original thought or valuable comment. If that's journalism, I'm Shakespeare.
Out of these twenty websites, only a single source mentioned EMET, the supremely useful and important mitigation framework developed by Microsoft, which provides excellent protection against exploits. But hey, that's not dramatic enough! And only one other would-be or be security blog had actually gone to some length in trying to outline the issues and how they may come to bear.
Apparently, there are four separate vulnerabilities, of which three are local. Boring unless you're a corporation with lots of people working in the organization. One could be a remote execution issue if a user opens a specially crafted document - electrocute yourself please - or visits a page with embedded malicious fonts.
This security update resolves vulnerabilities in Microsoft Windows, Microsoft .NET Framework, Microsoft Office, Skype for Business, and Microsoft Lync. The most severe of the vulnerabilities could allow remote code execution if a user opens a specially crafted document or visits a webpage that contains specially crafted embedded fonts.
Now, at this point, I would ask, all right, so you have written down the problem. OK, what's next? How does the exploit actually work? How do users actually protect themselves from this thing?
Nothing. Silence. Because people complaining and writing all this drama do not actually want to help. They just want to grab attention and reap profit from fear and propaganda. And they most likely do not have the necessary technical expertise to actually help. Which makes them useless.
Proper analysis
So let's see what gives. First, you can actually install the security updates provided by Microsoft. No biggie. This means that no particular advisory warrants any special mention really. But if you want to go technical, Microsoft has a lot of useful information on this topic, unlike the blogs writing about this.
Three of the four vulnerabilities fall under the category of: Multiple Win32k Elevation of Privilege Vulnerabilities, identified by advisories CVE-2016-143, -165 and -167. They are all local, and two of these have active exploits. Not interesting for the vast majority of home users.
The fourth one - Graphics Memory Corruption Vulnerability CVE-2016-0145, is all about embedded fonts. Currently it has not been publicly disclosed or exploited. That, however, should not really console or worry you. Because it's all about education. We do not want to worry about something being patched today. We want to be able to address all potential, future vulnerabilities of similar nature, whether they have their moment of spotlight or not.
Which means, we need to focus on embedded fonts. This is the source of the problem. If malicious embedded fonts exist on a webpage, and the user visits that page, then the system font libraries may go crazy and allow for an arbitrary execution of code.
In other words, we want to stop embedded fonts and/or stop the browser from calling on the font libraries in an illegal manner. Either one or both of these vectors, if stopped, can prevent exploits.
The first can be addressed by not allowing embedded fonts. In general, embedded fonts are displayed using the @font-face CSS rule. In other words, if you prevent this particular CSS rule from being parsed when a page loads, embedded fonts will not be loaded, and potential exploits will not run.
Now remember Noscript and how it was vilified just earlier?
Noscript actually blocks @font-face on untrusted pages!
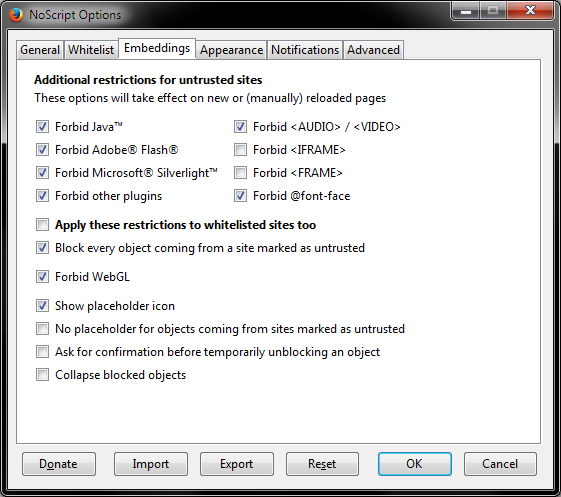
So in fact not only Noscript does not put millions at risk, it actually helps millions not be exposed to potential issues with embedded fonts. It just shows how much hype and drama there is without any real justification. But we've only just started.
The second vector is a browser going crazy by calling on a font library in an illegal manner. This is exactly what the Enhanced Mitigation Experience Toolkit is for. 'Tis a very nifty security tool. Zero footprint, no nonsense. It does not differentiate between good and bad applications. It stops all illegal instructions it can detect in programs that run under its wings.

And then, a practical, useful question would be - has anyone tested embedded font exploits under EMET using any one of the browsers? Or perhaps office tools or Skype or alike? Has anyone tried any sort of embedded fonts tricks that would trigger an illegal instruction?
Speaking of mitigations, Microsoft has a WHOLE page on blocking untrusted fonts! It explains how to add mitigation options, which prevent GDI from loading any font outside the %windir%/Fonts directory. This is exactly what you want in this case. And that means that exploits of this nature will not trigger any issues. Ergo, all those sensationalist articles are just pure bollocks.
