Updated: December 19, 2009
Many Windows users feel they need to install and run all sorts of security programs on their system, regardless whether they know how to use these programs, or even worse, respond to real-time alerts, popup messages and notifications presented by these programs. It's a time bomb. Let me explain ...
Windows security is the greatest paradox of all - those who need it can't use it properly and those who can do not need it. Thus, when an average user is given an arbitrary set of tools supposed to him/her safe forever from the perils of the Internet, it's only a matter of time before the user makes the one cardinal mistake and undoes the entire security of his system, so un-meticulously assembled and so blatantly misused.

Introduction
In this article, I hope to clear away some of the panic fog shrouding the world of Windows security. Furthermore, I hope to provide the Windows users with the most important security tool of all - reason.
Security is not about programs. It's about understanding. Even the supposedly best security software can do little against the tenacity and cluelessness of stubborn, obstinate, persistent, self-deluded users intent on achieving whatever they're trying to do. But even the most basic security setup can be quite useful in maintaining a very reasonable level of security and privacy if the users set their mind to it.
Today, we will have a war simulation - a day in life of your average computer user. The user will be assailed by all sorts of prompts by the system, asking the user to answer some rather difficult questions and make tough decisions with far-reaching consequences about the fate of his/her machine seemingly based on rather Cesarean, arbitrary thumbs-up thumb-down choices.
We will learn how to respond to these prompts. And we will turn a game of hunch roulette into calm, calculated, controlled computer usage, where the person behind the keyboard maintains full understanding and control of their machine.
We won't meddle with individual products. We will play with the core concepts. If you get the fundamentals, you'll know what to do, no matter what your firewall or anti-virus is called.
Let's do it.
Rule 1: Don't panic
Nothing happens without a reason. Computers are just dumb machines running code. When they get an instruction to do X, they do X, as simple as that. Computers don't think or do any sort of things you see in the movies. Remember, you're in control. If the boxen annoyeth thee, thou shalt unplug it.
Software update prompts
This can happen quite often. Your programs will have built-in update mechanisms, allowing them to check for updates periodically. This can be quite useful, as it lets you keep your programs patched, reducing the chance of functionality problems and possible security vulnerabilities.
Here's an example:

What do you do now?
Well, it really depends on several factors. The first question is, do you have the said product installed? In this case, do you have the Adobe Flash Player installed. If the answer is yes, then this request is quite likely legitimate. But if you do not, then you should think twice.
Moreover, there are different scenarios where you might see this kind of prompt. For example, while browsing, just after reboot, etc. Does the prompt show in the context of a running program or does it show on your desktop?
There is no golden rule. But my recommendation is like this:
Do not to agree to any installation prompts by plugins, add-ons or other utilities that do not run on their own. Instead, you should go to the official websites and download the necessary software update manually.
The same applies for plugin updates that you sometimes see in the browser. While most websites will offer legitimate content, you should not risk it. For example, Quake Live is an excellent website. Nevertheless, you should go to Adobe website on your own, download the Flash Player install it, then reload the website and enjoy the contents.

What about programs with built-in updaters?
These are rather safe to use. For example, Firefox will prompt you to update periodically, so will Opera, FileZilla, Notepad++, and other programs. Since these are self-contained programs with built-in self-update features, these prompts are to be expected.


What can go wrong?
Well, it is possible that certain websites might try to convince you into downloading and running software that you do not really want or need. There exist specially crafted webpages that look like a typical folder view in Windows Explorer, the Control Panel or show an animated view of a software scan in progress, displayed inside a browser window, yet aimed at convincing the user the action is taking place on their machine.
These websites use pure social engineering. Many people are too scared to rationalize what they see, often buying into frightening animations of scans with multiple problems found and eventually buying software that is meant to solve problems that did not exist in the first place.
Handling this kind of phenomenon is not easy. It takes software intelligence, which many people do not have, thus turning each and every popup into a potential risk of getting swindled, duped, infected, or whatnot.
Therefore, I suggest you update software at the time and place of your choosing. If you fear being distracted by browser popups, close your browsers before running any updates or open fresh instances of browsers, if the updates are browser-related, this way you will know that popups you see come from your own software. Knowing what programs you have installed helps too.
Mini-summary
You will get many more prompts for updates from your software: Java updates, Flash updates, Acrobat Reader updates, Firefox updates, and many others. In most cases, the requests will be completely legitimate and beneficial for you.
Sometimes you may get offers for updates and downloads you did not quite expect. If you're not really sure, then cancel the update. Remember, built-in updates are there for your convenience. They do not replace the old fashioned method of downloading manually from the vendor and running the installer.
If you suspect the prompts you're seeing are fraudulent and are not quite what they ought to be, do not agree to them, close them and perform the updates manually. Every program that I know of has the ability to perform the manual update checks. Nothing will happen if you temporarily delay the updates.
User Access Control (UAC) prompts
Windows Vista and Windows 7 have a security mechanism called UAC, which elevates privileges for the execution of system administration tasks, like changing of system settings and installation of software.
If you run one of these operating systems with UAC enabled, you will see security prompts now and then. Like with software updates, the same rules apply here. If you did not ask for it, do not expect it or you think it might be bad, do not accept it. As simple as that.
Here's an example:
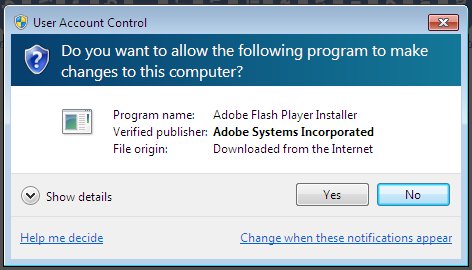
This prompt originated while browsing the Internet. It's an attempt to install the missing Adobe Flash Player. Did you trigger this installation? No? Then click No and continue working normally.
UAC is there to stop unsolicited requests, but it can't stop the users from hurting themselves, should they be so inclined. If you click Yes, the security of your setup might be undermined. Think carefully before making the decision. You can always click Yes later.
For more about UAC, please check my Windows 7 security guide.
Limited User Account (LUA) prompts
By default, Windows XP LUA does not offer any helpful hints to the user. At most, you will probably see generic messages informing you that you must be an administrator to run the program.

