Updated: August 27, 2009
In a nutshell, encryption means taking data in a readable, plain-text form and converting it to a random-looking, cypher form that cannot be understood without the encryption key. This means that encryption is an efficient method of making sure your private, sensitive data cannot be easily read by unauthorized third parties.
Today, I would like to begin a series of articles that will teach you several methods of encrypting data so that it stays safe even if an unauthorized third party gets hold of it, for instance, thieves. We will focus on how to do this both on Linux and Windows. Now let us begin.
Introduction
In both Windows and Linux, users have many ways to encrypt their data and keep it private. Linux distributions and their respective repositories offer a range of encryption tools that can be used to safeguard the privacy and integrity of one's data. Windows users will have to manually download applications from the Web. Luckily, some of the most useful encryption utilities are both open-source and cross-platform, therefore the reliable programs that you use on Linux will also serve you well on Windows.
In this article, we will review the different encryption methods and tools and learn when and how to use them. Different situations call for different measures, therefore it is important to understand your needs and select the right tools for the job.
Therefore, our first task is to understand when we should use encryption, what kind of encryption methods and algorithms exist and lastly, what tools to choose.
When should you use encryption?
Because of its high potential in getting used for wrong purposes and the portrayal of encryption in Hollywood as the tools of the trade of notorious hackers, you are quite likely to evoke a few raised brows or a scornful look when you mention encryption.
What do you have to hide? is the most likely response you will get when you broach the subject. The truth is, while encryption can be used to hide things, it can also be used to simply safeguard things. Take your family photos as an example. You do not have a problem showing them to your close friends. But you would not want these files perused by a thief who has just gotten hold of your laptop, even if the actual harm that may come from this breach of privacy is rather small. It's the matter of perception. People do not like their privacy boundaries intruded, no matter how real or serious.
Therefore, if you ask me, encryption should be used to secure data stored on high-profile devices, like smart phones or notebooks, which are easily lost or stolen. And because there's a chance these devices might get stolen, you should probably make sure that you have more than one copy of your data, stored elsewhere. What more, in unencrypted form. This is because retrieving data from encrypted devices is usually far more difficult than those without.
So, let's recap it:
- Use encryption to secure data on high-profile, mobile devices.
- Make sure you have a second copy (unencrypted) stored in another location.
Remember, the same tool that protects can also be your bane! If you forget your password, you will have a very difficult time getting your encrypted data deciphered, if ever. And if your one and only copy of encrypted data gets stolen, it will probably be forever safe from the thief's prying eyes, but you will still have lost your data. The same applies to spilling coffee on a laptop and frying the disk. We will talk about backup later on. Now, let's see what types of encryption exist.
Encryption methods and algorithms
Naturally, any talk about encryption instantly provokes lots of nonsense about government agencies using backdoors to hack into people computers, conspiracy theories about special computers breaking encryption codes in seconds and so forth.
The simple truth is that same encryption methods and algorithms that you may want to use are used by government services worldwide. In fact, contrary to intuition, when it comes to encryption you want to use as publicly known and tested algorithms as possible. This means they have been combat-tested and proven worthy. Little known, private algorithms are usually gimmicks and broken in the matter of seconds. Security through obscurity does not apply here.
When using encryption, you will go for open-source solutions that have been around for a few years and withstood the gales of hacking. There are no magic tricks here. Good encryption is like a celebrity that the paparazzi have nothing on. We will touch this subject more later on.
Encryption types
There are several ways to safeguard the data.
Individual file encryption
The most common approach is to separately encrypt individual files. This method has several advantages. First, it is the simplest method, as in most cases, it merely requires that you right-click the target file and encrypt it, with your password as the decryption key. Second, should some of your files get corrupt or your storage devices damaged, the chance of a massive loss is reduced. You may lose some files, but others will be retrievable.
The downside is that this method is not scalable. If you have a large number of files, the complexity of your setup goes up, since you can theoretically use a different encryption algorithm and a different password for each and every file. This means you're more likely to forget the different passwords used, creating a difficult situation where you are unable to access your data. You can use a single password for all files, but then you have a single point of failure. Furthermore, managing dozens, hundreds or even thousands of encrypted files across many directories, partitions, disks, or even computers is quite a task. You're also more likely to accidentally delete or overwrite a file now and then.
Volume encryption
Volume encryption is a method that allows you to create encrypted containers inside which you will be able to store your data. The containers themselves can be files, partitions or even whole disks. Their size will vary depending on your needs and physical limitations of your storage devices.