The article applies to Windows 10, and it also mentions EMET 5.5, which nicely complements this capability. I do not know if Windows 7 and Windows 8.1 users will also benefit from the exact same level of security, but then, they surely won't be any worse than they are.
Block untrusted fonts
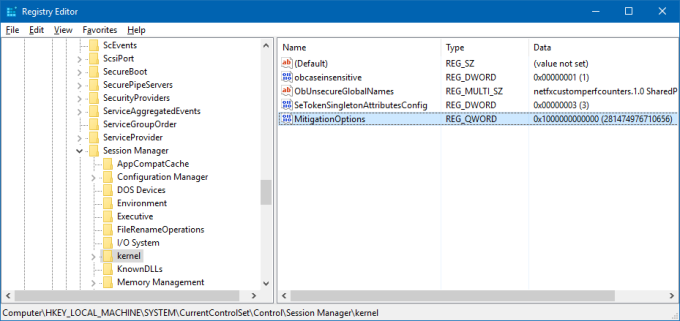
Anyhow, here's how you can block untrusted fonts. Launch regedit.exe, and then go to:
HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Kernel\
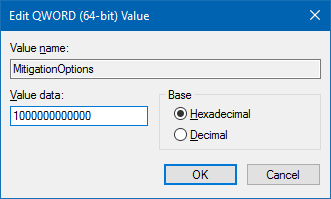
Under this hive, look for the MitigationOptions key. If it does not exist, create a QWORD (64-bit) value and rename it accordingly. The article assumes 64-bit architecture, so I believe you want a DWORD (32-bit) value on 32-bit systems. Assign the right value. To block untrusted fonts, you want a lengthy number - 1000000000000. Add this to any other mitigation value you may already have in place. This number is actually a filter.
And that's children, how babies are made!
Other stuff
There's more usual scaremongering. Flash. Meh, boring. Other pointless stuff, again, without any sensible leads on how you may actually protect yourself. It's like saying, a truck may hit you this month. Yes, but if you don't stand in the middle of the road, you can significantly reduce the chances of that happening. Only no one bothers, knows or wants to mention the workarounds. A total of just 1 out of 20 top searches did provide actual help to users, and even then, there wasn't too much info on EMET and how it works.
Why all this hype, pray?
Dedoimedo, why are these other folks not helping? Why are they hyping security so much? All good questions. There are several answers to this. The first and the obvious one is, no one got rich by selling unicorns and rainbows. People love drama. Secondly, for the lack of a better and more substantial content, rehashing security bulletins is as good as baking bread made of pure gold. But most importantly ...
Military service
Most if not all of the security bloggers in the Western world, re: California, have not had the pleasure of undergoing a military service of any kind. I highly recommend it. Adds hair to your chest and mustard to your radish. Builds character, forces you to socialize, you learn discipline, but also gives you a different perspective on life than you normally get listening to Spotify while you Segway your way to the nearest bio-meta-milk coffee shop.
And so, if your life has not been exposed to the less fluffy sides of human existence, like poverty, famine, disease, slavery, trafficking, riots and revolutions, war, and other delights of this world, going QWERTY - or DVORAK - on a security issue detected in an operating system suddenly becomes the creme de la creme of excitement.

A blogger on its way to the next security advisory.
To wit, if you are all too deep into the Hollywood blockbuster mentality, where explosions are orange and hacking occurs on sickly-green-and-black terminal windows, then you may easily lose the grip on reality and suddenly think that a simple font vulnerability is no less important than SARS and Ebola combined, and that by blogging about it, you're almost as badass as a regiment of the French Legion freshly landed on the shores of Djibouti.
Conclusion
This is the month of April in a nutshell. Nothing new. Nothing exciting. Nothing valuable. On the contrary, lots of detrimental nonsense designed to elicit drama and shock, keep you pasted to the screens and reading, frightening you without teaching you how to protect yourself. Noscript, EMET, hey, what about data backups? Nothing.
You all already know how I feel about software security. It's totally overrated. And people blogging about it without actually educating users are no better than the supposed enemy they are preaching about. If you have nothing valuable to contribute, you'd better not write anything in the first place. Anyone can read Microsoft bulletins. They do not need you to repeat the exact same information. Nor to spread FUD and propaganda without knowing how basic things work, like Firefox extensions. But hey, that's the world we live in. The really important thing is, the sites are all mobile-friendly, so they have good rankings. Right? Valuable information, after all.
Note: All dem old pics are in public domain.
Cheers.