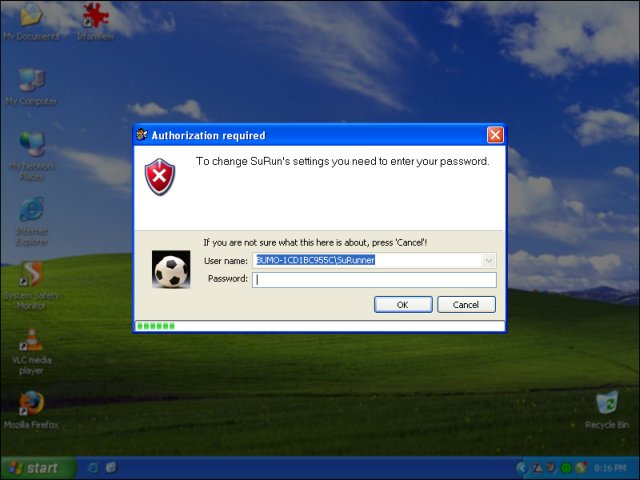
But if you're running SuRun, you'll enjoy a powerful privilege management mechanism, similar to SUDO in Linux. Like UAC, SuRun will alert you whenever a program/utility/plugin is trying to elevate its privileges.

You will also get helpful hints in the System Tray, telling you of the utilities running with elevated privileges.


Pay attention to the prompt above. It's a prompt by Java Quick Starter, which is running as a browser plugin in Firefox. This plugin wants elevated rights.
This is something that will happen often: one or the browser components will try to run an update, like Flash, like Java, or perform an operation that requires privileges that are higher than what it currently has. If you've just started your browser and deliberately permitted these requests, then there's nothing to worry about. But would you okay a request if you did not expect it?
It's simple. Here's an example:

Afraid? No problem. Deny the request. You will always have the chance to repent later. Programs are like salesmen. They will never say no when you come back to them.
You can always try to run the problematic program manually, with elevated privileges and perform the step that requires the administrator rights. Make sure you do that at the moment of your choosing, with no unhappy thoughts clouding your mind.

Data Execution Prevention prompts
Data Execution Prevention (DEP) is a seriously overlooked aspect of the Windows security. Buried deep in the menus, it's a mechanism that should prevent applications from using memory that does not belong to them.
Badly coded or malicious applications can try to access portions of memory outside their allocation, which would then enable them to run arbitrary code and maybe even cause damage. On modern Windows platforms, DEP is enabled only for core system utilities, but you can extend the functionality to encompass all programs. This will force the applications to work within the boundaries of their allocations and if they try to use more, crash them.
It's functionality versus security.


Using DEP should be transparent for most people. You should definitely use it, at least for the essential Windows programs and services. But if you care to make your system less vulnerable to shenanigans, then you may want to enable DEP for all programs.
DEP will do its magic in the background; sometimes you may see a prompt:

What should you do?
Well, nothing. Think twice about what you just tried to do and try to understand what it was that your machine did not like and avoid repeating that in the future. But in general, you're okay. Your system is functioning properly and doing what is supposed to do.
Firewall prompts
Windows firewall
Windows firewall will not bother you unless you try to start a service. In plain English, services are programs that also have an open network connection. When this happens, Windows firewall will jump into action and warn you:

By default, it will block the connection. You will have to examine the prompt and decide whether this program is something you have consciously, deliberately started yourself and whether you want to let it open a port. If you are not sure, then select Keep Blocking, otherwise click Unblock to permit the full functionality required by the program.
Other firewalls
If you're running a software firewall other than the Windows firewall, you'll often get a few warnings now and then, asking you to confirm or deny this or that connection. If you don't have any understanding how firewalls work, you'll probably be frustrated and maybe even a little afraid, thinking your machine is trying to phone home, send your data to a hacker and who knows what else.
Here's a typical prompt:

Wow, what now?
How do you handle something like this? Answer: very tricky.
First, ask me what were you doing when that thing came up. The answer is, I was trying to install something. So, it does NOT come as a surprise that you get the prompt. Some programs, especially those using Microsoft Software Installer (MSI), sometimes try to contact the vendor's server to check the digital signature and the hash of the downloaded file before invoking the installation process. Perfectly normally and nothing to be afraid of.
But what if you got this kind of alert when just doing simply stuff, like, let's say, browsing a website? What should you do?
Now comes the geek part. You really need to understand the prompts to be able to answer properly. There are three major components in every firewall prompt:
- The application (process) name
- The remote address
- The remote port
If you do not recognize the application (process) name and cannot pair it with one of the programs you're running, you will be hard pressed to make the right choice. The best thing to do in this case is to deny the connection attempt, but make it a one-time choice. All software firewall have the option to "remember" your answer, so you're not nagged with repeated requests. Make a single deny and observe. Did you lose functionality?
The remote address won't tell you much. However, in a few cases, you will be able to make an instant decision.
The remote address 127.0.0.1 is your own computer. This address is called the loopback. When an application asks for the permission to access this address, this means that one of the sub-processes of that application is trying to open a socket. Do not ask what that means. But this will allow the application to communicate with other processes on your machine, i.e. loop back.
Another safe address is 0.0.0.0, also known as the default gateway. Any process that wants to communicate with the external world must sends its data somewhere. In most cases, the data will be sent to the default gateway, a network device that handles all traffic that has not known destination. In other words, any bit of network traffic is not specifically sent to one of the network devices on your machine eventually routed to the default gateway.
When you see a prompt for an application/process asking to connect to the default gateway, this means that it is trying to communicate with the external world. This does not tell us anything yet. But if you allow the process to access the gateway, you will see yet another prompt soon thereafter, this time with the actual remote address and the destination port.
Please note that applications asking for loopback access do not necessarily need access to the external world (local network, Internet, etc). But they might. So you may see even as many as three separate prompts for one process and maybe even more.
Another possible set of "friendly" remote addresses are various addresses on your local network. For example, 172.16.x.x, 192.168.x.x, 10.x.x.x are all IP addresses that belong to local networks. If you're a member of one such network and you trust other machines connected to this grid, then you should not have any problems allowing outbound connections to these hosts.
However, other than the loopback, the default gateway and a few LAN addresses, the average user won't really know what's waiting at the remote destination. It is possible to run all sorts of queries, trying to determine who the IP address belongs to, but this is a rather geeky thing and beyond the skills of the average user.
Now, the remote port tell us, more or less, the type of communication the process is trying to establish. Most of the network traffic in the world, including the Internet, uses well-known ports, allowing for easier connectivity and troubleshooting of problems. This can help us better understand what is happening.
There are tons of ports, used for all sorts of purposes. If you do not know what which ports represents, then you will have a hard time making the right choice.
Mini-summary
Identifying the nature of the process asking for an outbound connection requires that you be able to make three educated guesses about what's happening.
Do not use firewalls with outbound control if you do not understand what's going on. If there's a doubt, there's no doubt. Deny. This can cost you the loss of connectivity, but you must make the decision whether you need or want to use firewalls with outbound control and understand the implications of added security/hassle this setup introduces.
For the average user, firewall prompts are too difficult to answer. The average user cannot make the right choice when faced with a connection prompt.
Here's another example:

Did you just launch this program? If you did not, what do you do?
Setting up firewalls with outbound control can take weeks, sometimes longer. There will always come a moment when a new program will be added to your list and it will then ask for permission to connect to Internet or something similar. And you will have to be able to make the right choice. Not feasible for 99% of people.
But the magic thing is: if you ARE using outbound firewalls, and you get an unexpected request for connection, DENY it and observe the system behavior. It requires discipline and knowledge, so you'll have to make the right decision.
Conclusion
I hope you really liked this article. I believe it's made the entire mess of Windows security management a little less confusing. There are no easy decisions to be made, but at least we now understand the basics of how things ought to be run.
The most important thing to remember: do not be tempted to click Yes just because there's a lot going on on your monitor. Analyze the situation. Even if you do not fully understand the prompts, you can follow the most basic checklist. Did I initiate that? Did I ask for that? Is there a doubt? If the answer is yes to any of these questions, you should deny the requests and retry at a later stage.
In this guide, we've learned to discern several principal groups of security alerts, focusing around privileges, software updates and network connectivity. The most difficult aspect is definitely the firewall management, but you can avoid it by not using outbound control.
But what about the applications installed on the machine? Won't they phone home? Well, the simple answer is no. If you install programs you trust and follow a healthy doctrine of avoiding unnecessary installations, especially when not asked for, there won't be any gremlins inside your box. You should be fine.
Oh, you may have noticed I did not include anti-virus programs or similar software in the list. The simple reason is, if you follow the advice mentioned above, you do not need any extras.
We now have the tools to make the right choices. Happy computing!
More reading: Windows 7 security and Safe Web practices. See ya around!
Cheers.