The encryption contains are quite useful and easy to manage, because you treat them as separate entities. For all practical purposes, these containers are virtual hard disk volumes. Think of your virtual containers are additional, on-demand disks that you connect when you need to work with the data stored on them, except you require a key to be able to see the data. The containers can be of any size and kept anywhere, which makes them useful for large-scale operations.
The downside of this approach is that the initial setup is more complex and requires some knowledge of the system internals and disk behavior. Moreover, opening and closing the encryption containers takes more than a right-click. Finally, if the container gets lost or damaged, there is a chance you may lose all data stored inside it.
Basically, you have two choices - file encryption and volume encryption. Both have their uses and in fact, you should use them both. In theory, you can even combine them, by placing individually encrypted files inside an encryption volume, although this is most likely a total overkill.
In this article, we will talk about file encryption. In the sequel, we will discuss volume encryption. Now, let's see what tools we want to use to encrypt individual files.
PGP
PGP stands for Pretty Good Privacy. It is a program that allows you to both encrypt your files and digitally sign your communications (like emails). Thus, PGP offers both privacy and integrity. You can safely encrypt content and send it to other people and also make sure that the content has not been tampered with.
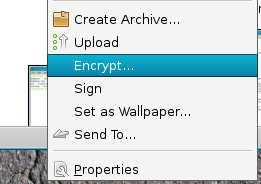
Most modern Linux distributions come with PGP installed. Linux Mint is no exception. Right-click on any file and select Encrypt and the fun begins. On Windows, PGP can be installed just like any other application.
Naming confusion!
Please note that there are several versions/implementations of PGP available, including payware solutions, so this can get confusing. What you want to look at is Gnu Privacy Guard (GPG), an implementation of the OpenPGP standard.
Furthermore, Windows tools include command line (CLI) editions and various GUI wrappers that make the usage simpler. Plus, there's a number of Firefox extensions that can also be used.
As you can see, it can get confusing. In Linux, just use the built-in tools or download via the repositories. In Windows, start with the GPG link above and see if you're comfortable with the solution. You may also want to read the Wikipedia article on the subject.
Linux
Like I mentioned before, PGP comes with most Linux distros already installed. After you select the file you want to encrypt, right-click and choose Encrypt, PGP will launch.
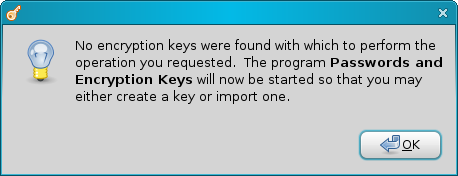
The first thing it will do is complain about no encryption keys found and start a wizard to create some.
Follow the wizard through. Click on New (under First time options) to create a new set.
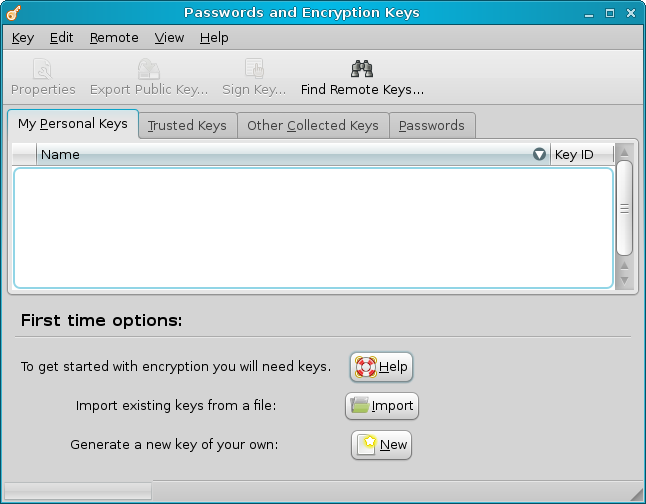
Now, the wizard also lets you create Secure Shell (SSH) keys, but this is a task for another, separate tutorial. We want the PGP key.

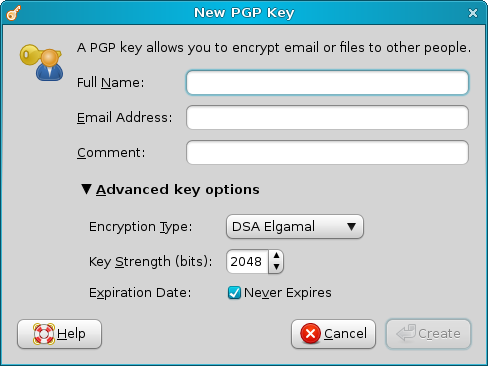
Since PGP can also be used to encrypt and sign emails, providing your name, email and comment forms a part of your digital signature. You can insert the credentials or simply skip the step. We will skip it for now.
Pay attention to the Advanced key options, though. Encryption Type and Key Strength are important. In general, you won't get any lousy options. The real question is how paranoid do you want to be. In that case, you may also want to set an expiration date, which will force you to periodically change your key. Most people can get by well with the default settings.
Once this is done, click Create. Your key will be created. Now, right-click on a file:
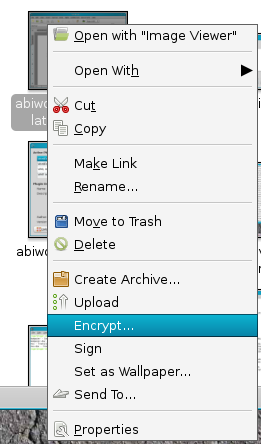
You'll be asked which key to use. And that's it!
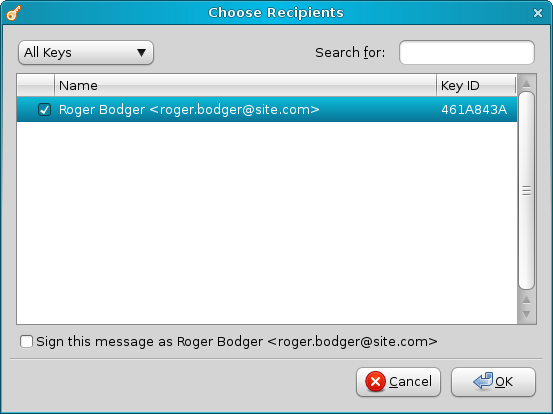
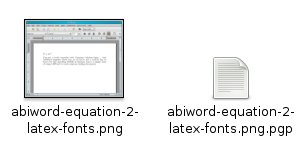
Your file will be now encrypted. Please note that PGP does not encrypt the original. Instead, it works on a copy. This is convenient, should you make a mistake or forget your password. It also aligns well with my opinion that you should also have unencrypted backups - or originals - of your data.
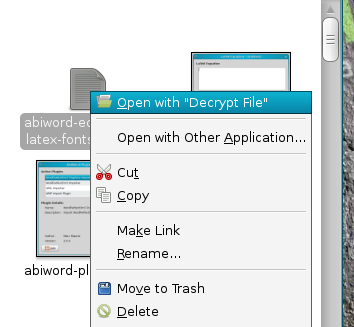
Decrypting files
And to decrypt, simply right-click, choose decrypt and provide the right password. The same goes for all tools and methods described below.
Windows
On Windows, things are very similar, however a little more complicated to setup. The procedure is virtually identical, so I'm going to show only a few screenshots.
By the way, we will not discuss email encryption here; that's a separate tutorial. Following up on the Safe Web and Mail Security articles, we'll see how we can beef up Thunderbird to use digitally signed emails and encrypt the contents.
When installing GPG, you will go through a standard wizard, however after the installation, you're on your own. Using the command line is identical to Linux. This is not recommended to new or typical Windows users.

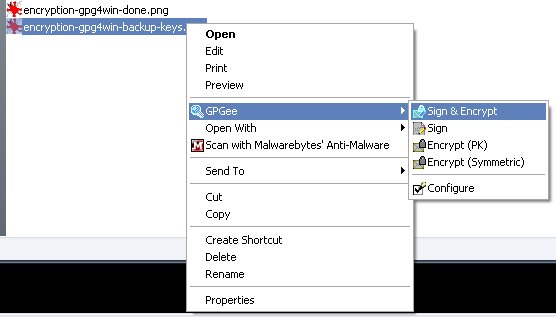
Instead, you may want to use a GUI implementation like Gpg4win. Gpg4win is a much friendlier tool, with lots of plugins, wizard-like functionality - and right-click integration.
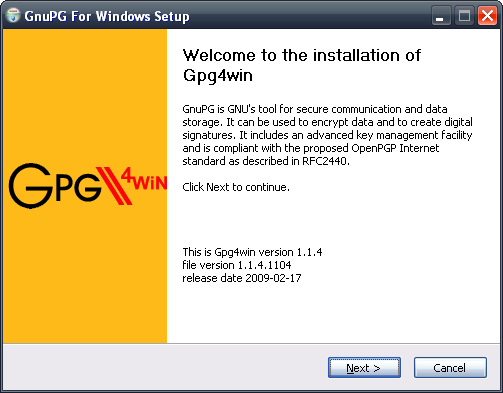
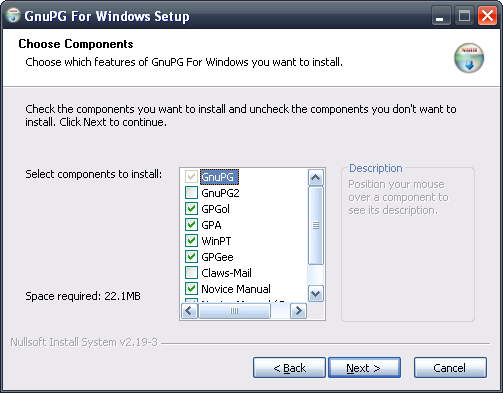
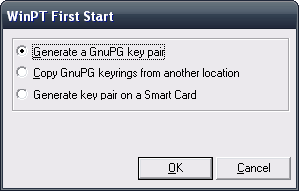
After the tool is installed, you'll be able to create new keys, just like on Linux.
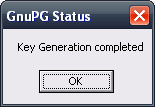
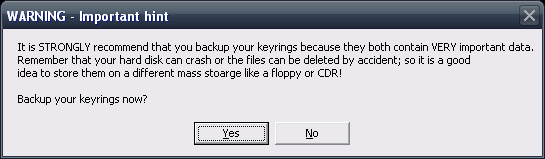
Once finished, you'll be asked to back the keys. We'll talk about this later on. BTW, notice the small spelling mistake in the warning message (storage).
For now, just right-click and enjoy.
Lastly, if you're using Firefox in Windows, you should also take a look at FireGPG extension.
When should you use PGP?
PGP is useful for encrypting individual files or electronic communication messages. Your PGP digital signature will ensure that whoever receives an email coming allegedly from someone will know that the sender is who they claim to be and that the message has not been altered in transition. Furthermore, it also allows you to make the messages contents unreadable, if visible, by third parties. But, we'll talk about emails separately.
Additionally, PGP makes a very good (and quite simple) choice for managing individual file encryption. Now, let's meet two more candidates.
ccrypt & AxCrypt
ccrypt and AxCrypt are file encryption utilities for Linux and Windows, respectively. Like PGP, you can use them to encrypt individual files. They are very simple to learn and use. Let's begin with ccrypt.
ccrypt
ccrypt is a simple, lightweight program that can be used instead PGP or alongside it. ccrypt replaces the standard UNIX crypt utility, which used weak algorithms.
It can be found in the repositories:
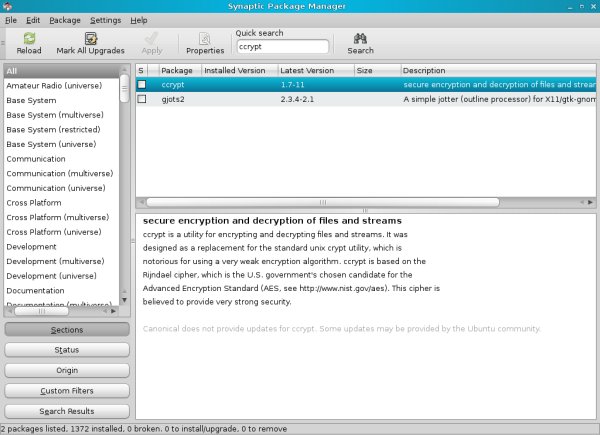
ccrypt is a command-line tool, so you should spend some time reading about the different flags and options. However, it's quite easy to use.
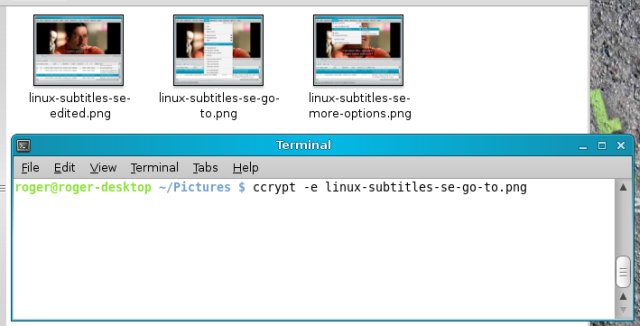
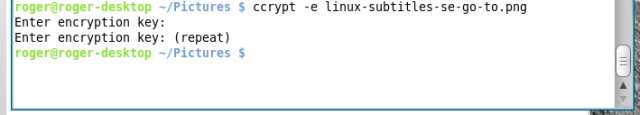
Encryption
Open a terminal and type ccrypt -e against a desired file:
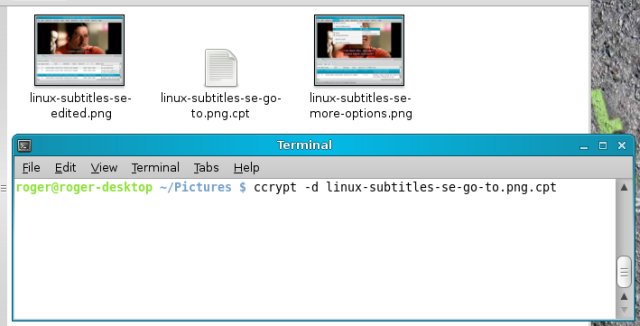
Decryption
And similarly, in reverse order, decryption (with ccrypt -d):
When should you use ccrypt?
ccrypt is very simple to use, therefore you should consider it for your everyday use, if and when needed. The command line functionality makes it useful for scripts and unattended batch encryptions.
AxCrypt
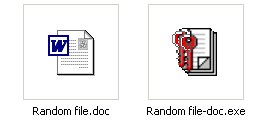
AxCrypt allows you to encrypt individual files, pure and simple. It can do this in two ways: create encrypted files that you can later open with AxCrypt or create self-extracting encrypted executables that can be opened on computers without AxCrypt installed.

If you choose to just encrypt the file, you'll be asked to provide a password. The original will not be retained, though. It will be converted to a file with the .axx extension that can only be decrypted by the AxCrypt program. To retain a copy, you'll have to go for the second option in the context menu.

On the other hand, you can create the self-extracting executables that will work on any Windows machine. Of course, executable files make for a rather spicy choice on Windows machine. However, this method will create a copy and keep the original untouched.
When should you use AxCrypt?
AxCrypt makes a solid alternative to PGP. You can also encrypt several files at once or even entire folders. Please note that corrupt files may break the encryption procedure, so you should work with small chunks of files at a time.
The executable option is quite useful, but may make other people nervous, if you have to send them files. A whole lot of problems may occur if you have anti-virus software scanning files or mail clients filtering files based on their attachments. This is something you should consider, portability versus comfort.
General advice
Compliance with law
Please be aware that laws in some countries prohibit the use of encryption, so you should consult with legal bodies to make sure your actions do not break any laws.
Backups
Backups are critical when it comes to encryption. When you encrypt the data, you transform it into a supposedly unbreakable format. The only way to decrypt the data is by using the key, which can be a password or a passphrase, preferably long and complex.
So, the first problem with encryption is the password. Without the right password, encrypted data will never be usable again, so make sure you do not forget the password.
The second issue arising is the possible damage to the encrypted data. Just like any other file, encrypted data can get lost, deleted or damaged, for whichever reason. Damaged files are difficult to open and read, even more so when they are encrypted. And while the corruption of plain-text files may result in parts of the data being unreadable, with encrypted files, you will probably lose all data.
The developers of encryption software are well aware of this and take all precautions to make sure you can salvage data from damaged or corrupted encrypted files, but there is no guarantee. Therefore, it is my warmest advice that you have a non-encrypted original also stored somewhere. If you're truly afraid of theft, keep the files on CD/DVDs, no one will steal those, unless you have been personally marked and targeted. Well, you can also store them in bank safe deposits, if you really must.
To sum up the backup strategy:
- Have unencrypted original data saved in addition to encrypted copies.
- Have more than a single copy of your data (including encrypted files).
- Do not forget your passwords.
I think that's it. We will discuss the backup strategies in greater detail in the second article, when we learn about encrypted volumes.
Oh yes, do note that the suggested backup strategy reflects my own person practices and may not be suitable for your needs. There is no written rule - only best known methods and personal preferences. I think the important data should be kept in both plain and cipher form, but you may disagree.
Conclusion
In this article, we learned a few important lessons on encryption. We now have the tools to encrypt our files and keep them safe in the case of a privacy breach. In the next article, we will learn how to encrypt entire partitions or even whole disks.
I'd like to thank Ocky for inspiring this article.
Cheers.